# Neutrino physics 101
## Table of Contents
* [Malware analysis](#Malware-analysis)
+ [The initial vector](#Initial)
+ [Loader](#loader)
* [Threat Intelligence](#Intel)
+ [](#Sub_Intel)
* [Cyber kill chain](#Cyber-kill-chain)
* [Indicators Of Compromise (IOC)](#IOC)
* [Yara Rules](#Yara)
* [References MITRE ATT&CK Matrix](#Ref-MITRE-ATTACK)
* [Links](#Links)
+ [Original Tweet](#tweet)
+ [Link Anyrun](#Links-Anyrun)
+ [Ressources](#Ressources)
Malware analysis
The initial vector
The initial vector is an malicious document using a macro. As the first look, we can note some constant variables can be replace and deletefor improvement the reading of the code.
``` VBA
Private Const HHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHOneMask = 16515072
Private Const HHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHTwoMask = 258048
Private Const HHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHThreeMask = 4032
Private Const HHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHFourMask = 63
Private Const HHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHighMask = 16711680
Private Const HHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHMidMask = 65280
Private Const HHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHHLowMask = 255
Private Const MNAJSAQQQQQQ18 = 262144
Private Const MNAJSAQQQQQQ12 = 4096
Private Const MNAJSAQQQQQQ6 = 64
Private Const MNAJSAQQQQQQ8 = 256
Private Const MNAJSAQQQQQQ16 = 65536
```
We can see the both functions for auto-open the macro in the reading of the document for the Word and Excel document. This is for a common code for the both vectors or for reduce the rate of the detection, hard to say it.
``` VBA
Sub AutoOpen()
AddSpace
End Sub
Private Sub Workbook_Open()
AddSpace
End Sub
```
![]()
Threat Intelligence
Cyber kill chain
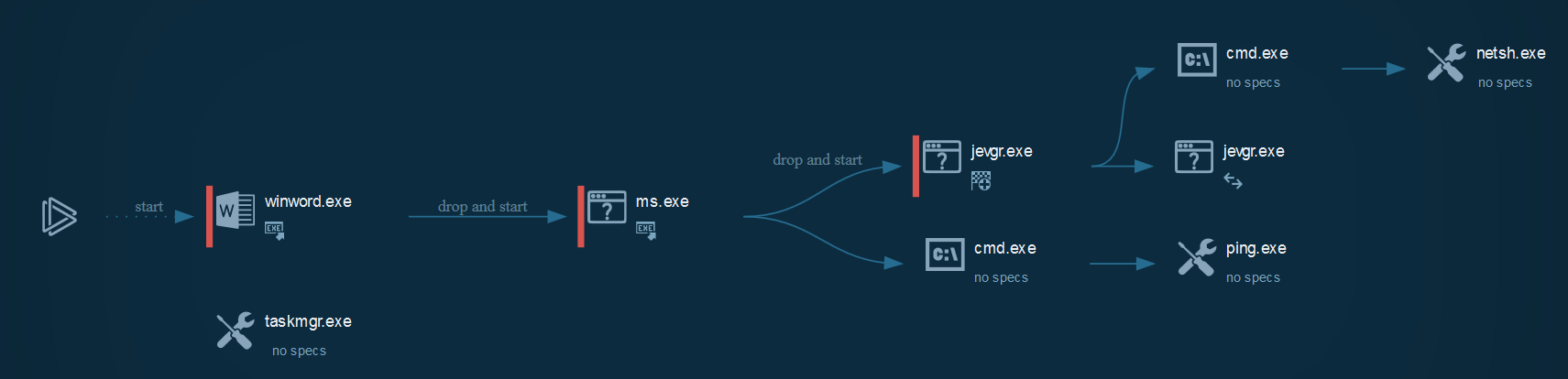
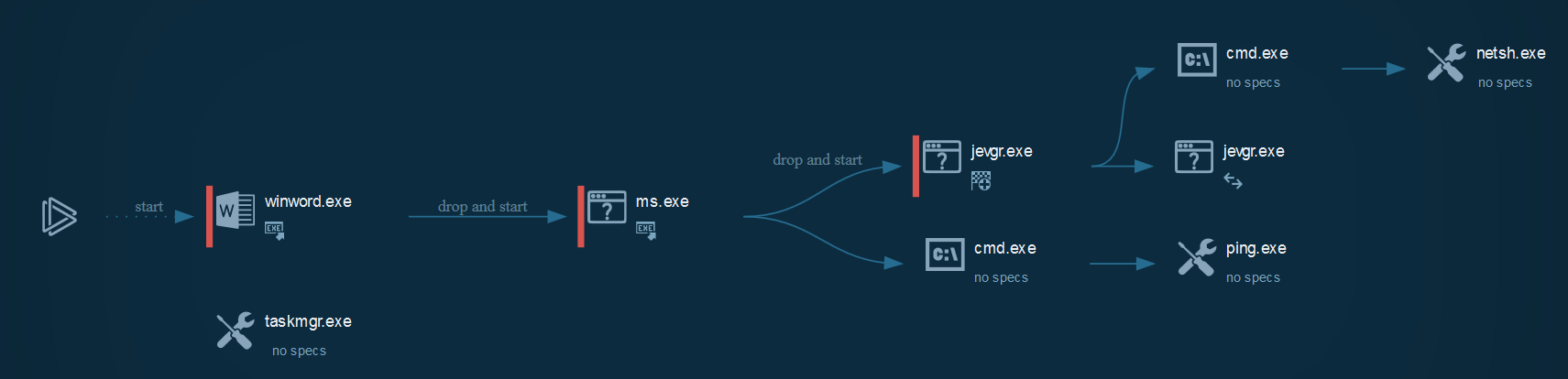
The process graph resume cyber kill chains used by the attacker :
Indicators Of Compromise (IOC)
List of all the Indicators Of Compromise (IOC)
|Indicator|Description|
| ------------- |:-------------:|
The IOC can be exported in JSON
References MITRE ATT&CK Matrix
|Enterprise tactics|Technics used|Ref URL|
| :---------------: |:-------------| :------------- |
This can be exported as JSON format
Yara Rules
YARA Rules are available here
Links
Original tweet:
* [https://twitter.com/JAMESWT_MHT/status/1225796259845414912](https://twitter.com/JAMESWT_MHT/status/1225796259845414912)
Links Anyrun:
* [impor.doc](https://app.any.run/tasks/454fe6a2-e2d0-4fa3-ba1d-78e2c7372ddd)
Resources :
* [Encode64 / Decode64 in VB.NET](https://stackoverflow.com/questions/12879661/encode64-decode64-in-vb-net)
* [New Neutrino Bot comes in a protective loader](https://blog.malwarebytes.com/threat-analysis/2017/02/new-neutrino-bot-comes-in-a-protective-loader/)
* [URLhaus Neutrino](https://urlhaus.abuse.ch/browse/tag/Neutrino/)
* [VB2019 paper: Rich Headers: leveraging this mysterious artifact of the PE format](https://www.virusbulletin.com/virusbulletin/2020/01/vb2019-paper-rich-headers-leveraging-mysterious-artifact-pe-format/)