2017-02-18 22:31:11 +00:00
|
|
|
# Wordpresscan
|
2017-02-27 14:51:35 +00:00
|
|
|
A simple Wordpress scanner written in python based on the work of WPScan (Ruby version)
|
2017-02-18 22:31:11 +00:00
|
|
|
|
2017-02-25 00:36:59 +00:00
|
|
|
## Disclaimer
|
|
|
|
|
```
|
|
|
|
|
The author of this github is not responsible for misuse or for any damage that you may cause!
|
|
|
|
|
You agree that you use this software at your own risk.
|
|
|
|
|
```
|
|
|
|
|
|
2017-02-25 22:48:28 +00:00
|
|
|
|
2017-02-18 22:31:11 +00:00
|
|
|
## Install & Launch
|
2017-03-03 13:25:06 +00:00
|
|
|
Dependencies
|
2017-03-03 13:24:07 +00:00
|
|
|
```
|
|
|
|
|
pip install requests
|
|
|
|
|
pip install tornado
|
|
|
|
|
```
|
|
|
|
|
|
2017-03-03 13:25:06 +00:00
|
|
|
Install
|
2017-02-23 11:00:48 +00:00
|
|
|
```bash
|
2017-02-18 22:31:11 +00:00
|
|
|
git clone https://github.com/swisskyrepo/Wordpresscan.git
|
|
|
|
|
cd Wordpresscan
|
2017-06-10 18:58:40 +00:00
|
|
|
```
|
|
|
|
|
|
|
|
|
|
Example 1 : Basic update and scan of a wordpress
|
|
|
|
|
```
|
2017-03-05 15:58:15 +00:00
|
|
|
python main.py -u "http://localhost/wordpress" --update --random-agent
|
2017-03-03 13:27:54 +00:00
|
|
|
|
2017-02-27 14:50:11 +00:00
|
|
|
-u : Url of the WordPress
|
|
|
|
|
--update : Update the wpscan database
|
|
|
|
|
--aggressive : Launch an aggressive version to scan for plugins/themes
|
2017-03-05 15:58:15 +00:00
|
|
|
--random-agent : Use a random user-agent for this session
|
2017-02-25 00:36:59 +00:00
|
|
|
```
|
|
|
|
|
|
2017-06-10 18:58:40 +00:00
|
|
|
Example 2 : Basic bruteforce
|
|
|
|
|
```
|
|
|
|
|
python main.py -u "http://127.0.0.1/wordpress/" --brute fuzz/wordlist.lst
|
|
|
|
|
python main.py -u "http://127.0.0.1/wordpress/" --brute admin
|
|
|
|
|
|
|
|
|
|
--brute file.lst : Will bruteforce every username and their password
|
|
|
|
|
--brute username : Will bruteforce the password for the given username
|
|
|
|
|
it will also try to bruteforce the password for the detected users.
|
|
|
|
|
```
|
|
|
|
|
|
|
|
|
|
Example 3 : Thinking is overrated, this is aggressive, mostly not advised!
|
|
|
|
|
```
|
|
|
|
|
python main.py -u "http://127.0.0.1/wordpress/" --fuzz
|
|
|
|
|
|
|
|
|
|
[i] Enumerating components from aggressive fuzzing ...
