Merge pull request #16 from Ice3man543/codingo-readme-updates
Documentation Changes / Addition of Sourcesmaster
commit
a649966c94
148
README.md
148
README.md
|
|
@ -7,13 +7,13 @@ SubFinder is a subdomain discovery tool that uses various techniques to discover
|
|||
|
||||
[](https://asciinema.org/a/177851)
|
||||
|
||||
## Why?
|
||||
# Why?
|
||||
|
||||
This project began it's life as a Bug Bounty World slack channel discussion. We were talking about how the cornerstone subdomain tool at the time, sublist3r, appeared to have been abandoned. The goal of this project was to make a low dependancy, manageable project in Go that would continue to be maintained over time. I decided to rewrite the sublist3r project and posted about it. @codingo offered to contribute to the project and subfinder was born.
|
||||
|
||||
So finally after working hard, here is something that I hope you guys will :heart:.
|
||||
|
||||
## Features
|
||||
# Features
|
||||
|
||||
- Simple and modular code base making it easy to contribute.
|
||||
- Fast And Powerful Bruteforcing Module (In Development)
|
||||
|
|
@ -21,67 +21,28 @@ So finally after working hard, here is something that I hope you guys will :hear
|
|||
- Many Passive Data Sources (CertDB, CertSpotter, crtsh, DNSDumpster, FindSubdomains, Hackertarget, Netcraft, PassiveTotal, PTRArchive, SecurityTrails, Threatcrowd, VirusTotal, Waybackarchive, Threatminer, Riddler)
|
||||
- Multiple Output formats
|
||||
|
||||
## Install
|
||||
## Sources
|
||||
|
||||
### Direct
|
||||
The installation is easy. Git clone the repo and run go build.
|
||||
| Source | Usage |
|
||||
|---------------- |-------------- |
|
||||
| Ask | Natively |
|
||||
| CertDB | Natively |
|
||||
| Certspotter | Natively |
|
||||
| Crtsh | Natively |
|
||||
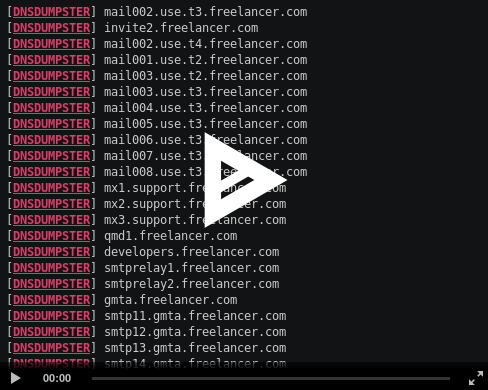
| DNSdumpster | Natively |
|
||||
| Findsubdomains | Natively |
|
||||
| Hackertarget | Natively |
|
||||
| Netcraft | Natively |
|
||||
| Passivetotal | With API key |
|
||||
| Ptrarchive | Natively |
|
||||
| Riddler | Natively |
|
||||
| Securitytrails | With API key |
|
||||
| Threatcrowd | Natively |
|
||||
| Threatminer | Natively |
|
||||
| Virustotal | With API key |
|
||||
| Waybackarchive | Natively |
|
||||
|
||||
```bash
|
||||
go get github.com/ice3man543/subfinder
|
||||
```
|
||||
|
||||
### Docker
|
||||
|
||||
Git clone the repo, then build and run subfinder in a container with the following commands
|
||||
|
||||
- Clone the repo using `git clone https://github.com/ice3man543/subfinder.git`
|
||||
- Build your docker container
|
||||
```bash
|
||||
docker build -t subfinder .
|
||||
```
|
||||
|
||||
- After building the container, run the following.
|
||||
```bash
|
||||
docker run -it subfinder
|
||||
```
|
||||
> The above command is the same as running `-h`
|
||||
|
||||
##### NOTE: Please follow the Post Install steps given after this to correctly configure the tool.
|
||||
|
||||
For example, this runs the tool against uber.com and output the results to your host file system:
|
||||
```bash
|
||||
docker run -v $HOME/.config/subfinder:/root/.config/subfinder -it subfinder -d uber.com > uber.com.txt
|
||||
```
|
||||
|
||||
### Post Install
|
||||
|
||||
To configure it to work with certain services, you need to have an API key for them. These are the services that do not work without an API key.
|
||||
|
||||
- [Virustotal](https://www.virustotal.com/)
|
||||
- [Passivetotal](http://passivetotal.org/)
|
||||
- [SecurityTrails](http://securitytrails.com/)
|
||||
|
||||
Theses values are stored in the $HOME/.config/subfinder/config.json file which will be created when you run the tool for the first time. To configure the services to use an API key, you need to use the tool with --set-config option which will allow you to set a configuration option.
