Read ignore file from current working directory |
||
|---|---|---|
| .github | ||
| static | ||
| v2 | ||
| .gitignore | ||
| .golangci.yml | ||
| .goreleaser.yml | ||
| Dockerfile | ||
| LICENSE.md | ||
| README.md | ||
| THANKS.md | ||
README.md
Nuclei is a fast tool for configurable targeted scanning based on templates offering massive extensibility and ease of use.
Nuclei is used to send requests across targets based on a template leading to zero false positives and providing effective scanning for known paths. Main use cases for nuclei are during initial reconnaissance phase to quickly check for low hanging fruits or CVEs across targets that are known and easily detectable. It uses retryablehttp-go library designed to handle various errors and retries in case of blocking by WAFs, this is also one of our core modules from custom-queries.
We have also open-sourced a template repository to maintain various type of templates, we hope that you will contribute there too. Templates are provided in hopes that these will be useful and will allow everyone to build their own templates for the scanner. Checkout the templating guide at nuclei.projectdiscovery.io for a primer on nuclei templates.
Resources
Features
- Simple and modular code base making it easy to contribute.
- Fast And fully configurable using a template based engine.
- Handles edge cases doing retries, backoffs etc for handling WAFs.
- Smart matching functionality for zero false positive scanning.
Usage
nuclei -h
This will display help for the tool. Here are all the switches it supports.
| Flag | Description | Example |
|---|---|---|
| -c | Number of concurrent requests (default 10) | nuclei -c 100 |
| -l | List of urls to run templates | nuclei -l urls.txt |
| -target | Target to scan using templates | nuclei -target hxxps://example.com |
| -t | Templates input file/files to check across hosts | nuclei -t git-core.yaml |
| -t | Templates input file/files to check across hosts | nuclei -t nuclei-templates/cves/ |
| -nC | Don't Use colors in output | nuclei -nC |
| -json | Prints and write output in json format | nuclei -json |
| -json-requests | Write requests/responses for matches in JSON output | nuclei -json -json-requests |
| -o | File to save output result (optional) | nuclei -o output.txt |
| -pbar | Enable the progress bar (optional) | nuclei -pbar |
| -silent | Show only found results in output | nuclei -silent |
| (except when using with pbar) | ||
| -retries | Number of times to retry a failed request (default 1) | nuclei -retries 1 |
| -timeout | Seconds to wait before timeout (default 5) | nuclei -timeout 5 |
| -rl | Rate-Limit of requests per specified target | nuclei -rl 100 |
| -severity | Filter templates based on their severity and only run the matching ones | nuclei -severity critical, low |
| -exclude | Template input dir/file/files to exclude | nuclei -exclude panels, tokens |
| -debug | Allow debugging of request/responses. | nuclei -debug |
| -update-templates | Download and updates nuclei templates | nuclei -update-templates |
| -update-directory | Directory for storing nuclei-templates(optional) | nuclei -update-directory templates |
| -tl | List available templates | nuclei -tl |
| -v | Shows verbose output of all sent requests | nuclei -v |
| -version | Show version of nuclei | nuclei -version |
| -proxy-url | Proxy URL | nuclei -proxy-url hxxp://127.0.0.1:8080 |
| -proxy-socks-url | Socks proxy URL | nuclei -proxy-socks-url socks5://127.0.0.1:8080 |
| -H | Custom Header | nuclei -H "x-bug-bounty: hacker" |
Installation Instructions
From Binary
The installation is easy. You can download the pre-built binaries for your platform from the Releases page. Extract them using tar, move it to your $PATHand you're ready to go.
