|
|
||
|---|---|---|
| CONTRIBUTING.md | ||
| ISSUE_TEMPLATE.md | ||
| LICENSE | ||
| PULL_REQUEST_TEMPLATE.md | ||
| README.md | ||
README.md
__ __ __ __
/ / / /___ ______/ /_____ _____ _________ ____ _____/ /___ ___ ____ _____
/ /_/ / __ `/ ___/ //_/ _ \/ ___/_____/ ___/ __ \/ __ `/ __ / __ `__ \/ __ `/ __ \
/ __ / /_/ / /__/ ,< / __/ / /_____/ / / /_/ / /_/ / /_/ / / / / / / /_/ / /_/ /
/_/ /_/\__,_/\___/_/|_|\___/_/ /_/ \____/\__,_/\__,_/_/ /_/ /_/\__,_/ .___/
/_/
This repository is a guide for amateurs pen testers and a summary of hacking tools, resources and references to practice ethical hacking, pen testing and web security. Most of these tools are UNIX compatible and MIT licensed. Note that Linux is the best operating system to practice ethical hacking.
Summary
Introduction
What is penetration testing ?
Penetration testing is a type of security testing that is used to test the insecurity of an application. It is conducted to find the security risk which might be present in the system.
If a system is not secured, then any attacker can disrupt or take authorized access to that system. Security risk is normally an accidental error that occurs while developing and implementing the software. For example, configuration errors, design errors, and software bugs, etc. Learn more
Want to become a penetration tester ?
Know about risks on the internet and how they can be prevented is very useful. Especially as a developer. Web hacking and penetration testing is the v2.0 of self-defense! But does know about tools and how to use them is really all you need to become a pen tester? Surely not. A real penetration tester must be able to proceed rigorously and detect the weaknesses of an application. He must be able to identify the technology behind and test every single door that might be open to hackers.
This repository aim first to establish a reflection method on penetration testing and explain how to proceed to secure an application. And secondly, to regroup all kind of tools or resources pen testers need. Be sure to know basics of programming languages and Internet security before learning pen testing.
Some vocabulary
Black/grey/white hat hacker : Someone who uses bugs or exploits to break into systems or applications. The goal and the method differs depending if he's a black, grey or white hat hacker. A black hat is just someone malicious that does not wait permission to break into a system or application. A white hat is usually a security researcher who practice ethical hacking. A grey hat is just in the middle of these two kind of hackers, he might want to be malicious if it can be benefit (data breach, money, whistleblowing ...).
Penetration tester : Most likely a white hacker who test applications and systems to secure them or find vulnerabilities.
Security researcher : Someone who practice pen testing and browse the web everyday to find phishing/fake websites, infected servers, bugs or vulnerabilities. He can work for a company so he's responsible for the security of systems.
Difference between hacking and ethical hacking
A black hat is practicing penetration testing, but unlike a white hat, this is not ethical hacking. Ethical hacking is about find vulnerabilities and improve the security of a system. An ethical hacker is the ultimate security professional. Ethical hackers know how to find and exploit vulnerabilities and weaknesses in various systems, just like a malicious hacker (a black hat hacker). In fact, they both use the same skills; however, an ethical hacker uses those skills in a legitimate, lawful manner to try to find vulnerabilities and fix them before the bad guys can get there and try to break in. An ethical hacker is basically a white hat hacker.
Languages
- Python
- Ruby
- C / C++ / C#
- Perl
- Go
- Java
Content Management Systems
- Wordpress
- Joomla
- Drupal
- SPIP
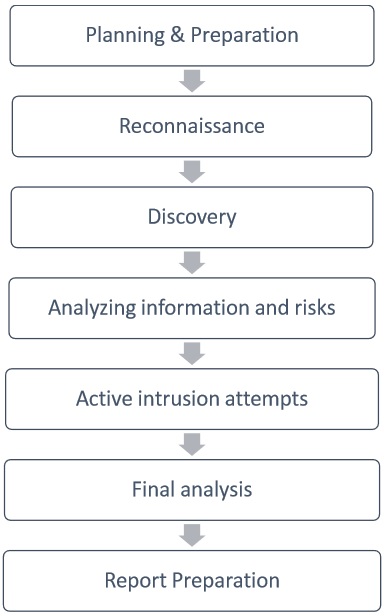
Basic steps of pen testing
Tools by category
🕵️♂️ Information Gathering
Information Gathering tools allows you to collect host metadata about services and users. Check informations about a domain, IP address, phone number or an email address.
- Th3inspector Perl |
Linux/Windows/macOS| All in one tool for Information Gathering written in Perl. - Crips Python |
Linux/Windows/Android| IP Tools To quickly get information about IP Address's, Web Pages and DNS records. - theHarvester Python |
Linux/Windows/macOS| E-mails, subdomains and names Harvester. - Scanless Python |
Linux/Windows/macOS| Online port scan scraper. - CTFR Python |
Linux/Windows/macOS| Abusing Certificate Transparency logs for getting HTTPS websites subdomains. - Sn1per bash |
Linux/macOS| Automated Pentest Recon Scanner - ReconDog Python |
Linux/Windows/macOS| Recon Dog is an all in one tool for all your basic information gathering needs. - RED Hawk PHP |
Linux/Windows/macOS| All in one tool for Information Gathering, Vulnerability Scanning and Crawling. A must have tool for all penetration testers. - Infoga Python |
Linux/Windows/macOS| Email Information Gathering. - KnockMail Python |
Linux/Windows/macOS| Check if email address exists.
