11 lines
765 B
Markdown
11 lines
765 B
Markdown
|
|
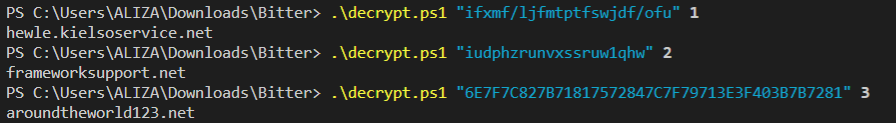
## Tool for decoding the encoded strings of ArtraDownloader
|
||
|
|
##### This tool decoding the encoded strings of the three variants of ArtraDownloader used by the APT Bitter group (August 2019)
|
||
|
|
##### The following syntax is the next :
|
||
|
|
```sh
|
||
|
|
> decrypt.ps1 "[Encoded string]" [Num Variant]
|
||
|
|
```
|
||
|
|
##### This will be give you the following result :
|
||
|
|
|
||
|
|
##### URL Tool : https://github.com/StrangerealIntel/CyberThreatIntel/blob/master/offshore%20APT%20organization/Bitter/27-08-19/decrypt/decrypt.ps1
|
||
|
|
##### Ref Analysis: https://unit42.paloaltonetworks.com/multiple-artradownloader-variants-used-by-bitter-to-target-pakistan/
|