# Analysis of the new TA505 campaign
## Table of Contents
* [Malware analysis](#Malware-analysis)
* [Cyber Threat Intel](#Cyber-Threat-Intel)
* [Cyber kill chain](#Cyber-kill-chain)
* [Indicators Of Compromise (IOC)](#IOC)
* [References MITRE ATT&CK Matrix](#Ref-MITRE-ATTACK)
* [Links](#Links)
+ [Original Tweet](#Original-Tweet)
+ [Link Anyrun](#Links-Anyrun)
## Malware analysis
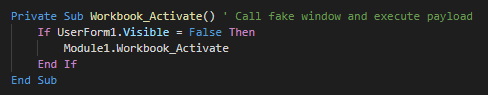
###### The initial vector is a malicious excel file which used an XLM macro (macro v4). This uses a function for launch the payload when the excel windows is active (selected as primary window). As first action, this executes the module 1.
## Cyber Threat Intel
######
## Cyber kill chain
###### The process graphs resume all the cyber kill chains used by the attacker.
![alt text]()
## References MITRE ATT&CK Matrix
###### List of all the references with MITRE ATT&CK Matrix
|Enterprise tactics|Technics used|Ref URL|
| :---------------: |:-------------| :------------- |
||||
## Indicators Of Compromise (IOC)
###### List of all the Indicators Of Compromise (IOC)
|Indicator|Description|
| ------------- |:-------------:|
|||
###### This can be exported as JSON format [Export in JSON]()
## Links
###### Original tweet:
* [https://twitter.com/Timele9527/status/1182587382626996224](https://twitter.com/Timele9527/status/1182587382626996224)
###### Links Anyrun:
* [Letter 7711.xls](https://app.any.run/tasks/7cdd1bfc-f0a3-4dd6-a29c-5ed70a77e76c)
###### Ressources:
* [DotNetToJScript](https://github.com/tyranid/DotNetToJScript)