Download latest binary from https://github.com/projectdiscovery/nuclei/releases
▶ tar -xzvf nuclei-linux-amd64.tar.gz
▶ mv nuclei /usr/local/bin/
▶ nuclei -version
From Source
nuclei requires go1.14+ to install successfully. Run the following command to get the repo -
▶ GO111MODULE=on go get -u -v github.com/projectdiscovery/nuclei/v2/cmd/nuclei
From Github
▶ git clone https://github.com/projectdiscovery/nuclei.git; cd nuclei/v2/cmd/nuclei/; go build; mv nuclei /usr/local/bin/; nuclei -h
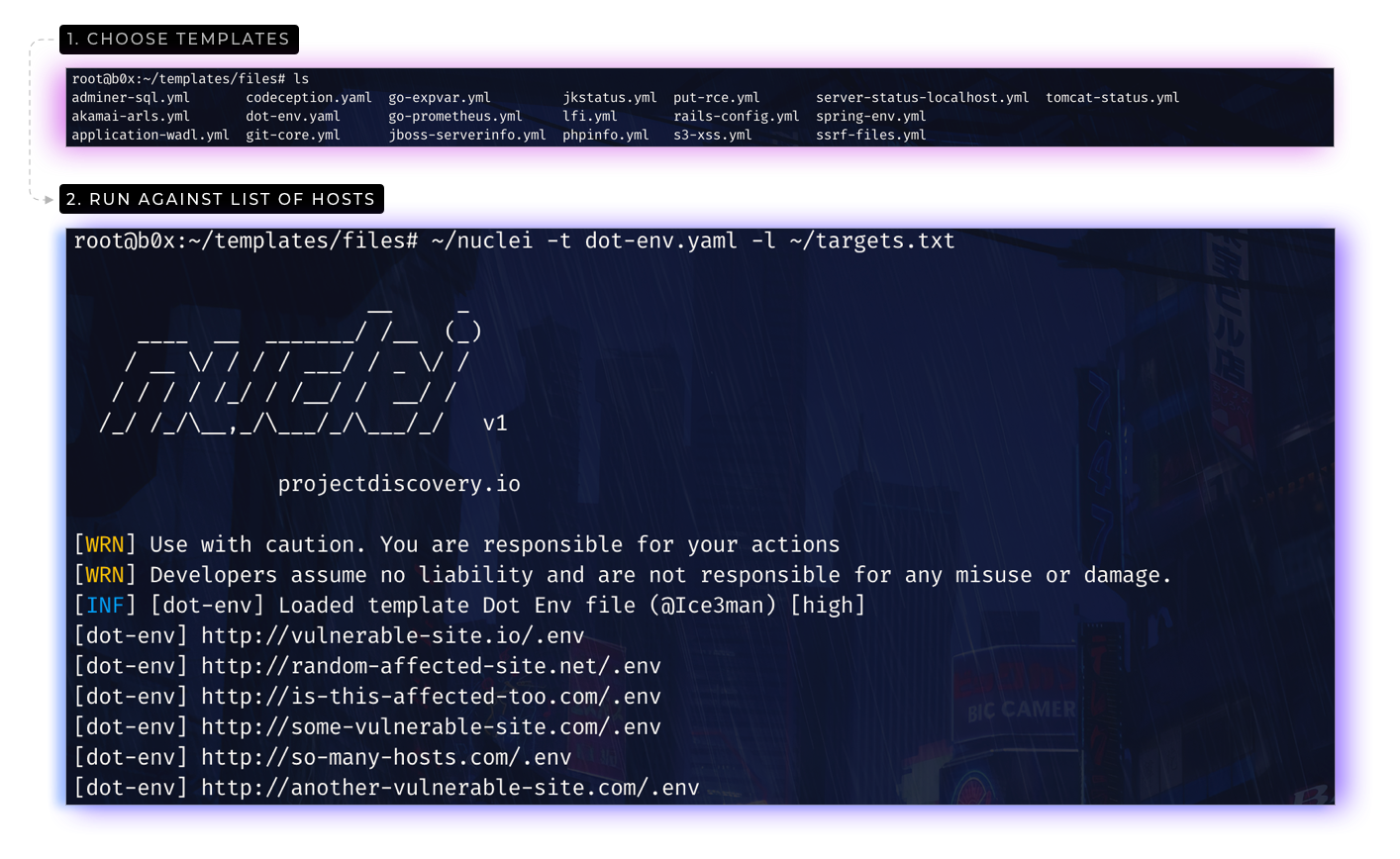
Nuclei templates
You can download or update the nuclei templates using update-templates flag.
▶ nuclei -update-templates
or download it from nuclei templates Github project.
▶ git clone https://github.com/projectdiscovery/nuclei-templates.git
Please refer to nuclei templating guide to writing your own custom templates.
Running nuclei
Running with single template.
This will run git-core.yaml template against all the hosts in urls.txt and returns the matched results.
▶ nuclei -l urls.txt -t files/git-core.yaml -o results.txt
You can also pass the list of urls at standard input (STDIN). This allows for easy integration in automation pipelines.
▶ cat urls.txt | nuclei -t files/git-core.yaml -o results.txt
Running with multiple templates.
This will run the tool against all the urls in urls.txt with all the templates in the cves and files directory and returns the matched results.
▶ nuclei -l urls.txt -t cves/ -t files/ -o results.txt
Running with subfinder.
▶ subfinder -d hackerone.com -silent | httpx -silent | nuclei -t cves/ -o results.txt
Running in Docker container
You can use the nuclei dockerhub image. Simply run -
▶ docker pull projectdiscovery/nuclei
After downloading or building the container, run the following:
▶ docker run -it projectdiscovery/nuclei
For example, this will run the tool against all the hosts in urls.txt and output the results to your host file system:
▶ cat urls.txt | docker run -v /path/to/nuclei-templates:/app/nuclei-templates -v /path/to/nuclei/config:/app/.nuclei-config.json -i projectdiscovery/nuclei -t ./files/git-config.yaml > results.txt
Remember to change /path-to-nuclei-templates to the real path on your host file system.
Thanks
nuclei is made with 🖤 by the projectdiscovery team. Community contributions have made the project what it is. See the Thanks.md file for more details.
Do also check out these similar awesome projects that may fit in your workflow:
Burp Suite, FFuF, Jaeles, Qsfuzz, Inception, Snallygaster, Gofingerprint, Sn1per, Google tsunami, ChopChop