🔒 Password Attacks
Crack passwords and create wordlists.
- John the Ripper C |
Linux/Windows/macOS| John the Ripper is a fast password cracker. - hashcat C |
Linux/Windows/macOS| World's fastest and most advanced password recovery utility. - Hydra C |
Linux/Windows/macOS| Parallelized login cracker which supports numerous protocols to attack. - ophcrack C++ |
Linux/Windows/macOS| Windows password cracker based on rainbow tables. - Ncrack C |
Linux/Windows/macOS| High-speed network authentication cracking tool.
📝 Wordlists
- Probable Worlist | Wordlists sorted by probability originally created for password generation and testing.
🌐 Wireless Testing
Used for intrusion detection and wifi attacks.
- Aircrack C |
Linux/Windows/macOS| WiFi security auditing tools suite. - bettercap Go |
Linux/Windows/macOS/Android| bettercap is the Swiss army knife for network attacks and monitoring. - WiFi Pumpkin Python |
Linux/Windows/macOS/Android| Framework for Rogue Wi-Fi Access Point Attack. - Airgeddon Shell |
Linux/Windows/macOS| This is a multi-use bash script for Linux systems to audit wireless networks. - Airbash C |
Linux/Windows/macOS| A POSIX-compliant, fully automated WPA PSK handshake capture script aimed at penetration testing.
🔧 Exploitation Tools
Acesss systems and data with service-oriented exploits.
- SQLmap Python |
Linux/Windows/macOS| Automatic SQL injection and database takeover tool. - XSStrike Python |
Linux/Windows/macOS| Advanced XSS detection and exploitation suite.
👥 Sniffing & Spoofing
Listen to network traffic or fake a network entity.
- Wireshark C/C++ |
Linux/Windows/macOS| Wireshark is a network protocol analyzer. - WiFi Pumpkin Python |
Linux/Windows/macOS/Android| Framework for Rogue Wi-Fi Access Point Attack.
🚀 Web Hacking
Exploit popular CMSs that are hosted online.
- WPScan Ruby |
Linux/Windows/macOS| WPScan is a black box WordPress vulnerability scanner. - Droopescan Python |
Linux/Windows/macOS| A plugin-based scanner to identify issues with several CMSs, mainly Drupal & Silverstripe. - Joomscan Perl |
Linux/Windows/macOS| Joomla Vulnerability Scanner. - Drupwn Python |
Linux/Windows/macOS| Drupal Security Scanner to perform enumerations on Drupal-based web applications.
⚡ Private Web Hacking
Access files and databases.
...
🎉 Post Exploitation
Exploits for after you have already gained access.
- TheFatRat Java |
Linux/Windows/macOS| Easy tool to generate backdoor and easy tool to post exploitation attack like browser attack, dll. - Microsploit Shell |
Linux/Windows/macOS| Fast and easy create backdoor office exploitation using module metasploit packet , Microsoft Office , Open Office , Macro attack , Buffer Overflow.
📦 Frameworks
Frameworks are packs of pen testing tools with custom shell navigation and documentation.
- Operative Framework Python |
Linux/Windows/macOS| Framework based on fingerprint action, this tool is used for get information on a website or a enterprise target with multiple modules. - Metasploit Ruby |
Linux/Windows/macOS| A penetration testing framework for ethical hackers. - fsociety Python |
Linux/Windows/macOS| fsociety Hacking Tools Pack – A Penetration Testing Framework. - cSploit Java |
Android| The most complete and advanced IT security professional toolkit on Android. - radare2 C |
Linux/Windows/macOS/Android| Unix-like reverse engineering framework and commandline tools. - Social Engineer Toolkit Python |
Linux/macOS| Penetration testing framework designed for social engineering. - hate_crack Python |
Linux/macOS| A tool for automating cracking methodologies through Hashcat. - Wifiphisher Python |
Linux| The Rogue Access Point Framework. - Kickthemout Python |
Linux/macOS| Kick devices off your network by performing an ARP Spoof attack.
Additional resources
- Devbreak on Twitter Twitter Bot that post articles about security, hacking, opensource, dev, webdesign and more.
- The Life of a Security Researcher
- Find an awesome hacking spots in your country
- Awesome Infosec
Books / Manuals
Warning : I haven't read them all so don't consider I am recommanding as I liked them. They just seems to provide useful resources.
- Blue Team Field Manual (BTFM)
- Cybersecurity - Attack and Defense Strategies
- NMAP Network Scanning : Official Discovery
- Social Engineering : The Art of Human Hacking
- Incognito Toolkit: Tools, Apps, and Creative Methods for Remaining Anonymous
Discussions
- Reddit/HowToHack Learn and ask about hacking, security and pen testing.
- Reddit/hacking Discuss about hacking and web security.
- ax0nes Hacking, security, and software development forum.
- 0Day.rocks on discord Discord server about the 0day.rocks blog for technical and general InfoSec/Cyber discussions & latest news.
License
This repository is under MIT license.