|
|
|
|
|
[i] File: http://127.0.0.1/wordpress/license.txt - found
|
|
|
|
|
[i] File: http://127.0.0.1/wordpress/readme.html - found
|
|
|
|
|
[i] File: http://127.0.0.1/wordpress/wp-admin/admin-footer.php - found
|
|
|
|
|
[i] File: http://127.0.0.1/wordpress/wp-admin/css/ - found
|
|
|
|
|
[i] File: http://127.0.0.1/wordpress/wp-admin/admin-ajax.php - found
|
|
|
|
|
[i] File: http://127.0.0.1/wordpress/wp-activate.php - found
|
|
|
|
|
--fuzz : Will fuzz the website in order to detect as much file, themes and plugins as possible
|
|
|
|
|
```
|
|
|
|
|
|
2017-02-25 22:54:00 +00:00
|
|
|
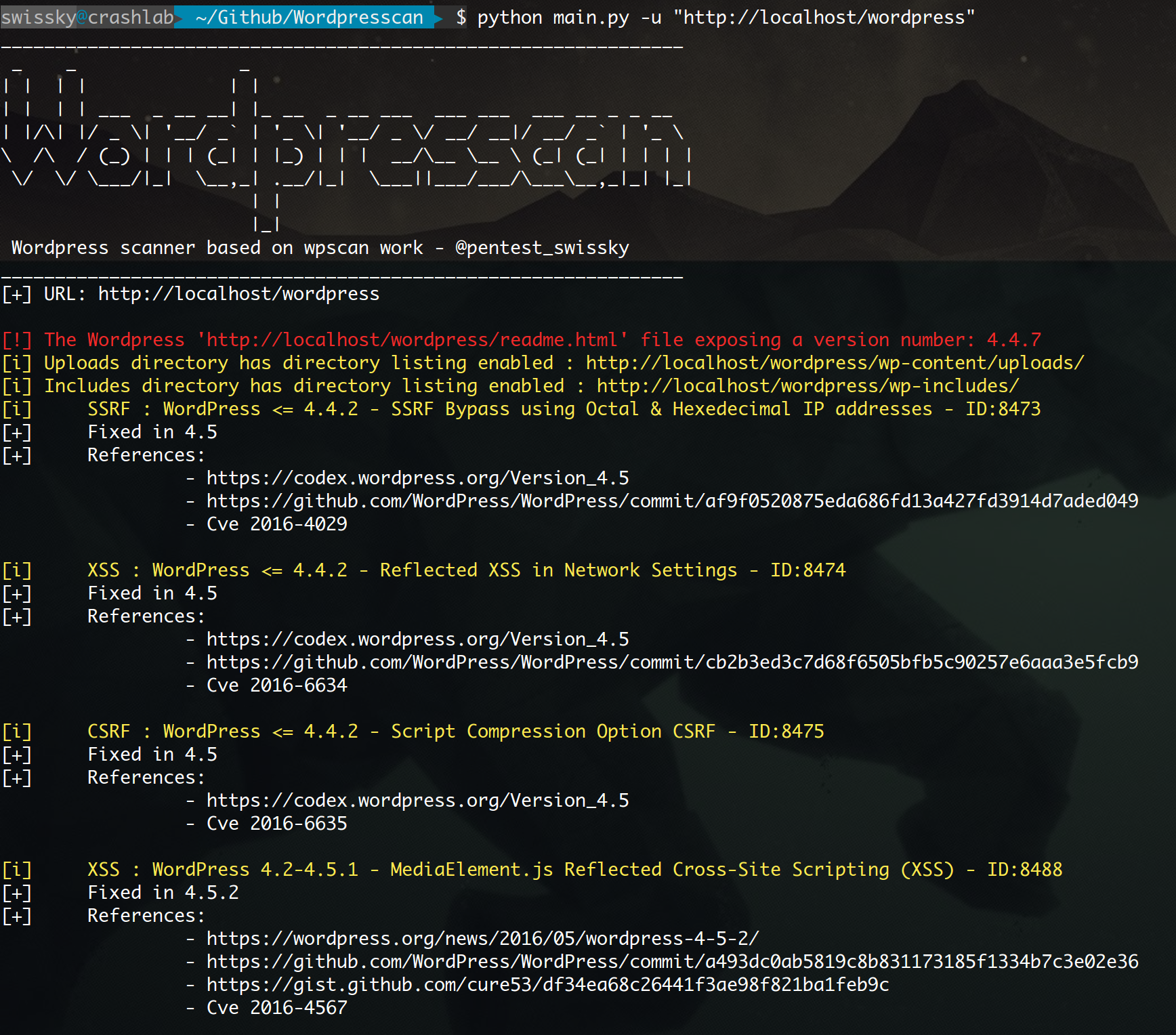
## Output example from a test environment
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
2017-02-25 00:36:59 +00:00
|
|
|
## Credits and Contributor
|
2017-06-10 18:58:40 +00:00
|
|
|
* Original idea and script from [WPScan Team](https://wpscan.org/)
|