|
||||
|
||||
```bash
|
||||
./subfinder --set-config VirustotalAPIKey=0x41414141
|
||||
./subfinder --set-config PassivetotalUsername=hacker,PassivetotalKey=supersecret
|
||||
```
|
||||
|
||||
If you are using docker, you need to first create your directory structure holding subfinder configuration file. You can either run the binary in your host system and let it create the directory structure of files, after which you can use --set-config flag to set the api values like before. Or you can run -
|
||||
```bash
|
||||
mkdir $HOME/.config/subfinder
|
||||
cp config.json $HOME/.config/subfinder/config.json
|
||||
nano $HOME/.config/subfinder/config.json (optional)
|
||||
```
|
||||
After that, you can pass it as a volume using the following sample command.
|
||||
|
||||
```bash
|
||||
sudo docker run -v $HOME/.config/subfinder:/root/.config/subfinder -it subfinder -d freelancer.com
|
||||
```
|
||||
Now, you can also pass --set-config inside the docker to change the configuration options.
|
||||
|
||||
## Usage
|
||||
# Usage
|
||||
|
||||
```bash
|
||||
./subfinder -h
|
||||
|
|
@ -105,13 +66,64 @@ This will display help for the tool. Here are all the switches it supports.
|
|||
| -v | Display verbose output | ./subfinder -v |
|
||||
| -w | Wordlist for doing bruteforcing and permutation | ./subfinder -w words.txt |
|
||||
|
||||
## NOTE
|
||||
This tool is currently in active development. So some features may not work or maybe broken. Please do a PR or create an Issue for any features, suggestions or ideas. Would love to hear from you guys.
|
||||
# Installation Instructions
|
||||
## Direct Installation
|
||||
The installation is easy. Git clone the repo and run go build.
|
||||
|
||||
## Acknowledgements
|
||||
```bash
|
||||
go get github.com/ice3man543/subfinder
|
||||
```
|
||||
|
||||
## Running in a Docker Container
|
||||
|
||||
Git clone the repo, then build and run subfinder in a container with the following commands
|
||||
|
||||
- Clone the repo using `git clone https://github.com/ice3man543/subfinder.git`
|
||||
- Build your docker container
|
||||
```bash
|
||||
docker build -t subfinder .
|
||||
```
|
||||
|
||||
- After building the container, run the following.
|
||||
```bash
|
||||
docker run -it subfinder
|
||||
```
|
||||
> The above command is the same as running `-h`
|
||||
|
||||
***NOTE: Please follow the Post Install steps given after this to correctly configure the tool.***
|
||||
|
||||
For example, this runs the tool against uber.com and output the results to your host file system:
|
||||
```bash
|
||||
docker run -v $HOME/.config/subfinder:/root/.config/subfinder -it subfinder -d uber.com > uber.com.txt
|
||||
```
|
||||
|
||||
## Post Installation Instructions
|
||||
|
||||
Subfinder will work after using the installation instructions however to configure Subfinder to work with certain services, you will need to have setup API keys. These following services do not work without an API key:
|
||||
|
||||
- [Virustotal](https://www.virustotal.com/)
|
||||
- [Passivetotal](http://passivetotal.org/)
|
||||
- [SecurityTrails](http://securitytrails.com/)
|
||||
|
||||
Theses values are stored in the $HOME/.config/subfinder/config.json file which will be created when you run the tool for the first time. To configure the services to use an API key, you need to use the tool with --set-config option which will allow you to set a configuration option. For example:
|
||||
|
||||
```bash
|
||||
./subfinder --set-config VirustotalAPIKey=0x41414141
|
||||
./subfinder --set-config PassivetotalUsername=hacker,PassivetotalKey=supersecret
|
||||
```
|
||||
|
||||
If you are using docker, you need to first create your directory structure holding subfinder configuration file. You can either run the binary in your host system and let it create the directory structure of files, after which you can use --set-config flag to set the api values like before. Or you can run:
|
||||
```bash
|
||||
mkdir $HOME/.config/subfinder
|
||||
cp config.json $HOME/.config/subfinder/config.json
|
||||
nano $HOME/.config/subfinder/config.json (optional)
|
||||
```
|
||||
After that, you can pass it as a volume using the following sample command.
|
||||
```bash
|
||||
sudo docker run -v $HOME/.config/subfinder:/root/.config/subfinder -it subfinder -d freelancer.com
|
||||
```
|
||||
Now, you can also pass --set-config inside the docker to change the configuration options.
|
||||
|
||||
# Acknowledgements
|
||||
|
||||
- @FranticFerret for his work on adding docker support.
|
||||
|
||||
## License
|
||||
|
||||
MIT License
|
||||
|
|
|
|||
Loading…
Reference in New Issue