|
|
||
|---|---|---|
| editor | ||
| sample-data | ||
| threat-actor-data | ||
| .dockerignore | ||
| .gitignore | ||
| Dockerfile | ||
| LICENSE | ||
| README.md | ||
| constants.py | ||
| data_source_mapping.py | ||
| dettect.py | ||
| editor.py | ||
| eql_yaml.py | ||
| generic.py | ||
| group_mapping.py | ||
| health.py | ||
| interactive_menu.py | ||
| requirements.txt | ||
| scoring_table.xlsx | ||
| technique_mapping.py | ||
| upgrade.py | ||
README.md

Detect Tactics, Techniques & Combat Threats
Latest version: 1.3
To get started with DeTT&CT, check out this page, our talk at hack.lu 2019 and our blog on:
- mbsecure.nl/blog/2019/5/dettact-mapping-your-blue-team-to-mitre-attack or
- siriussecurity.nl/blog/2019/5/8/mapping-your-blue-team-to-mitre-attack.
DeTT&CT aims to assist blue teams using ATT&CK to score and compare data log source quality, visibility coverage, detection coverage and threat actor behaviours. All of which can help, in different ways, to get more resilient against attacks targeting your organisation. The DeTT&CT framework consists of a Python tool, YAML administration files, the DeTT&CT Editor and scoring tables for the different aspects.
DeTT&CT provides the following functionality:
- Administrate and score the quality of your data sources.
- Get insight on the visibility you have on for example endpoints.
- Map your detection coverage.
- Map threat actor behaviours.
- Compare visibility, detections and threat actor behaviours to uncover possible improvements in detection and visibility. This can help you to prioritise your blue teaming efforts.
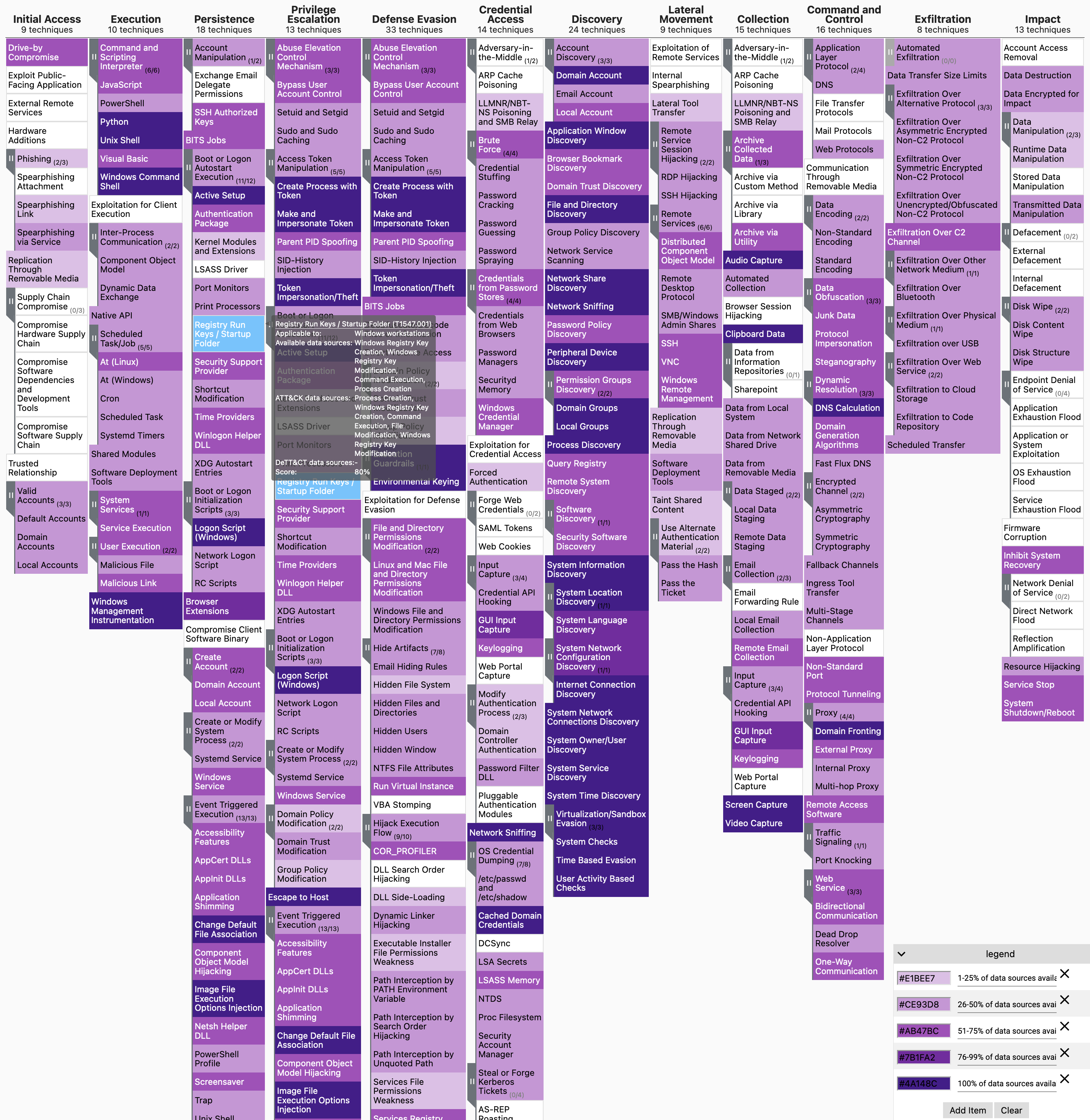
The coloured visualisations are created with the help of MITRE's ATT&CK™ Navigator.
Authors and contributions
This project is developed and maintained by Marcus Bakker (Twitter: @bakk3rm) and Ruben Bouman (Twitter: @rubenb_2). Feel free to contact, DMs are open.
We welcome contributions! Contributions can be both in code, as well as in ideas you might have for further development, usability improvements, etc.
Work of others
Some functionality within DeTT&CT was inspired by the work of others:
- Roberto Rodriguez's work on data quality and scoring of MITRE ATT&CK™ techniques (How Hot Is Your Hunt Team?, Ready to hunt? First, Show me your data!).
- The MITRE ATT&CK Mapping project on GitHub: https://github.com/siriussecurity/mitre-attack-mapping.
Example
YAML files are used for administrating scores and relevant metadata. All of which can be visualised by loading JSON layer files into the ATT&CK Navigator (some types of scores and metadata can also be written to Excel).
See below an example of mapping your data sources to ATT&CK, which gives you a rough overview of your visibility coverage:
Installation and requirements
See our GitHub Wiki: Installation and requirements.